GITNUXSOFTWARE ADVICE
SecurityTop 10 Best Access Governance Software of 2026
Discover the top 10 access governance software solutions. Compare features, pick the best fit for your business. Get actionable insights now.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
SailPoint IdentityAI
IdentityAI governance assistance for risk-driven access reviews and remediation guidance
Built for large enterprises needing AI-accelerated access governance and certification automation.
Oracle Identity Governance
Automated access certification with policy-based evidence capture for compliance reporting
Built for enterprises standardizing access governance across Oracle and non-Oracle apps.
CyberArk Identity Governance
Identity Certification campaigns with configurable attestations and comprehensive audit reporting
Built for enterprises governing privileged and application access across many systems.
Related reading
Comparison Table
This comparison table evaluates access governance software across identity and entitlement lifecycle controls, including role mining, policy enforcement, and access request workflows. You can compare products such as SailPoint IdentityAI, Oracle Identity Governance, CyberArk Identity Governance, Microsoft Entra Entitlement Management, and Okta Identity Governance by capability focus so you can map each tool to your governance and compliance requirements.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | SailPoint IdentityAI Automates identity governance for enterprise access management with AI-assisted risk analytics, recertification, and policy-based workflows. | enterprise | 9.3/10 | 9.5/10 | 7.8/10 | 8.4/10 |
| 2 | Oracle Identity Governance Governs user access with automated workflows for access requests, role mining, certification, and policy enforcement across enterprise apps. | enterprise | 8.3/10 | 9.0/10 | 7.4/10 | 7.6/10 |
| 3 | CyberArk Identity Governance Provides access governance with certification, segregation-of-duties controls, privileged access workflows, and policy-driven entitlement management. | privileged governance | 8.3/10 | 9.0/10 | 7.4/10 | 7.8/10 |
| 4 | Microsoft Entra Entitlement Management Manages access packages with time-bound access, approvals, and governance controls for applications connected to Entra ID. | cloud-first | 8.2/10 | 8.7/10 | 7.6/10 | 8.0/10 |
| 5 | Okta Identity Governance Delivers identity governance with access requests, role lifecycle management, and certification workflows integrated with Okta workflows. | cloud-first | 8.1/10 | 8.8/10 | 7.6/10 | 7.3/10 |
| 6 | Saviynt Governs identities and entitlements with access request and approval automation, identity analytics, and certifications across cloud and on-prem systems. | all-in-one | 7.6/10 | 8.5/10 | 6.8/10 | 7.1/10 |
| 7 | IBM Security Verify Governance Controls user access with role-based governance, approvals, and access reviews for applications integrated into IBM Security ecosystems. | enterprise | 7.3/10 | 8.2/10 | 6.9/10 | 6.8/10 |
| 8 | Ping Identity Governance Improves access governance through policy-driven access decisions and lifecycle controls for identities and resources. | policy-driven | 8.1/10 | 8.6/10 | 7.6/10 | 7.9/10 |
| 9 | One Identity Manager Automates joiner-mover-leaver identity workflows and access governance with role management, certifications, and policy enforcement. | suite | 7.8/10 | 8.4/10 | 6.9/10 | 7.1/10 |
| 10 | Access Reviews in SAP Identity Management Runs access reviews and governance workflows for SAP and connected applications using SAP Identity Management capabilities. | SAP-integrated | 6.9/10 | 7.2/10 | 6.4/10 | 6.8/10 |
Automates identity governance for enterprise access management with AI-assisted risk analytics, recertification, and policy-based workflows.
Governs user access with automated workflows for access requests, role mining, certification, and policy enforcement across enterprise apps.
Provides access governance with certification, segregation-of-duties controls, privileged access workflows, and policy-driven entitlement management.
Manages access packages with time-bound access, approvals, and governance controls for applications connected to Entra ID.
Delivers identity governance with access requests, role lifecycle management, and certification workflows integrated with Okta workflows.
Governs identities and entitlements with access request and approval automation, identity analytics, and certifications across cloud and on-prem systems.
Controls user access with role-based governance, approvals, and access reviews for applications integrated into IBM Security ecosystems.
Improves access governance through policy-driven access decisions and lifecycle controls for identities and resources.
Automates joiner-mover-leaver identity workflows and access governance with role management, certifications, and policy enforcement.
Runs access reviews and governance workflows for SAP and connected applications using SAP Identity Management capabilities.
