GITNUXSOFTWARE ADVICE
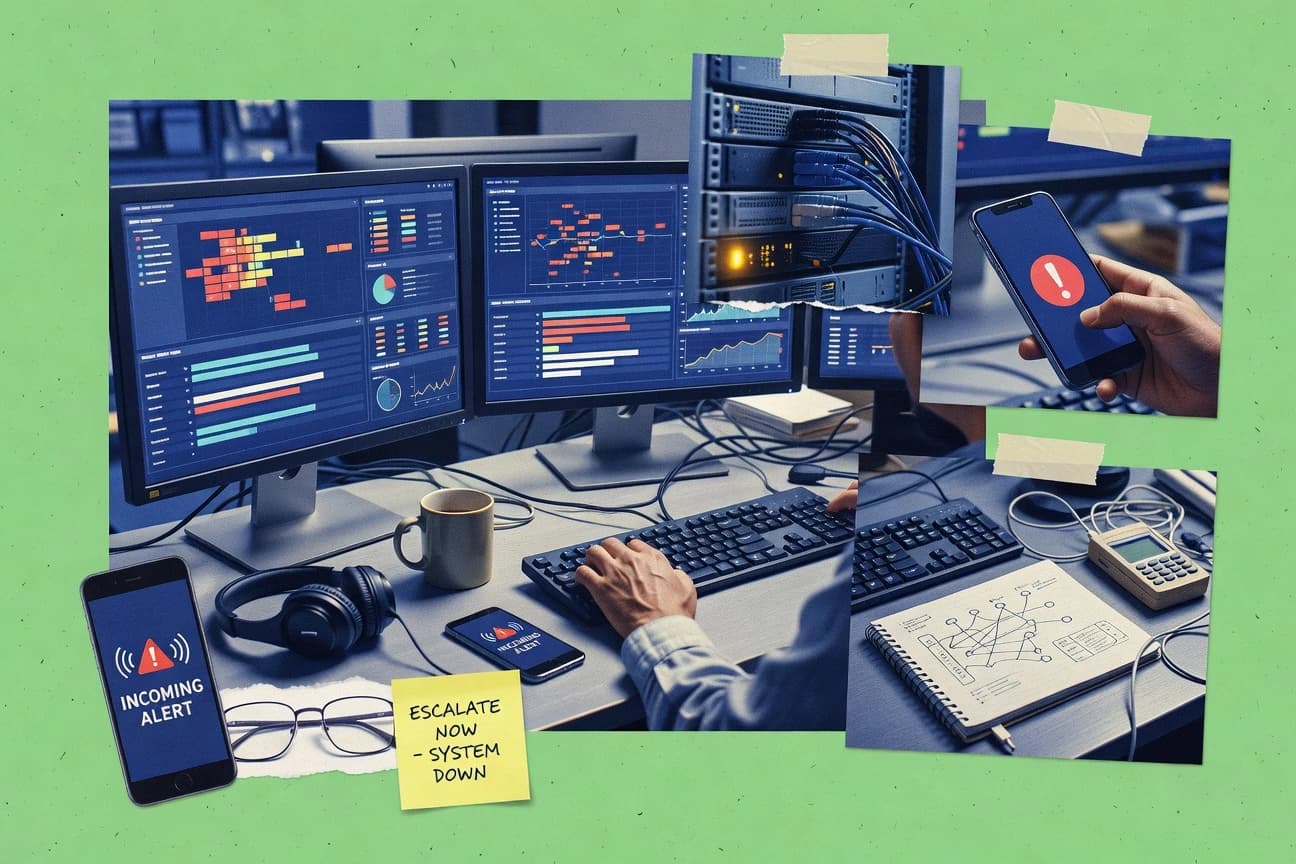
Business FinanceTop 10 Best Incident Software of 2026
Discover the top 10 incident software solutions. Compare features, evaluate tools, and find the best fit. Click to learn more.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
PagerDuty
Incident orchestration with escalation policies and automation rules tied to acknowledgements
Built for enterprises and scaling teams that need automated, auditable incident response workflows.
