GITNUXSOFTWARE ADVICE
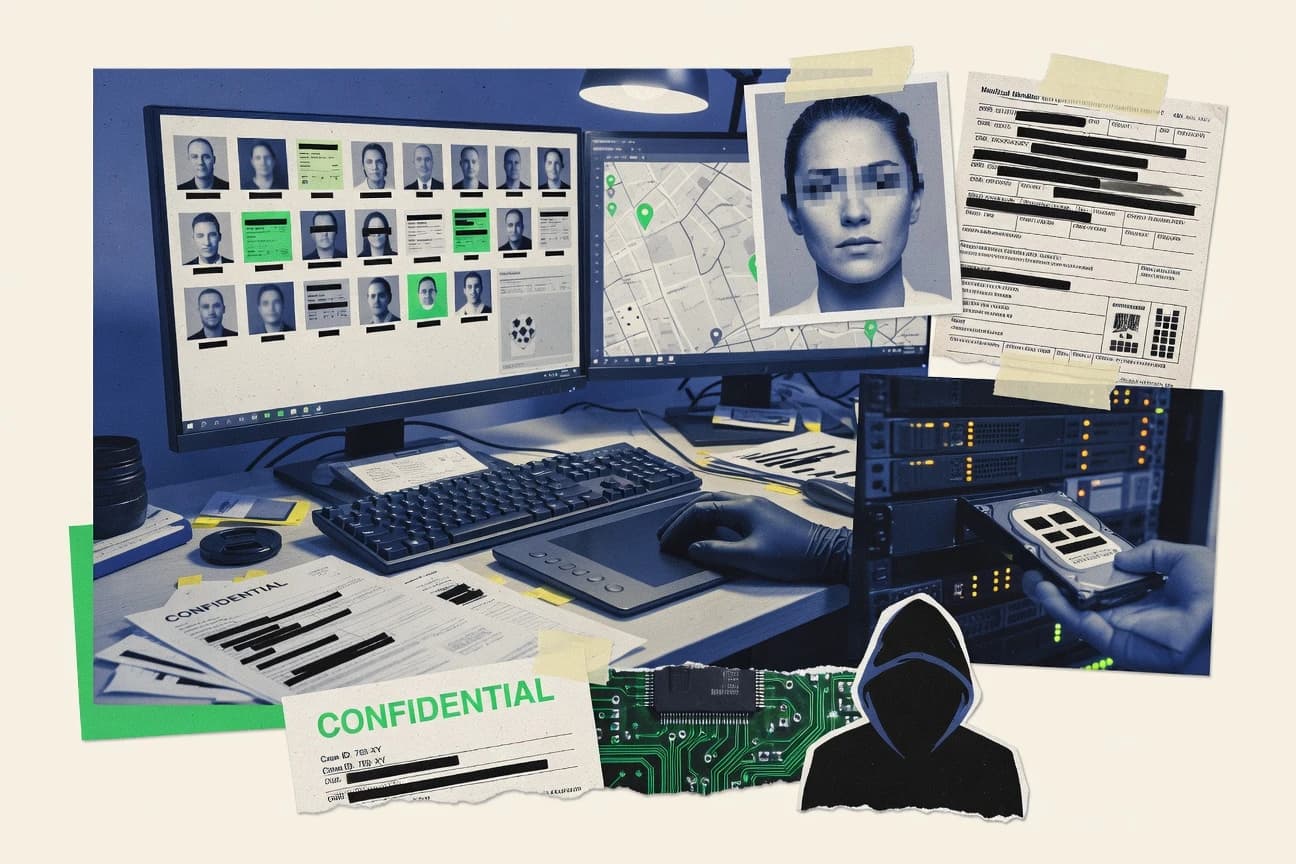
Data Science AnalyticsTop 10 Best Data Anonymization Software of 2026
Discover top data anonymization software to protect privacy.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
Microsoft Presidio
Custom Analyzer and Recognizer configuration for domain-specific PII detection.