SailPoint IdentityAI
enterpriseAutomates identity governance for enterprise access management with AI-assisted risk analytics, recertification, and policy-based workflows.
IdentityAI governance assistance for risk-driven access reviews and remediation guidance
SailPoint IdentityAI stands out by combining identity governance workflows with AI assistance for policy decisions, remediation guidance, and case handling. It delivers core access governance capabilities like joiner mover leaver provisioning, entitlement management, and access request and approval workflows. Risk-focused certifications and recertification workflows connect campaign evidence to control outcomes for audit-ready results. It also supports identity analytics to prioritize reviews and reduce noise across large applications and data sources.
Pros
- AI-assisted governance workflows that speed up remediation guidance
- Strong access certification and recertification campaigns with audit-ready evidence
- Granular entitlement management tied to policies across applications
- Robust integrations for identity sources and target application provisioning
- Identity analytics helps prioritize high-risk access reviews
Cons
- Setup and tuning typically require specialist identity governance expertise
- Complex workflows can be harder to administer without training
- Higher total cost for large deployments with multiple applications
Best For
Large enterprises needing AI-accelerated access governance and certification automation
More related reading
Oracle Identity Governance
enterpriseGoverns user access with automated workflows for access requests, role mining, certification, and policy enforcement across enterprise apps.
Automated access certification with policy-based evidence capture for compliance reporting
Oracle Identity Governance uses centralized joiner-mover-leaver workflows tied to policy-driven access reviews and approvals. It supports role and entitlement management with automated provisioning and deprovisioning across connected applications. Its strong audit and compliance reporting emphasizes traceability from request through approval and evidence generation.
Pros
- Policy-driven access approvals with auditable workflow trails
- Role and entitlement modeling supports structured access governance
- Automated joiner-mover-leaver provisioning reduces manual access changes
Cons
- Implementation typically needs specialized identity and integration expertise
- Review and reporting configuration can feel heavy for smaller teams
- Administration complexity increases with many connected applications
Best For
Enterprises standardizing access governance across Oracle and non-Oracle apps
CyberArk Identity Governance
privileged governanceProvides access governance with certification, segregation-of-duties controls, privileged access workflows, and policy-driven entitlement management.
Identity Certification campaigns with configurable attestations and comprehensive audit reporting
CyberArk Identity Governance focuses on life-cycle access for identities and the approval workflows that govern who gets what, when, and why. It provides request and approval automation, policy enforcement, and certification workflows tied to Active Directory and other enterprise apps. Strong audit trails and role-based access modeling support compliance reporting for high-risk systems. Deployment fits enterprises that need centralized governance across many applications and service accounts.
Pros
- Automates access requests with approval workflows and policy checks
- Supports access certification campaigns with audit-ready activity trails
- Enforces governance across enterprise apps, including directory-based identities
Cons
- Setup and integration effort rises with app count and identity complexity
- Role and policy modeling requires experienced administrators to avoid misalignment
- User experience can feel heavy for smaller teams with limited governance scope
Best For
Enterprises governing privileged and application access across many systems
More related reading
Microsoft Entra Entitlement Management
cloud-firstManages access packages with time-bound access, approvals, and governance controls for applications connected to Entra ID.
Entitlement Management access packages with automated request, approval, and lifecycle actions
Microsoft Entra Entitlement Management ties access requests, approvals, and lifecycle controls to Entra ID groups and entitlement packages. It supports role-based access reviews and dynamic assignments through scoped access, which helps standardize who can reach sensitive apps and resources. The product integrates tightly with Microsoft workflows, including automated access request flows and reporting for compliance. Strong governance comes from policy-driven workflows rather than manual ticketing and spreadsheets.
Pros
- Tight integration with Entra ID for group-based entitlements and lifecycle control
- Policy-driven request and approval workflows reduce manual access handling
- Role-based access reviews support compliance-focused governance workflows
- Audit-friendly reporting for entitlement assignments and approvals
Cons
- Setup requires Entra ID structure planning and entitlement scope design
- Complex approval and scoping rules can be difficult to model without testing
- Limited non-Microsoft app governance compared with broader access governance suites
Best For
Enterprises governing Entra ID access with policy workflows and audit-ready reviews
Okta Identity Governance
cloud-firstDelivers identity governance with access requests, role lifecycle management, and certification workflows integrated with Okta workflows.