Atlassian Opsgenie
Alert routing with escalation policies and on-call scheduling across teams
Built for teams using Jira and needing automated alert routing with disciplined on-call workflows.
ServiceNow Incident Management
CMDB-driven incident context for smarter assignment, impact analysis, and faster resolution
Built for enterprise IT teams standardizing incident workflows with SLAs and CMDB context.
Related reading
Comparison Table
This comparison table reviews major incident management tools, including PagerDuty, Atlassian Opsgenie, ServiceNow Incident Management, Datadog Incident Management, and Splunk IT Service Intelligence. It highlights how each platform handles alerting, incident workflows, routing and escalation, integrations with monitoring and ITSM systems, and reporting. Use the table to quickly narrow down which solution fits your operational model and toolchain.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | PagerDuty PagerDuty orchestrates incident response with alert routing, on-call scheduling, escalation policies, and automated workflows across monitoring, ITSM, and cloud systems. | enterprise orchestration | 9.3/10 | 9.4/10 | 8.7/10 | 8.6/10 |
| 2 | Atlassian Opsgenie Opsgenie provides alert management, on-call scheduling, incident collaboration, and escalation workflows that integrate with monitoring tools and Jira. | enterprise incident management | 8.6/10 | 9.1/10 | 8.2/10 | 7.9/10 |
| 3 | ServiceNow Incident Management ServiceNow supports incident workflows with ticketing, automated assignment, knowledge integration, and deep integrations across ITSM and operations tools. | ITSM suite | 8.6/10 | 9.2/10 | 7.8/10 | 7.9/10 |
| 4 | Datadog Incident Management Datadog centralizes alerts into incident workflows with alert grouping, timeline context, collaboration, and integrations for alerting and automation. | monitoring-native | 8.1/10 | 8.7/10 | 7.6/10 | 7.5/10 |
| 5 | Splunk IT Service Intelligence Splunk IT Service Intelligence ties machine data to service impact with incident correlation, event analytics, and operational intelligence for troubleshooting. | observability intelligence | 7.9/10 | 8.3/10 | 7.1/10 | 7.4/10 |
| 6 | VictorOps (Moogsoft Incident Response) Moogsoft provides incident response with AI-driven event correlation to reduce alert noise and accelerate triage across monitoring sources. | AIOps correlation | 7.6/10 | 8.1/10 | 7.3/10 | 6.8/10 |
| 7 | Moogsoft AIOps Moogsoft aggregates and correlates events into actionable incidents with automated analysis and operational workflows. | AIOps platform | 7.4/10 | 8.3/10 | 6.9/10 | 6.8/10 |
| 8 | Jira Service Management Jira Service Management manages incidents through configurable workflows, service requests, SLAs, and integrations with monitoring and collaboration tools. | ticketing-first | 8.0/10 | 8.6/10 | 7.4/10 | 7.6/10 |
| 9 | Freshservice Incident Management Freshservice enables incident tracking with ITIL-aligned workflows, asset context, automation rules, and reporting for IT operations teams. | SMB ITSM | 7.2/10 | 8.1/10 | 7.4/10 | 6.8/10 |
| 10 | OpsHub OpsHub provides alert routing, on-call schedules, incident timelines, and escalation automation for operational incident response teams. | on-call automation | 7.2/10 | 7.4/10 | 7.0/10 | 7.6/10 |
PagerDuty orchestrates incident response with alert routing, on-call scheduling, escalation policies, and automated workflows across monitoring, ITSM, and cloud systems.
Opsgenie provides alert management, on-call scheduling, incident collaboration, and escalation workflows that integrate with monitoring tools and Jira.
ServiceNow supports incident workflows with ticketing, automated assignment, knowledge integration, and deep integrations across ITSM and operations tools.