Built for teams anonymizing customer and employee text fields via automated detection and redaction.
IBM Guardium Data Privacy
Policy-driven masking and anonymization tied to discovered sensitive data with integrated auditing evidence
Built for enterprises needing governed masking, anonymization, and audit trails across many data sources.
Delphix
Dynamic Data Masking with policy-driven virtualization to serve compliant, versioned datasets to nonproduction
Built for enterprises needing governed, repeatable anonymized data for rapid testing cycles.
Comparison Table
This comparison table evaluates data anonymization and privacy tooling across Microsoft Presidio, IBM Guardium Data Privacy, Delphix, Informatica Data Privacy, and Google Cloud Data Loss Prevention, plus additional options. You will compare how each product detects sensitive data, masks or tokenizes it, and integrates with common data platforms for governance and audit trails.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | Microsoft Presidio Microsoft Presidio detects personally identifiable information and supports de-identification actions like anonymization and pseudonymization via Python and REST APIs. | open-source | 9.3/10 | 9.2/10 | 8.4/10 | 8.7/10 |
| 2 | IBM Guardium Data Privacy IBM Guardium Data Privacy provides automated discovery, classification, and privacy controls for data including masking and anonymization workflows. | enterprise | 8.4/10 | 9.0/10 | 7.4/10 | 8.1/10 |
| 3 | Delphix Delphix provides data virtualization and masking so teams can use realistic anonymized data for non-production environments while preserving referential integrity. | data masking | 8.1/10 | 8.8/10 | 7.4/10 | 7.3/10 |
| 4 | Informatica Data Privacy Informatica Data Privacy discovers sensitive data and automates anonymization and masking policies across data stores and pipelines. | enterprise | 7.6/10 | 8.3/10 | 6.9/10 | 6.8/10 |
| 5 | Google Cloud Data Loss Prevention Google Cloud DLP inspects datasets for sensitive content and can transform records with de-identification methods such as tokenization and k-anonymity. | cloud DLP | 8.1/10 | 8.8/10 | 7.3/10 | 7.9/10 |
| 6 | Dataguise Dataguise delivers data masking and anonymization capabilities with automated sensitive data discovery and policy-driven protection for enterprises. | data masking | 7.6/10 | 8.2/10 | 7.1/10 | 7.4/10 |
| 7 | OneTrust Data Discovery and Protection OneTrust Data Discovery and Protection supports detection and anonymization controls to manage sensitive data across systems for privacy compliance. | privacy governance | 7.3/10 | 8.1/10 | 6.9/10 | 6.8/10 |
| 8 | IBM Guardium Privacy Analytics IBM Guardium Privacy Analytics helps detect privacy risk and supports de-identification planning using privacy analytics and governance workflows. | privacy analytics | 7.8/10 | 8.2/10 | 6.9/10 | 7.1/10 |
| 9 | Veeva Vault Data Privacy Veeva Vault Data Privacy supports privacy governance processes that can drive anonymization readiness for regulated data workflows. | regulated workflows | 7.8/10 | 8.3/10 | 6.9/10 | 7.1/10 |
| 10 | Open-source Anonimyzer Anonimyzer is an open-source anonymization utility for transforming datasets by removing or obfuscating identifying attributes. | open-source | 6.4/10 | 6.6/10 | 6.2/10 | 7.6/10 |
Microsoft Presidio detects personally identifiable information and supports de-identification actions like anonymization and pseudonymization via Python and REST APIs.
IBM Guardium Data Privacy provides automated discovery, classification, and privacy controls for data including masking and anonymization workflows.
Delphix provides data virtualization and masking so teams can use realistic anonymized data for non-production environments while preserving referential integrity.
Informatica Data Privacy discovers sensitive data and automates anonymization and masking policies across data stores and pipelines.
Google Cloud DLP inspects datasets for sensitive content and can transform records with de-identification methods such as tokenization and k-anonymity.
Dataguise delivers data masking and anonymization capabilities with automated sensitive data discovery and policy-driven protection for enterprises.