Recertification and access reviews that enforce entitlement validation and audit trails
Okta Identity Governance distinguishes itself with strong integration into Okta Workforce Identity, using policies and workflows that extend existing identity operations. It supports access request and approval flows with configurable governance policies across apps and groups. It also provides recertification for access reviews and can automate lifecycle actions when entitlements change. Centralized reporting ties governance outcomes back to users, applications, and rule decisions.
Pros
- Deep integration with Okta Workforce Identity for policy-driven governance
- Configurable access request and approval workflows for controlled onboarding
- Recertification and access reviews for ongoing entitlement validation
- Auditable reporting that links decisions to users, apps, and rules
Cons
- Setup complexity increases when governance spans many apps and entitlements
- Advanced workflow design requires expertise in Okta policy patterns
- Value drops if you only need lightweight approval without review automation
Best For
Enterprises standardizing access governance on Okta identity policies
Saviynt
all-in-oneGoverns identities and entitlements with access request and approval automation, identity analytics, and certifications across cloud and on-prem systems.
Continuous access reviews with policy enforcement across entitlements and application roles
Saviynt stands out with enterprise-grade identity governance focused on access lifecycle automation across apps and cloud resources. It supports role and entitlement mining, policy-driven access request and approval workflows, and continuous access reviews. The platform adds strong auditability through built-in compliance reporting and historical change tracking, with integrations for common identity and ticketing ecosystems. Saviynt also emphasizes analytics for detecting risky access patterns and enforcing least-privilege over time.
Pros
- Automates access lifecycle with policy-driven workflows and approvals
- Supports entitlement intelligence for role and permission recertification
- Provides continuous access review controls and strong audit trails
- Delivers analytics for risky access detection and access pattern checks
Cons
- Implementation requires significant configuration and identity data mapping
- User experience can feel complex for business owners running governance cycles
- Advanced modeling work increases admin effort during ongoing tuning
Best For
Enterprises centralizing access governance across SaaS, cloud, and data platforms
More related reading
IBM Security Verify Governance
enterpriseControls user access with role-based governance, approvals, and access reviews for applications integrated into IBM Security ecosystems.
Role mining and role lifecycle governance tied to access certification decisions
IBM Security Verify Governance focuses on access certification and policy-driven role lifecycle control across enterprise applications. It combines role mining, governance workflows, and audit-ready reporting to help teams detect excessive and inappropriate entitlements. The product supports integration with identity sources and target systems so reviews can be based on actual assignments and changes.
Pros
- Strong access certification workflows with audit-grade reporting outputs
- Role lifecycle governance supports continuous control over entitlement changes
- Integration-oriented design helps align reviews with actual identity assignments
Cons
- Setup and tuning are heavier than simpler access review tools
- Configuration complexity increases with many applications and granular policies
- Value can be weak for smaller teams with limited governance needs
Best For
Enterprises needing certification and role governance across many applications
Ping Identity Governance
policy-drivenImproves access governance through policy-driven access decisions and lifecycle controls for identities and resources.
Governed access workflows for approvals and recertification across applications and entitlements
Ping Identity Governance stands out with policy-centric access workflows that integrate tightly with Ping Identity’s authentication and identity stack. It provides approvals, recertification, and separation-of-duties style governance capabilities to control who can access applications and entitlements. The solution focuses on managing access changes through governed workflows rather than manual ticketing or static role assignment alone. Integration with enterprise identity sources and downstream enforcement makes it practical for organizations standardizing access governance across many systems.
Pros
- Policy-driven access workflows with strong approval and recertification controls
- Deep integration with Ping Identity authentication and identity management components
- Governance enforcement designed for both applications and entitlements
Cons
- Administration complexity rises with large workflow and rule libraries
- Best results depend on solid identity source integration design
- Implementation effort can be high for nonstandard entitlement models
Best For
Enterprises needing policy-driven access approvals and recertification across many apps
More related reading
One Identity Manager
suiteAutomates joiner-mover-leaver identity workflows and access governance with role management, certifications, and policy enforcement.
Policy-based provisioning and governance workflows for role-based access across directories
One Identity Manager stands out by combining identity lifecycle management with governance workflows for complex, rule-driven access requests. It supports RBAC and lifecycle automation across Windows, Linux, Active Directory, and cloud directories using policy-based provisioning. The product emphasizes auditability through change tracking, approval workflows, and role and entitlement analysis tied to business risk. Governance capabilities are strongest where you need cross-system access orchestration rather than lightweight approvals alone.