Datadog centralizes alerts into incident workflows with alert grouping, timeline context, collaboration, and integrations for alerting and automation.
Splunk IT Service Intelligence ties machine data to service impact with incident correlation, event analytics, and operational intelligence for troubleshooting.
Moogsoft provides incident response with AI-driven event correlation to reduce alert noise and accelerate triage across monitoring sources.
Moogsoft aggregates and correlates events into actionable incidents with automated analysis and operational workflows.
Jira Service Management manages incidents through configurable workflows, service requests, SLAs, and integrations with monitoring and collaboration tools.
Freshservice enables incident tracking with ITIL-aligned workflows, asset context, automation rules, and reporting for IT operations teams.
OpsHub provides alert routing, on-call schedules, incident timelines, and escalation automation for operational incident response teams.
PagerDuty
enterprise orchestrationPagerDuty orchestrates incident response with alert routing, on-call scheduling, escalation policies, and automated workflows across monitoring, ITSM, and cloud systems.
Incident orchestration with escalation policies and automation rules tied to acknowledgements
PagerDuty stands out with deeply configurable incident lifecycles and routing that keep on-call response consistent across complex teams. Core capabilities include real-time alerts from integrations, escalation policies, acknowledgements, and incident timelines for investigation. It also supports post-incident reviews, automation workflows, and comprehensive reporting to track reliability and reduce repeat incidents.
Pros
- Highly configurable escalation policies with flexible routing logic
- Strong incident timeline and audit trail for investigation
- Automation workflows reduce manual triage and routing work
- Broad alert integration coverage across monitoring and ticketing tools
- Detailed reporting supports reliability metrics and ongoing improvement
Cons
- Advanced configuration can feel heavy for small teams
- Automation setup takes time to model real on-call workflows
- Costs scale quickly with high alert volumes and multiple teams
- UI navigation across complex workflows can slow first-time administrators
Best For
Enterprises and scaling teams that need automated, auditable incident response workflows
More related reading
Atlassian Opsgenie
enterprise incident managementOpsgenie provides alert management, on-call scheduling, incident collaboration, and escalation workflows that integrate with monitoring tools and Jira.
Alert routing with escalation policies and on-call scheduling across teams
Opsgenie stands out for its automated alert routing and on-call scheduling tightly integrated with Atlassian products like Jira. It supports escalation policies, incident collaboration, and alert suppression to reduce noisy paging. The platform adds practical response tooling through incident timelines, mass notifications, and duplication controls across multiple sources. It also emphasizes governance features like audit logs and configurable notification rules for teams that manage complex operations.
Pros
- Advanced escalation policies with flexible routing across teams and schedules
- Strong on-call management with handoffs, rotations, and escalation timing controls
- Deep incident collaboration linked to Jira for triage and follow-up
- Built-in alert suppression and de-duplication to reduce alert fatigue
- Multiple notification channels including email, SMS, and mobile push
Cons
- Setup effort increases with complex routing and multi-team escalation rules
- Higher administrative overhead than lightweight incident tools
- Costs can rise quickly when alert volume and user seats expand
- Integrations require careful configuration for consistent incident timelines
Best For
Teams using Jira and needing automated alert routing with disciplined on-call workflows
ServiceNow Incident Management
ITSM suiteServiceNow supports incident workflows with ticketing, automated assignment, knowledge integration, and deep integrations across ITSM and operations tools.
CMDB-driven incident context for smarter assignment, impact analysis, and faster resolution
ServiceNow Incident Management centers on IT workflows that connect incident intake, triage, and resolution to broader ITSM processes in a single system. It supports configurable assignment rules, SLAs, task generation, and escalation management to keep incidents progressing with measurable targets. Integration with Service Catalog, Problem Management, Change Management, and CMDB lets teams route incidents with context and reduce repeat failures. Reporting and automation capabilities make it strong for enterprise incident operations and cross-team coordination.