OneTrust Data Discovery and Protection supports detection and anonymization controls to manage sensitive data across systems for privacy compliance.
IBM Guardium Privacy Analytics helps detect privacy risk and supports de-identification planning using privacy analytics and governance workflows.
Veeva Vault Data Privacy supports privacy governance processes that can drive anonymization readiness for regulated data workflows.
Anonimyzer is an open-source anonymization utility for transforming datasets by removing or obfuscating identifying attributes.
Microsoft Presidio
open-sourceMicrosoft Presidio detects personally identifiable information and supports de-identification actions like anonymization and pseudonymization via Python and REST APIs.
Custom Analyzer and Recognizer configuration for domain-specific PII detection.
Microsoft Presidio stands out for combining a mature PII recognizer with a deterministic anonymization engine built for production pipelines. It detects entities across text using NLP-based models and can redact, replace, or mask detected spans. It also supports custom entity recognition and custom transformers for domain-specific PII. For data anonymization, it integrates with common workflows by exposing APIs and pairing with Microsoft tooling patterns.
Pros
- Strong PII detection using configurable recognizers and entity types
- Flexible anonymization actions like redaction and replacement of detected spans
- Supports custom entity patterns for domain-specific PII
- API-first design fits into automated data pipelines
Cons
- Requires model and threshold tuning for best detection accuracy
- Less turnkey than full DLP suites for end-user remediation workflows
- Coverage depends on the quality of recognizers for your data formats
Best For
Teams anonymizing customer and employee text fields via automated detection and redaction
IBM Guardium Data Privacy
enterpriseIBM Guardium Data Privacy provides automated discovery, classification, and privacy controls for data including masking and anonymization workflows.
Policy-driven masking and anonymization tied to discovered sensitive data with integrated auditing evidence
IBM Guardium Data Privacy focuses on applying privacy controls to sensitive data at scale across databases, servers, and cloud targets. It combines discovery and classification with rule-based masking and anonymization so organizations can reduce exposure in test and production contexts. The solution supports role-aware governance workflows and policy enforcement that can be tied to specific data sets and regulatory requirements. Strong integration with Guardium auditing helps teams validate that sensitive fields are handled consistently.
Pros
- Discovery and classification drive targeted masking and anonymization policies
- Role-aware governance supports controlled release and auditability for sensitive data
- Guardium auditing integration strengthens evidence for compliance reporting
- Works across multiple data sources to reduce manual privacy workflows
Cons
- Policy design can require specialized data privacy and database knowledge
- Setup complexity rises with many data sources and environments
- Advanced workflows can increase admin overhead for governance teams
Best For
Enterprises needing governed masking, anonymization, and audit trails across many data sources
Delphix
data maskingDelphix provides data virtualization and masking so teams can use realistic anonymized data for non-production environments while preserving referential integrity.
Dynamic Data Masking with policy-driven virtualization to serve compliant, versioned datasets to nonproduction
Delphix stands out with dynamic data masking and virtualization workflows that support fast, repeatable refreshes for nonproduction environments. It can deliver compliant copies of production data while keeping relationships and schema behavior consistent for testing. Core capabilities include masking policies, timeflow-based data versions, and automated provisioning for multiple apps and databases. It is designed for governance and auditability across the full data lifecycle instead of one-time anonymization exports.
Pros
- Dynamic masking and virtualization keep dev and test aligned with production
- Timeflow and versioned datasets support repeatable refreshes for investigations
- Centralized policies improve governance and audit trails for sensitive fields
- Supports automated provisioning across multiple applications and database targets
Cons
- Deployment and environment integration can be complex for small teams
- Licensing costs can be high when many environments and datasets are needed
- Advanced workflows require operational discipline to manage refresh schedules
Best For
Enterprises needing governed, repeatable anonymized data for rapid testing cycles
Informatica Data Privacy
enterpriseInformatica Data Privacy discovers sensitive data and automates anonymization and masking policies across data stores and pipelines.