Pros
- Automated access provisioning across on-prem and cloud directories
- Policy-driven approval workflows for role and entitlement changes
- Strong audit trails with change history for access governance
- Supports complex RBAC modeling across heterogeneous systems
Cons
- Configuration and tuning require specialized identity engineering
- User experience can feel heavy compared with workflow-only tools
- Implementation time increases with multi-system integration needs
Best For
Enterprises needing cross-system access governance with automation
Access Reviews in SAP Identity Management
SAP-integratedRuns access reviews and governance workflows for SAP and connected applications using SAP Identity Management capabilities.
Automated, role-driven access recertification workflows integrated with SAP identity governance
Access Reviews in SAP Identity Management focuses on automating periodic access recertifications tied to SAP identities and roles. It supports manager and role owner review workflows, collects decisions, and feeds results back into access compliance and remediation. The solution is strongest when your access model already uses SAP role design and identity governance patterns. Outside that SAP-centric scope, review workflows and integrations can feel less flexible than broader access governance suites.
Pros
- Tight integration with SAP Identity Management for access recertification
- Workflow-based access reviews with captured approvals and rejections
- Clear audit trail for access governance decisions and outcomes
Cons
- Best fit for SAP-centric access models and role structures
- Review setup and policy alignment can be complex in large environments
- Less competitive breadth for non-SAP applications and custom workflows
Best For
Enterprises running SAP-focused access governance with role-based recertification
Conclusion
After evaluating 10 security, SailPoint IdentityAI stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Access Governance Software
This buyer's guide explains how to choose Access Governance Software using concrete capabilities from SailPoint IdentityAI, Oracle Identity Governance, CyberArk Identity Governance, Microsoft Entra Entitlement Management, and the other tools in this top set. It maps specific features like certification evidence capture, entitlement access packages, and role mining-driven lifecycle controls to the teams that need them most. It also calls out the implementation and administration pitfalls that commonly slow adoption across this group of products.
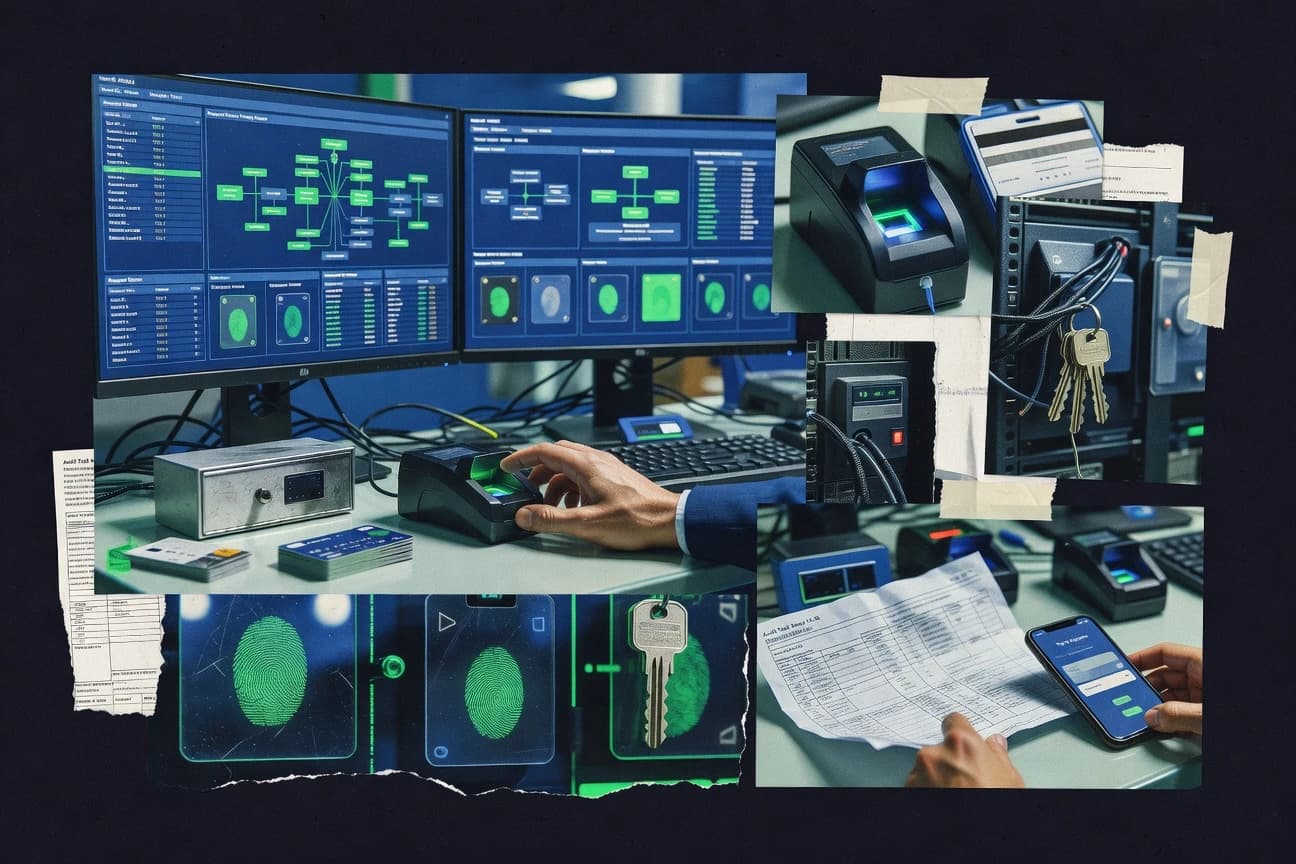
What Is Access Governance Software?