Pros
- Deep ITSM integration links incidents to problems, changes, and service catalog
- Strong SLA, escalation, and workflow automation for consistent incident handling
- CMDB-backed context improves routing, impact analysis, and troubleshooting efficiency
- Robust reporting supports operational metrics like MTTR, backlog, and SLA attainment
Cons
- Complex configuration and data modeling increases time to first effective rollout
- Licensing and implementation costs can be heavy for smaller teams
- Admin overhead is high for large-scale workflow customization and governance
- Non-IT incident use cases may require additional configuration effort
Best For
Enterprise IT teams standardizing incident workflows with SLAs and CMDB context
More related reading
Datadog Incident Management
monitoring-nativeDatadog centralizes alerts into incident workflows with alert grouping, timeline context, collaboration, and integrations for alerting and automation.
Incident timelines that compile alert context, updates, and ownership into a single response record
Datadog Incident Management stands out for tying incident workflows to live observability signals from Datadog monitors and events. It supports incident timelines, status updates, and collaboration in a structured workflow that reduces time spent coordinating across teams. Escalation paths integrate with alerting so responders can route incidents by severity and ownership without manual triage steps. It also connects with post-incident review outputs to keep action items linked to the incidents that created them.
Pros
- Automatic incident creation from Datadog alerts with severity and ownership context
- Timeline and status management streamline incident communication for many responders
- Integrations with alerting and notification channels reduce manual escalation work
- Post-incident reviews keep action items connected to incident history
Cons
- Best results require strong Datadog monitor setup and alert hygiene
- Advanced workflow configuration can feel complex for teams without observability tooling
- Cost grows with Datadog usage even if incident workflow value is modest
Best For
Teams already standardized on Datadog who need workflow-driven incident response
Splunk IT Service Intelligence
observability intelligenceSplunk IT Service Intelligence ties machine data to service impact with incident correlation, event analytics, and operational intelligence for troubleshooting.
Event correlation that turns Splunk-detected anomalies into actionable incident context
Splunk IT Service Intelligence stands out by connecting IT operations data to incident workflows using Splunk’s search, monitoring, and analytics foundation. It supports event correlation, incident creation, and case-based investigation with timelines that trace signals across tools. Strong dashboards and alerting help teams standardize response for IT service issues. Integration breadth with common monitoring and ITSM systems improves incident context and reduces manual enrichment.
Pros
- Advanced correlation using Splunk search and machine learning for incident triage
- Case timelines unify logs, metrics, and events for faster root-cause analysis
- Automation connects alerts to incident records across IT operations sources
Cons
- Setup and tuning require Splunk expertise and ongoing configuration effort
- Incident workflow customization can be heavy for teams needing simple runs
- Licensing and implementation costs can outweigh value for small incident volumes
Best For
Enterprises standardizing incident triage with Splunk-driven observability and IT data
VictorOps (Moogsoft Incident Response)
AIOps correlationMoogsoft provides incident response with AI-driven event correlation to reduce alert noise and accelerate triage across monitoring sources.
Automated alert aggregation for incident correlation and duplicate suppression
VictorOps is distinct for its incident response workflow built around alert correlation and automated notification routing from Moogsoft Incident Response. It focuses on reducing duplicate incidents through event aggregation and then speeding response with guided runbooks, escalation policies, and after-action timelines. The solution also supports team collaboration by connecting incidents to operational context from monitoring and service data. VictorOps is strongest when you want correlated, actionable incidents instead of individual alert noise.
Pros
- Alert correlation reduces duplicate incidents from noisy monitoring signals
- Escalation policies and notification routing speed time to acknowledgement
- Incident timelines improve post-incident analysis and handoffs
Cons
- Setup and tuning require strong operational knowledge
- Workflow depth can feel heavy for smaller teams and fewer alerts
- Licensing costs can outweigh value for organizations with simple monitoring
Best For
Operations teams needing correlated incident workflows and escalation automation
More related reading
Moogsoft AIOps
AIOps platformMoogsoft aggregates and correlates events into actionable incidents with automated analysis and operational workflows.