Privacy Workbench guided data discovery with policy-based masking and audit traceability
Informatica Data Privacy stands out by pairing governed data discovery with automated masking and privacy controls for production and analytics datasets. It supports structured and unstructured data anonymization workflows using reusable policies and configurable transformation rules. The product emphasizes compliance-ready governance through audit trails, role-based access, and traceability from source fields to masked outputs.
Pros
- Policy-driven masking supports consistent anonymization across datasets and workflows
- Built-in privacy governance links discovered data to masking rules and audits
- Strong traceability and audit logging for regulated environment workflows
Cons
- Setup and policy modeling takes time for teams without existing Informatica expertise
- Masking configuration can become complex across many sources and data types
- Cost is typically high for smaller teams focused on simple anonymization
Best For
Enterprises needing governed masking with auditability for compliance and analytics pipelines
Google Cloud Data Loss Prevention
cloud DLPGoogle Cloud DLP inspects datasets for sensitive content and can transform records with de-identification methods such as tokenization and k-anonymity.
De-identification with tokenization, hashing, and redaction driven by DLP inspection findings
Google Cloud Data Loss Prevention stands out for combining automated de-identification with enterprise DLP rule enforcement across Google Cloud and managed storage. It includes built-in detectors and configurable transformation actions like tokenization, hashing, and redaction to anonymize sensitive fields. It supports inspection and classification at scale using jobs, streaming, and findings in Cloud Security tooling. The workflow is strongest when you already operate on Google Cloud services and want consistent anonymization controls across datasets and applications.
Pros
- Strong built-in detectors for PII, secrets, and custom data patterns
- Supports multiple de-identification actions including tokenization and hashing
- Integrates with Google Cloud storage and security workflows for consistent enforcement
- Inspection jobs and findings scale for large datasets
Cons
- Setup complexity rises with custom detectors, reidentification, and policies
- Value depends on Google Cloud usage patterns and scanning volume
- Fine-grained application-level anonymization requires careful integration work
- Managing transformation consistency across pipelines can add operational overhead
Best For
Enterprises on Google Cloud needing scalable automated de-identification
Dataguise
data maskingDataguise delivers data masking and anonymization capabilities with automated sensitive data discovery and policy-driven protection for enterprises.
Policy engine for automated masking and tokenization based on defined transformation rules
Dataguise stands out for policy-driven data anonymization that supports recurring automation across large datasets. It provides tokenization, masking, and pseudonymization capabilities designed to protect sensitive values while keeping data usable for analytics and testing. The product focuses on governance controls that help teams define how fields are transformed and when changes apply.
Pros
- Policy-driven anonymization rules for repeatable protection
- Supports tokenization, masking, and pseudonymization workflows
- Designed to preserve analytics utility after transformations
Cons
- Setup and rule modeling can feel heavy for small teams
- Integration effort grows with complex data pipelines
- Limited transparency for advanced de-identification performance
Best For
Organizations anonymizing customer and employee data for analytics and test environments
OneTrust Data Discovery and Protection
privacy governanceOneTrust Data Discovery and Protection supports detection and anonymization controls to manage sensitive data across systems for privacy compliance.
Automated sensitive data discovery feeding policy-based protection and anonymization workflows
OneTrust Data Discovery and Protection stands out for treating data privacy risk as a lifecycle workflow, not a one-time masking job. It combines automated discovery of sensitive data, policy-driven governance, and protection actions that include anonymization through configurable transformation. Strong integration with OneTrust Privacy and compliance workflows makes it easier to operationalize anonymization in support of GDPR and similar regimes. The product’s power is strongest when you already run centralized governance processes and need repeatable controls across systems.
Pros
- Policy-driven discovery and protection workflows tied to OneTrust governance
- Configurable anonymization and protection actions for sensitive data handling
- Broad coverage of enterprise data sources for repeatable privacy controls
Cons
- Setup and tuning of discovery and protection rules can take substantial effort
- Anonymization output quality depends on accurate classification and context
- Costs and administration overhead are heavy for smaller teams
Best For
Enterprises standardizing anonymization workflows across many systems with governance teams
IBM Guardium Privacy Analytics
privacy analyticsIBM Guardium Privacy Analytics helps detect privacy risk and supports de-identification planning using privacy analytics and governance workflows.