Access Governance Software automates and enforces who can access applications, entitlements, and resources by linking lifecycle events, approvals, and access certifications to audit-ready evidence. It solves problems like manual access handling, inconsistent joiner mover leaver processes, and periodic review fatigue by running policy-driven workflows and capturing decisions. Tools like SailPoint IdentityAI and CyberArk Identity Governance exemplify broad governance for enterprise access by combining certification campaigns and entitlement workflows with audit trails.
Key Features to Look For
Access governance outcomes depend on how well a product models access, runs workflows, and produces evidence that survives audits.
Risk-driven identity certification with remediation guidance
SailPoint IdentityAI uses identity analytics to prioritize high-risk access reviews and adds AI-assisted governance assistance that supports remediation guidance and case handling. CyberArk Identity Governance also emphasizes identity certification campaigns with configurable attestations and comprehensive audit reporting so reviewers can produce defensible outcomes.
Policy-based evidence capture that ties approvals to results
Oracle Identity Governance focuses on automated access certification with policy-based evidence capture that supports compliance traceability from request through approval and evidence generation. Okta Identity Governance ties governance outcomes back to users, applications, and rule decisions through auditable reporting that supports entitlement validation.
Automated joiner mover leaver and entitlement lifecycle enforcement
Oracle Identity Governance and One Identity Manager both emphasize automated joiner mover leaver workflows and policy-driven provisioning and deprovisioning to reduce manual access changes. CyberArk Identity Governance also automates access requests with approval workflows and policy checks so entitlement changes follow governance rules.
Role mining and role lifecycle governance tied to certifications
IBM Security Verify Governance includes role mining and role lifecycle governance tied to access certification decisions to help teams detect excessive and inappropriate entitlements. Saviynt adds role and entitlement mining plus continuous access review controls that enforce least-privilege over time.
Entitlement access packages with scoped approvals and lifecycle controls
Microsoft Entra Entitlement Management manages access through entitlement packages that connect requests, approvals, and lifecycle actions to Entra ID groups. Ping Identity Governance provides governed access workflows for approvals and recertification across applications and entitlements with policy-centric decisioning tied to its identity stack.
Continuous access reviews and historical change tracking
Saviynt supports continuous access reviews with policy enforcement across entitlements and application roles and includes strong auditability through historical change tracking. IBM Security Verify Governance and One Identity Manager also provide audit-ready reporting and change history so teams can explain what changed and why.
How to Choose the Right Access Governance Software
Pick the tool that matches your identity ecosystem, access model, and governance operating model so workflows are accurate and evidence is complete.
Match the platform fit to your identity sources and enforcement scope
If your access decisions primarily flow through Entra ID groups, Microsoft Entra Entitlement Management is purpose-built around entitlement packages tied to Entra ID group-based entitlements and lifecycle control. If your workforce identity operations run through Okta, Okta Identity Governance aligns governance policies and workflows with Okta Workforce Identity for policy-driven governance. If you need broad enterprise coverage across many systems and identity sources, SailPoint IdentityAI and CyberArk Identity Governance focus on enterprise-grade governance across applications and directory-based identities.