AI-driven event correlation that automatically deduplicates and clusters related alerts into incidents
Moogsoft AIOps stands out for using AI-driven event correlation to reduce alert noise and automatically group related incidents across tools. It supports incident lifecycle workflows with case management, assignment, and collaboration so teams can resolve issues from a single operational view. It also integrates with monitoring, IT service management, and ticketing to feed incidents with context and to push resolved outcomes downstream. For incident software, its strength is speeding triage and investigation through unified timelines and automated recommendations.
Pros
- AI event correlation groups noisy alerts into actionable incident clusters
- Incident workflows include case creation, ownership, and resolution tracking
- Unified timelines combine telemetry, alerts, and supporting context for faster triage
- Integrates with monitoring and ticketing systems to sync incident state
- Automation recommendations reduce manual investigation steps
Cons
- Setup and tuning correlation rules can take significant effort
- UI navigation can feel complex for teams using only basic alerting
- Licensing and deployment costs can strain smaller incident teams
- Advanced use often requires skilled administrators and data pipeline knowledge
Best For
Enterprises consolidating incidents across monitoring tools and ITSM workflows
Jira Service Management
ticketing-firstJira Service Management manages incidents through configurable workflows, service requests, SLAs, and integrations with monitoring and collaboration tools.
SLA-driven incident management with automated routing and escalation
Jira Service Management stands out with incident management built on the same Jira issue model your teams already use. It supports ITIL-style service management with incident workflows, SLAs, and automated routing to the right support teams. For operations that need audit trails and tight coordination, it integrates incident work with knowledge articles and service request handling. Its on-call and escalation options connect service desks to responders, but advanced incident tooling depends on add-ons and careful configuration.
Pros
- Strong incident workflows with SLA targets and escalation paths
- Tight alignment with Jira issues for engineering collaboration
- Automation for triage, routing, and status updates reduces manual work
- Built-in audit history supports compliance and post-incident reviews
Cons
- Setup of workflows, SLAs, and automation can be time-consuming
- Incident command capabilities feel less specialized than dedicated incident platforms
- Some advanced alerting and incident features require additional tooling
Best For
Teams using Jira who need SLA-driven incident triage and cross-team collaboration
More related reading
Freshservice Incident Management
SMB ITSMFreshservice enables incident tracking with ITIL-aligned workflows, asset context, automation rules, and reporting for IT operations teams.
Incident SLAs with impact-based prioritization and automated breach workflows
Freshservice Incident Management stands out with tight integration between incident workflows and broader IT service management modules in the Freshworks suite. It provides ticket-based incident tracking with automation, service impact prioritization, and SLAs that help teams coordinate faster response. Built-in problem management links recurring incidents to root-cause work, and reporting supports operational reviews across teams. Custom fields and views help shape workflows without heavy configuration for common IT operations.
Pros
- Incident workflows connect with service management and problem management tasks
- Automation rules handle routing, reassignment, and status changes at scale
- SLA tracking and impact-based prioritization reduce response-time drift
- Reports show incident volume, resolution trends, and SLA performance
- Custom fields and views support tailored operations without coding
Cons
- Advanced configuration can feel complex compared with simpler incident tools
- Value drops for teams needing incident features without broader ITSM modules
- Some integrations and automation patterns require deeper setup effort
Best For
IT teams running ITSM with incident-to-problem workflows and SLA governance
OpsHub
on-call automationOpsHub provides alert routing, on-call schedules, incident timelines, and escalation automation for operational incident response teams.
Incident timeline builder with structured responder actions and resolution follow-ups
OpsHub stands out with incident-focused workflow automation that ties response steps to real-time status updates. It supports assigning responders, tracking incident timelines, and coordinating communications through structured incident records. The platform is built for operational continuity by linking incidents to knowledge, follow-ups, and resolution outcomes. Teams use it to reduce response chaos and standardize post-incident actions.