Privacy risk analytics that links discovered sensitive data to governed masking and anonymization actions
IBM Guardium Privacy Analytics focuses on discovering sensitive data across SQL and file sources and mapping it to privacy regulations and internal policies. It builds privacy-aware data controls by linking scans to anonymization actions like masking and tokenization for governed datasets. It supports recurring workflows with role-based access to protect privacy teams and data stewards during remediation. The strongest fit is teams that need ongoing privacy monitoring tied directly to how data is anonymized for analytics and sharing.
Pros
- Automates sensitive data discovery and privacy policy mapping across data sources
- Connects scan findings to anonymization workflows like masking and tokenization
- Provides governance controls for privacy teams via role-based access
- Supports recurring monitoring to keep anonymization aligned with data changes
Cons
- Setup and tuning require specialist effort for accurate classification
- Workflow configuration can feel heavy for small teams with limited data
- Value depends on using the broader IBM Guardium ecosystem effectively
Best For
Enterprises needing governed, recurring anonymization workflows tied to privacy policies
Veeva Vault Data Privacy
regulated workflowsVeeva Vault Data Privacy supports privacy governance processes that can drive anonymization readiness for regulated data workflows.
Privacy workflow governance with audit-ready controls inside the Veeva Vault ecosystem
Veeva Vault Data Privacy focuses on privacy management for regulated life sciences data workflows, not generic tokenization. It supports controlled data sharing with role-based access, audit trails, and privacy impact controls across Vault applications. The solution emphasizes governance and compliance operations for personal data rather than offering a simple one-click anonymization utility. Common use cases include masking or redaction for downstream access while keeping traceability for oversight.
Pros
- Built for life sciences governance workflows with privacy controls
- Strong audit trails for privacy actions and data access
- Role-based permissions align with regulated data sharing requirements
- Works alongside Vault ecosystem for centralized compliance operations
Cons
- Anonymization tooling feels indirect compared with standalone anonymizers
- Implementation requires Vault configuration and privacy model setup
- Cost and scope fit best for enterprise programs, not small labs
- Less suited for ad hoc anonymization outside structured Vault data
Best For
Enterprise life sciences teams needing governed privacy controls in Veeva Vault
Open-source Anonimyzer
open-sourceAnonimyzer is an open-source anonymization utility for transforming datasets by removing or obfuscating identifying attributes.
Configurable rule-driven anonymization that you can adapt to your dataset schema
Open-source Anonimyzer focuses on anonymizing datasets with rule-based transformations and automated masking workflows. It supports common data privacy tasks like removing or obfuscating direct identifiers and applying configurable substitutions to sensitive fields. The tool’s GitHub-first model makes it transparent to audit and modify, but that also shifts operational responsibility to the teams deploying it. It fits best when you can map your own data schema to its anonymization rules and validate results with your own quality checks.
Pros
- Open-source transparency helps teams audit anonymization logic
- Rule-based masking supports custom handling of sensitive fields
- Self-hosting enables control over processing and retention policies
Cons
- Setup and governance require developer effort
- Limited out-of-the-box discovery for unknown sensitive data
- Validation and re-identification risk testing are on the adopter
Best For
Teams building custom anonymization pipelines with self-hosted control
Conclusion
After evaluating 10 data science analytics, Microsoft Presidio stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Data Anonymization Software
This buyer's guide helps you choose data anonymization software for production pipelines and governed nonproduction environments, with practical examples from Microsoft Presidio, IBM Guardium Data Privacy, Delphix, and Google Cloud Data Loss Prevention. It also compares enterprise privacy governance options like Informatica Data Privacy, OneTrust Data Discovery and Protection, IBM Guardium Privacy Analytics, and Veeva Vault Data Privacy. You will also see how teams building custom pipelines can use Open-source Anonimyzer and how general-purpose anonymization automation can be handled by Dataguise.