Validate that certification and evidence capture match your audit requirements
If auditors require traceability from request to approval to evidence, Oracle Identity Governance emphasizes auditable workflow trails and policy-based evidence capture during access certification. If you need structured attestations and detailed audit reporting, CyberArk Identity Governance provides identity certification campaigns with configurable attestations and comprehensive audit reporting. If you want risk-driven prioritization to reduce reviewer workload, SailPoint IdentityAI uses identity analytics to prioritize high-risk access reviews.
Choose workflow automation depth that your administrators can operate
If you can staff specialist identity governance administrators, SailPoint IdentityAI can be tuned for complex, policy-based workflows and AI-assisted governance assistance. If you have deep Okta policy expertise, Okta Identity Governance offers configurable access request and approval workflows but advanced workflow design requires expertise in Okta policy patterns. If you want faster rollout with simpler governance cycles, avoid products where admin effort rises sharply with granular policy and workflow libraries such as IBM Security Verify Governance and Ping Identity Governance.
Ensure your role and entitlement modeling supports lifecycle outcomes
If you need automation that continuously enforces least-privilege, Saviynt combines continuous access reviews with policy enforcement across entitlements and application roles. If you rely on role models and want mining-driven governance, IBM Security Verify Governance uses role mining and role lifecycle governance tied to access certification decisions. If you need cross-system access orchestration across heterogeneous directories, One Identity Manager emphasizes policy-based provisioning and governance workflows for role-based access across Windows, Linux, Active Directory, and cloud directories.
Run a realistic integration and workflow readiness test across your app mix
CyberArk Identity Governance, Oracle Identity Governance, and SailPoint IdentityAI all require integration effort that increases with app count and identity complexity, so test your highest-volume applications first. Microsoft Entra Entitlement Management requires Entra ID structure planning and entitlement scope design, so validate group design and scoped access rules before building approval chains. Ping Identity Governance and Saviynt depend on strong identity source integration design and entitlement modeling, so confirm your mapping quality before launching governance campaigns.
Who Needs Access Governance Software?
Access governance tools fit organizations that must control access lifecycle, run recurring certifications, and produce audit-grade evidence across identities and applications.
Large enterprises needing AI-accelerated access governance and certification automation
SailPoint IdentityAI fits teams that want AI-assisted governance assistance for risk-driven access reviews and remediation guidance plus identity analytics to prioritize high-risk reviews. This profile matches environments where certification campaigns and remediation workflows must scale across large application and data source estates.
Enterprises standardizing governance across Oracle and non-Oracle applications
Oracle Identity Governance fits organizations that need automated access certification with policy-driven approvals and auditable workflow trails across Oracle and non-Oracle apps. This audience benefits from joiner mover leaver workflows and entitlement modeling that ties evidence generation to compliance reporting.
Enterprises governing privileged and application access across many systems
CyberArk Identity Governance fits teams that require identity certification campaigns with configurable attestations and comprehensive audit reporting. This profile aligns with centralized governance for life-cycle access across Active Directory and other enterprise apps and service accounts.
Enterprises governing Entra ID group-based access with entitlement workflows
Microsoft Entra Entitlement Management fits organizations that structure access through Entra ID groups and want entitlement management access packages with automated request, approval, and lifecycle actions. This audience also benefits from role-based access reviews designed for compliance-focused governance.
Common Mistakes to Avoid
Most implementation failures in access governance come from mismatches between workflow complexity and operational readiness or from entitlement modeling that does not reflect real assignments.
Launching with complex workflows without governance expertise
SailPoint IdentityAI and Okta Identity Governance can deliver sophisticated policy workflows, but setup and tuning typically require specialist identity governance expertise. Okta Identity Governance also demands expertise in Okta policy patterns for advanced workflow design, so start with your highest-confidence entitlement rules.
Overlooking integration and identity data mapping effort
Saviynt and IBM Security Verify Governance require significant configuration and identity data mapping so reviews reflect actual assignments and changes. CyberArk Identity Governance also increases setup and integration effort as app count and identity complexity grow, so validate mappings early.
Building approvals and reporting without end-to-end evidence traceability
Oracle Identity Governance is built around policy-driven access approvals with traceability from request through approval and evidence generation, so skip this capability only if your audits do not require linkage. If you use tools like Okta Identity Governance and require audit trails, ensure your reporting ties decisions to users, applications, and rule outcomes.