Pros
- Incident workflows reduce manual coordination during high-pressure events
- Structured incident timelines improve auditability of actions taken
- Responder assignments stay attached to each incident record
- Post-incident follow-ups help convert incidents into repeatable fixes
Cons
- Setup complexity can slow teams that need quick onboarding
- Limited advanced automation depth compared with top-tier incident suites
- Reporting customization takes effort for metrics-driven organizations
Best For
Operations teams needing standardized incident workflows and follow-up tracking
Conclusion
After evaluating 10 business finance, PagerDuty stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Incident Software
This buyer’s guide shows how to choose incident software by mapping core needs like alert routing, escalation workflows, incident timelines, and ITSM context to specific tools like PagerDuty, Atlassian Opsgenie, and ServiceNow Incident Management. It also compares correlation-first platforms like VictorOps and Moogsoft AIOps against workflow-first options like Jira Service Management, Freshservice, and OpsHub.
What Is Incident Software?
Incident software coordinates detection to resolution by collecting alerts, creating a structured incident record, assigning responders, and driving escalation through a defined lifecycle. It solves the coordination gap between monitoring signals and accountable action by recording who acknowledged, what happened next, and which follow-ups were created. Teams use these systems to reduce time spent chasing context across tools and to improve operational metrics like MTTR and SLA attainment. PagerDuty and Atlassian Opsgenie demonstrate this pattern with alert routing, on-call scheduling, escalation policies, and auditable incident timelines.
Key Features to Look For
The right incident platform turns alert noise into a controlled workflow with accountable handoffs, consistent routing, and investigation-ready context.
Incident orchestration with escalation policies and acknowledgements
PagerDuty excels at incident orchestration with escalation policies and automation rules tied to acknowledgements, so response actions follow a repeatable playbook. OpsHub also emphasizes assigning responders to each incident record and converting incident activity into structured follow-ups.
On-call scheduling and disciplined alert routing
Atlassian Opsgenie provides advanced escalation policies with flexible routing across teams and schedules, plus on-call handoffs with escalation timing controls. Jira Service Management supports escalation paths inside Jira workflows, which keeps routing tied to the same issue model used by engineering and support teams.
Incident timelines that compile alert context and ownership
Datadog Incident Management builds incident timelines that compile alert context, updates, and ownership into a single response record. PagerDuty also delivers a strong incident timeline and audit trail for investigation, which helps teams understand exactly how the incident progressed.
CMDB-driven context and ITSM workflow automation
ServiceNow Incident Management links incidents to broader ITSM processes using CMDB-backed context for smarter assignment and impact analysis. Freshservice connects incident workflows with service management and problem management tasks, which supports incident-to-problem links for recurring failures.
AI-driven event correlation and automated duplicate suppression
VictorOps applies automated alert aggregation for incident correlation and duplicate suppression, which reduces noisy monitoring signals into actionable incidents. Moogsoft AIOps extends the same concept by using AI-driven event correlation to deduplicate and cluster related alerts into incidents.
Correlation-first investigation across logs, metrics, and events
Splunk IT Service Intelligence turns Splunk-detected anomalies into actionable incident context using event correlation. It then provides case timelines that unify logs, metrics, and events to speed root-cause analysis when multiple signal sources drive the incident.
How to Choose the Right Incident Software
Pick the platform that matches how your organization creates context during incidents, either from observability signals, ITSM assets, or structured operational workflows.
Start with your incident source of truth for context
If your incidents originate from Datadog alerts, choose Datadog Incident Management because it ties incident workflows to live Datadog monitor and event signals and compiles alert context into incident timelines. If your incidents originate from Splunk anomalies, choose Splunk IT Service Intelligence because it uses event correlation and case timelines to unify logs, metrics, and events into a single investigation view.
Choose the routing model that matches your org structure
If you need complex, auditable routing across multiple teams with acknowledgements driving automated next steps, choose PagerDuty because it supports highly configurable escalation policies and flexible routing logic. If your team coordination is already anchored in Jira, choose Atlassian Opsgenie for alert routing and on-call scheduling integrated with Jira.