What Is Data Anonymization Software?
Data anonymization software detects or maps sensitive fields and transforms them using redaction, masking, tokenization, hashing, pseudonymization, or related de-identification actions. It solves the problem of reducing exposure of personal data in analytics, testing, monitoring, and data sharing while preserving enough usability for downstream workflows. Many organizations use it to turn regulated datasets into compliant copies for nonproduction use and controlled access. Microsoft Presidio represents text-first anonymization with PII detection and deterministic de-identification actions, while Delphix represents governed dynamic masking that keeps referential integrity across versioned refreshes.
Key Features to Look For
The right anonymization features determine whether you can automate correctly, prove governance, and keep data usable for testing or analytics.
PII detection plus configurable anonymization actions
Look for tools that detect PII and then apply multiple transformation types such as redaction and replacement of spans. Microsoft Presidio excels here with its mature PII recognizer and flexible anonymization actions for detected spans, including redaction, replacement, and masking.
Custom analyzers and recognizers for domain-specific PII
Choose software that lets you define custom entity detection so accuracy matches your data formats and business terms. Microsoft Presidio enables custom Analyzer and Recognizer configuration for domain-specific PII so teams can extend detection beyond default entity types.
Policy-driven discovery to targeted masking and anonymization
Prioritize solutions that discover sensitive data and then tie that discovery to specific masking or anonymization policies. IBM Guardium Data Privacy links discovered sensitive data to policy-driven masking and anonymization with integrated auditing evidence, and Informatica Data Privacy ties privacy workbench discovery to policy-based masking with audit traceability.
Integrated auditing and evidence for compliance workflows
Select tools that produce audit trails showing which sensitive fields were anonymized and by which controlled rules. IBM Guardium Data Privacy strengthens compliance reporting by integrating Guardium auditing evidence, and Informatica Data Privacy provides audit logging with traceability from source fields to masked outputs.
Scalable de-identification driven by inspection findings
For large datasets and frequent scanning, prioritize built-in detectors and transformation actions that run from inspection findings. Google Cloud Data Loss Prevention supports tokenization, hashing, and redaction driven by DLP inspection findings and integrates with Google Cloud security tooling for scalable enforcement.
Governed repeatable anonymized datasets with dynamic masking and refresh
If your goal is ongoing nonproduction readiness, prioritize dynamic masking and versioned refresh rather than one-time exports. Delphix delivers dynamic data masking with policy-driven virtualization so teams can provision compliant, versioned datasets that preserve referential integrity across repeated refresh cycles.
How to Choose the Right Data Anonymization Software
Pick the tool that matches your data types, workflow style, and governance requirements so anonymization is both correct and operationally sustainable.
Match the anonymization workflow to your data lifecycle
If you need deterministic detection and transformation for text fields in pipelines, start with Microsoft Presidio since it supports PII detection and de-identification actions like anonymization and pseudonymization via Python and REST APIs. If you need repeatable anonymized datasets for dev and test with consistent relationships, Delphix is designed for dynamic masking and timeflow-based versioned datasets with automated provisioning.
Use governed discovery that drives targeted transformation rules
If you must control which sensitive fields get protected, choose IBM Guardium Data Privacy or Informatica Data Privacy because both link discovery to policy-driven masking and anonymization with audit traceability. For organizations running governance workflows across systems, OneTrust Data Discovery and Protection feeds policy-based protection and anonymization actions from automated sensitive data discovery.
Select de-identification methods that preserve your intended data usability
If you need tokenization, hashing, and redaction options that execute based on inspection results, Google Cloud Data Loss Prevention provides multiple de-identification actions driven by DLP findings. If you want policy-controlled tokenization and pseudonymization designed to keep analytics utility, Dataguise supports tokenization, masking, and pseudonymization via a policy engine for automated masking and tokenization rules.