Assuming coverage beyond your ecosystem will be effortless
Access Reviews in SAP Identity Management is strongest when your access model uses SAP role design and SAP Identity Management patterns, so non-SAP workloads often face less flexible review setup and policy alignment. Microsoft Entra Entitlement Management also has limited non-Microsoft app governance compared with broader access governance suites, so test cross-app workflows before committing.
How We Selected and Ranked These Tools
We evaluated each tool on overall capability, feature depth, ease of use, and value using the practical build and operation patterns described in the tool summaries. We separated SailPoint IdentityAI from lower-ranked options by combining broad access governance workflows with AI-assisted governance assistance for risk-driven access reviews, identity analytics to prioritize reviews, and audit-ready certification evidence tied to remediation workflows. We also used consistent weighting across certification and recertification automation, policy-driven approvals, role and entitlement lifecycle controls, and the degree of admin effort called out for complex multi-application environments.
Frequently Asked Questions About Access Governance Software
Which access governance product is best for AI-assisted access review decisions and remediation guidance?
SailPoint IdentityAI is built to support access governance with AI assistance for policy decisions, remediation guidance, and case handling. It also connects risk-focused certifications and recertification workflows to audit-ready evidence and uses identity analytics to prioritize reviews and reduce review noise.
How do Oracle Identity Governance and Microsoft Entra Entitlement Management handle joiner-mover-leaver lifecycle workflows?
Oracle Identity Governance centralizes joiner-mover-leaver workflows and ties them to policy-driven access reviews and approvals. Microsoft Entra Entitlement Management ties lifecycle controls to Entra ID groups and entitlement packages and drives access requests and approvals through policy-driven flows.
Which tools are strongest for identity certification campaigns with strong audit trails and evidence generation?
CyberArk Identity Governance provides identity certification campaigns with configurable attestations and comprehensive audit reporting. SailPoint IdentityAI adds evidence generation tied to control outcomes, while Oracle Identity Governance emphasizes end-to-end traceability from request through approval and evidence generation.
What product should I choose if I need access governance that integrates tightly with Entra ID group and scoped resource assignments?
Microsoft Entra Entitlement Management is the most direct fit for governing Entra ID access because it builds access packages that map to Entra ID groups. It supports role-based access reviews and dynamic assignments through scoped access and plugs into Microsoft workflows for automated request flows and reporting.
Which access governance platforms are best for privileged access and high-risk system approvals across many apps and service accounts?
CyberArk Identity Governance is designed around centrally governed life-cycle access for identities, with request and approval automation and policy enforcement. It also supports role-based access modeling and strong audit trails that work well for high-risk systems across many enterprise applications.
If my environment is standardized on Okta for identity and group-based policies, which governance tool fits best?
Okta Identity Governance extends Okta Workforce Identity with governance policies and workflows across apps and groups. It supports access request and approval flows plus recertification, and its reporting ties governance outcomes back to users, applications, and rule decisions.
Which option supports continuous access reviews and least-privilege enforcement over time across SaaS, cloud, and data platforms?
Saviynt focuses on continuous access reviews and policy enforcement to drive least-privilege over time. It supports access lifecycle automation across SaaS, cloud, and data platforms, with historical change tracking and analytics for risky access pattern detection.
How do IBM Security Verify Governance and One Identity Manager differ for role mining and certification-driven governance?
IBM Security Verify Governance emphasizes access certification and policy-driven role lifecycle control using role mining to detect excessive and inappropriate entitlements. One Identity Manager combines identity lifecycle management with rule-driven governance workflows and policy-based provisioning across Windows, Linux, Active Directory, and cloud directories.
Which product is best when your access model is already built around SAP roles and you want role-driven periodic recertification?
Access Reviews in SAP Identity Management automates periodic access recertifications tied to SAP identities and SAP roles. It supports manager and role owner review workflows and feeds decisions into access compliance and remediation, with the strongest fit when your role design uses SAP identity governance patterns.
What common implementation pitfall should I watch for when integrating access governance into existing workflow and identity ecosystems?
Saviynt and SailPoint IdentityAI both rely on accurate access discovery and change history, so poor connector coverage can lead to noisy or incomplete review evidence. CyberArk Identity Governance and Oracle Identity Governance also depend on clear role and entitlement modeling, so inconsistent target system role mapping can break the request-to-approval traceability needed for audit reporting.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Security alternatives
See side-by-side comparisons of security tools and pick the right one for your stack.
Compare security tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