Decide how you will deduplicate noisy alerts into fewer incidents
If the biggest time sink is duplicate alert storms, choose VictorOps because it aggregates alerts into correlated incidents and suppresses duplicates. If you need broader clustering across multiple monitoring tools, choose Moogsoft AIOps because it uses AI-driven event correlation to automatically deduplicate and cluster related alerts into incident clusters.
Map incident resolution to the workflows your business already uses
If you run ITIL-style processes and need CMDB-backed assignment with SLAs, choose ServiceNow Incident Management because it integrates with Problem Management, Change Management, Service Catalog, and CMDB context. If your incident-to-problem loop lives in IT service management modules, choose Freshservice because it links recurring incidents to root-cause problem work and drives SLA-based incident breach workflows.
Validate lifecycle depth, audit needs, and administrator effort
If your enterprise requires deeply configurable incident lifecycles and automation tied to response events, choose PagerDuty because it provides a detailed incident audit trail and robust automation workflows. If your team needs a simpler standardized operational flow with structured timelines and follow-ups, choose OpsHub because it focuses on assigning responders, building incident timelines, and converting incidents into repeatable fixes.
Who Needs Incident Software?
Incident software fits organizations where alerts must become accountable actions across multiple responders, tools, and lifecycle steps.
Enterprises and scaling teams that need automated, auditable incident response workflows
PagerDuty fits this audience because incident orchestration uses escalation policies and automation rules tied to acknowledgements, and it maintains strong incident timelines for investigation. ServiceNow Incident Management also fits because it connects incident handling to SLAs, escalation management, and CMDB context for measurable operational outcomes.
Teams using Jira that need disciplined alert routing and engineering-friendly collaboration
Atlassian Opsgenie fits because it integrates alert routing and on-call scheduling with Jira and provides incident collaboration, mass notifications, and alert de-duplication. Jira Service Management fits because it runs incident workflows on the Jira issue model with SLA-driven escalation and audit history tied to the same work records engineers use.
Operations teams focused on reducing alert noise using correlation and duplicate suppression
VictorOps fits because it provides automated alert aggregation for incident correlation and duplicate suppression, and it accelerates acknowledgement through escalation routing. Moogsoft AIOps fits because it uses AI-driven correlation to automatically deduplicate and cluster related alerts into actionable incident groupings.
Organizations standardizing on observability platforms and want workflows built from their telemetry
Datadog Incident Management fits because it creates incident workflows from Datadog alert signals with incident timelines that compile alert context, updates, and ownership. Splunk IT Service Intelligence fits because it connects Splunk search and machine learning correlation to incident cases with unified case timelines across telemetry sources.
Common Mistakes to Avoid
These mistakes show up when teams select incident software that mismatches their incident sources, lifecycle depth, or operating model.
Buying a workflow platform without a clear routing and escalation design
PagerDuty and Atlassian Opsgenie succeed when escalation policies are modeled to match your on-call structure because acknowledgements and routing rules drive the workflow forward. OpsHub also provides structured timelines and assignments, but it has limited advanced automation depth compared with top-tier suites.
Ignoring alert hygiene and signal quality requirements
Datadog Incident Management delivers best results when Datadog monitor setup and alert hygiene are strong, because it builds incident workflows from Datadog signals. Splunk IT Service Intelligence also depends on usable Splunk-detected anomalies, because event correlation turns those signals into actionable incident context.
Overlooking configuration complexity that delays first effective rollout
ServiceNow Incident Management and Splunk IT Service Intelligence can require complex configuration and modeling effort, especially when SLAs, CMDB context, and workflow customization are deeply integrated. VictorOps and Moogsoft AIOps can also require tuning of correlation rules, which can slow onboarding if teams lack operational knowledge.