Plan for quality tuning and classification accuracy
If your environment includes domain-specific or uncommon identifiers, Microsoft Presidio lets you configure custom analyzers and recognizers so detection thresholds and entity types can be tuned to your formats. If your environment requires privacy risk monitoring with mapping to anonymization actions, IBM Guardium Privacy Analytics ties scan findings to masking and tokenization through privacy risk analytics and role-based governance, which still requires specialist tuning for accurate classification.
Choose governance fit for your organization and ecosystem
If you operate within Veeva’s life sciences environment, Veeva Vault Data Privacy provides privacy workflow governance, audit trails, and role-based permissions across Vault applications for regulated personal data sharing. If you need fully governed database and ecosystem workflows with integrated evidence, IBM Guardium Data Privacy and IBM Guardium Privacy Analytics align with Guardium auditing for validation and recurring monitoring.
Who Needs Data Anonymization Software?
Data anonymization software benefits teams that must reduce personal data exposure while keeping datasets usable for analytics, testing, or regulated sharing.
Teams anonymizing customer and employee text fields via automated detection and redaction
Microsoft Presidio fits this audience because it detects PII across text and applies anonymization actions like redaction, replacement, and masking through API-first automation. Teams that require domain-specific identifier coverage can use Presidio’s custom Analyzer and Recognizer configuration for domain-specific PII detection.
Enterprises needing governed masking, anonymization, and audit trails across many data sources
IBM Guardium Data Privacy fits because it performs discovery and classification and then enforces rule-based masking and anonymization with Guardium auditing integration. Informatica Data Privacy also fits because Privacy Workbench guides discovery and produces audit traceability from source fields to masked outputs.
Enterprises needing governed, repeatable anonymized data for rapid testing cycles
Delphix fits because it delivers dynamic data masking with policy-driven virtualization and timeflow-based, versioned datasets that keep schema behavior consistent. This approach supports automated provisioning for multiple apps and database targets with governance and auditability across the data lifecycle.
Enterprise platforms standardizing anonymization workflows across many systems using centralized governance
OneTrust Data Discovery and Protection fits because it treats anonymization as a lifecycle workflow with automated discovery feeding policy-based protection and anonymization actions. IBM Guardium Privacy Analytics fits when you need recurring privacy monitoring tied directly to how data is anonymized for analytics and sharing.
Common Mistakes to Avoid
Common failure patterns come from mismatching workflow style to requirements and underestimating setup effort for accurate classification and governance.
Treating anonymization as a one-time export instead of a governed lifecycle
Delphix prevents lifecycle drift by using dynamic masking and policy-driven virtualization that supports repeatable refreshes for nonproduction. IBM Guardium Data Privacy and OneTrust Data Discovery and Protection prevent ad hoc anonymization by tying discovery to policy enforcement and role-aware governance workflows.
Ignoring domain-specific PII coverage and relying on default detection alone
Microsoft Presidio avoids coverage gaps for domain terms by allowing custom Analyzer and Recognizer configuration for domain-specific PII. IBM Guardium Data Privacy and IBM Guardium Privacy Analytics still require specialist tuning for accurate classification when identifiers differ from typical patterns.
Choosing a tool without the audit evidence your compliance process needs
IBM Guardium Data Privacy integrates Guardium auditing evidence for compliance reporting so you can validate consistent handling of sensitive fields. Informatica Data Privacy adds audit logging and traceability from discovered data to masked outputs so governance teams can produce evidence.
Underestimating setup complexity when using inspection and policy orchestration
Google Cloud Data Loss Prevention can require careful integration work for fine-grained application-level anonymization and consistent transformation across pipelines. OneTrust Data Discovery and Protection and Informatica Data Privacy can require substantial effort for setup and tuning of discovery and protection rules across complex sources.
How We Selected and Ranked These Tools
We evaluated each anonymization solution on overall capability, feature depth, ease of use, and value fit for practical adoption. Microsoft Presidio stood apart because it combined strong configurable PII detection with flexible anonymization actions for detected spans and an API-first design suitable for automated pipelines. IBM Guardium Data Privacy ranked high for governed masking and anonymization tied to discovery with integrated auditing evidence across many data sources. We separated tools designed for text-first de-identification like Microsoft Presidio from tools designed for dynamic governed nonproduction provisioning like Delphix and from tools designed for inspection-driven de-identification like Google Cloud Data Loss Prevention.
Frequently Asked Questions About Data Anonymization Software
How do Microsoft Presidio and IBM Guardium Data Privacy differ in how they anonymize data in production?
Microsoft Presidio uses NLP-based PII detection plus deterministic redaction, replacement, or masking on text fields, and it supports custom analyzers for domain-specific entities. IBM Guardium Data Privacy applies policy-driven masking and anonymization across databases, servers, and cloud targets with discovery and auditing evidence integrated into Guardium governance workflows.
Which tool is best for recurring anonymization workflows tied to privacy policies rather than one-time exports?
OneTrust Data Discovery and Protection treats anonymization as a lifecycle workflow by coupling automated sensitive-data discovery with policy-driven protection actions. IBM Guardium Privacy Analytics also supports recurring privacy monitoring by linking scans to specific masking and tokenization actions for governed datasets.
What should teams look for when they need repeatable anonymized datasets for fast testing cycles?
Delphix provides dynamic data masking and virtualization so teams can refresh compliant nonproduction environments while preserving schema behavior and data relationships. Dataguise focuses on policy-driven tokenization, masking, and pseudonymization designed for automated recurring transformations across large datasets.
How do Google Cloud Data Loss Prevention and Informatica Data Privacy handle de-identification actions at scale?
Google Cloud Data Loss Prevention runs DLP inspection with transformation actions like tokenization, hashing, and redaction and can execute via jobs and streaming workflows in Google Cloud. Informatica Data Privacy pairs governed data discovery with reusable privacy policies and configurable transformation rules, and it emphasizes audit trails and traceability from source fields to masked outputs.
Which solution fits organizations that need anonymization controls integrated into cloud security and storage workflows?
Google Cloud Data Loss Prevention is strongest when you operate in Google Cloud because it aligns de-identification actions with DLP rule enforcement across managed storage. IBM Guardium Data Privacy targets multi-system governance by enforcing masking and anonymization policies with Guardium auditing across databases and cloud targets.
What is the most direct way to maintain data usability after anonymization for analytics and testing?
Dataguise is built around tokenization, masking, and pseudonymization so sensitive values can change while remaining usable for analytics and test scenarios. Delphix also preserves relationships and schema behavior through dynamic masking and virtualization so downstream applications keep consistent semantics.
How do Informatica Data Privacy and IBM Guardium Data Privacy support governance and auditability?
Informatica Data Privacy emphasizes compliance-ready governance through audit trails, role-based access, and traceability from source fields to masked outputs via its privacy workbench guided discovery. IBM Guardium Data Privacy combines role-aware governance workflows with policy enforcement and integrated Guardium auditing so teams can validate consistent handling of sensitive fields.
Which tools are designed for structured privacy workflows in regulated life sciences environments?
Veeva Vault Data Privacy targets life sciences privacy operations with role-based access, audit trails, and privacy impact controls inside the Veeva Vault ecosystem. Other tools like Microsoft Presidio can mask text spans, but Veeva Vault focuses on governance and compliance operations for regulated Vault workflows rather than generic anonymization utilities.
What are the practical trade-offs of using Open-source Anonimyzer compared with managed enterprise platforms?
Open-source Anonimyzer supports rule-based dataset anonymization with configurable substitutions and uses a GitHub-first approach that makes transformation logic transparent and modifiable. That transparency shifts operational responsibility to the teams deploying it, while enterprise platforms like IBM Guardium Data Privacy and OneTrust Data Discovery and Protection provide governed discovery-to-action workflows with built-in governance integration.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Data Science Analytics alternatives
See side-by-side comparisons of data science analytics tools and pick the right one for your stack.
Compare data science analytics tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