Treating incidents as single alerts instead of lifecycle-managed cases
VictorOps and Moogsoft AIOps are built to correlate events into incident clusters so teams handle fewer, more actionable cases rather than independent alerts. PagerDuty and Datadog Incident Management also focus on incident timelines and audit trails, which keeps incident response tied to investigation-ready lifecycle history.
How We Selected and Ranked These Tools
We evaluated PagerDuty, Atlassian Opsgenie, ServiceNow Incident Management, Datadog Incident Management, Splunk IT Service Intelligence, VictorOps, Moogsoft AIOps, Jira Service Management, Freshservice, and OpsHub using overall capability fit, feature depth, ease of use, and value for operational teams. We separated PagerDuty from lower-ranked tools by focusing on how incident orchestration works end to end with escalation policies, flexible routing logic, and automation rules tied to acknowledgements, plus an incident timeline and audit trail built for investigation and reporting. We also scored tools higher when they connected incident workflows to the operational systems that supply context, such as CMDB integration in ServiceNow Incident Management, alert context compilation in Datadog Incident Management, and event correlation in Splunk IT Service Intelligence.
Frequently Asked Questions About Incident Software
Which incident software is best for routing and escalation across large, multi-team orgs?
PagerDuty is built for configurable incident lifecycles with escalation policies tied to acknowledgements, so the same response pattern runs across complex teams. Atlassian Opsgenie pairs automated alert routing with on-call scheduling and escalation policies, which helps teams reduce routing mistakes when ownership changes.
What tool is most effective at reducing alert noise using event correlation and deduplication?
Moogsoft AIOps uses AI-driven event correlation to cluster related alerts into incidents and speed triage from a unified view. VictorOps (Moogsoft Incident Response) also focuses on alert aggregation and duplicate suppression, then drives responders using escalation policies and guided runbooks.
Which platforms can turn incident workflows into auditable records for post-incident reviews?
PagerDuty includes incident timelines and post-incident reviews that connect investigation history to action items. Atlassian Opsgenie provides governance-oriented audit logs and configurable notification rules, and it keeps collaboration anchored to incident timelines.
How do I connect incident intake to ITSM processes like SLA tracking, problem management, and change workflows?
ServiceNow Incident Management links incident intake, triage, and resolution to ITSM modules like Problem Management, Change Management, and the CMDB. Freshservice Incident Management connects incident tickets to problem management for recurring incident root-cause work, with SLA-driven breach workflows.
Which incident software works best when your observability stack is already centered on Datadog monitors and events?
Datadog Incident Management ties incident timelines, status updates, and collaboration directly to live signals from Datadog monitors and events. It integrates escalation paths with alerting so severity and ownership routing happens without manual triage steps.
What options are strongest for correlating and investigating incidents using searchable operational data?
Splunk IT Service Intelligence connects IT operations data to incident creation using Splunk search, monitoring, and analytics. It supports event correlation so anomalies across tools become a single case with a timeline for investigation.
Which tool is best if your teams already manage work in Jira and want consistent incident tracking using the Jira issue model?
Jira Service Management runs incident management on the same Jira issue model teams use for other work. It supports ITIL-style incident workflows, SLA-driven routing, and cross-team coordination with audit trails, knowledge articles, and service request handling.
What incident software is designed to structure communications and next steps as part of the incident record?
OpsHub is designed around structured incident records that track responder assignments, incident timelines, and coordinated communications. It also links incidents to knowledge, follow-ups, and resolution outcomes to standardize post-incident actions.
How do I avoid repeated manual enrichment when creating incidents from multiple alert sources and systems?
VictorOps (Moogsoft Incident Response) aggregates signals and suppresses duplicates so responders deal with fewer, more actionable incidents. Moogsoft AIOps and Datadog Incident Management also compile alert context into incident timelines and route responders by severity and ownership, which reduces the need for manual lookups.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Business Finance alternatives
See side-by-side comparisons of business finance tools and pick the right one for your stack.
Compare business finance tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
