GITNUXSOFTWARE ADVICE
SecurityTop 10 Best User Activity Monitoring Software of 2026
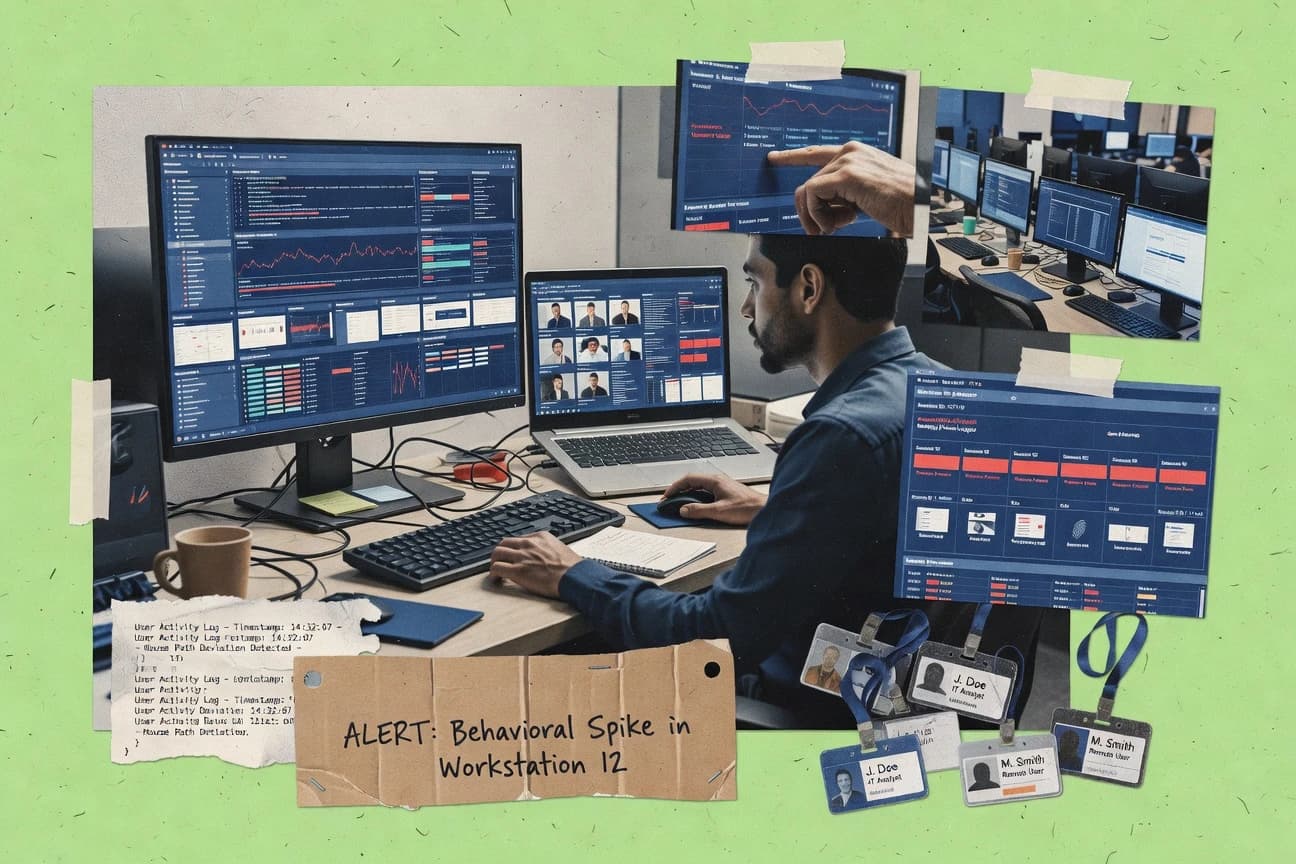
Discover top user activity monitoring tools to boost productivity & security. Compare features & find the best fit for your business today.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
ActivTrak
Policy-based alerts that trigger on defined activity thresholds across users and apps
Built for mid-market and enterprise teams needing governance-grade user activity monitoring.
Teramind
Behavior analytics with policy-based alerting tied to monitored user actions
Built for security teams monitoring regulated workflows across distributed endpoints.
Securonix User and Entity Behavior Analytics
Behavior-based risk scoring for users and entities across authentication and access activity
Built for mid-market to enterprise SOCs needing UEBA-driven user activity detection.
Related reading
Comparison Table
This comparison table evaluates user activity monitoring software across core capabilities like endpoint and application visibility, alerting and case management, investigation workflows, and policy enforcement. It contrasts platforms including ActivTrak, Teramind, Securonix User and Entity Behavior Analytics, Veriato, and Verint so you can compare how each tool supports threat detection, insider-risk analytics, and audit readiness.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | ActivTrak ActivTrak monitors employee and user activity across applications and websites with analytics, alerts, and investigation-ready reporting. | enterprise | 9.1/10 | 9.2/10 | 8.4/10 | 8.6/10 |
| 2 | Teramind Teramind provides user activity monitoring with behavior analytics, screen recording, alerts, and compliance-oriented audit trails. | behavior-analytics | 8.6/10 | 9.1/10 | 7.4/10 | 8.0/10 |
| 3 | Securonix User and Entity Behavior Analytics Securonix UEBA correlates user and entity activity signals to detect insider risk and account misuse with investigative workflows. | UEBA | 8.1/10 | 8.8/10 | 7.2/10 | 7.6/10 |
| 4 | Veriato Veriato monitors digital behavior with activity tracking, investigations, and configurable policies for security and compliance use cases. | investigation | 8.1/10 | 8.8/10 | 7.4/10 | 7.6/10 |
| 5 | Verint Verint delivers digital intelligence for workforce and enterprise monitoring with analytics, governance, and audit support. | workforce-monitoring | 7.6/10 | 8.3/10 | 6.8/10 | 7.2/10 |
| 6 | Nextiva (VoIP and contact center user activity visibility) Nextiva provides user and agent activity visibility through contact center and VoIP analytics that track interactions and performance signals. | contact-center | 7.4/10 | 8.1/10 | 6.9/10 | 7.0/10 |
| 7 | Hubstaff Hubstaff tracks time and activity with productivity analytics, screenshots, and task-oriented reporting for distributed teams. | productivity | 7.2/10 | 7.8/10 | 6.9/10 | 7.1/10 |
| 8 | RescueTime RescueTime monitors application and website usage and produces insights and reports about how time is spent. | self-monitoring | 8.0/10 | 8.5/10 | 8.2/10 | 7.4/10 |
| 9 | DeskTime DeskTime monitors computer activity and time usage with automatic tracking, reports, and optional screenshots. | time-tracking | 7.6/10 | 8.1/10 | 7.4/10 | 7.3/10 |
| 10 | Open-source: Syncthing (activity via device sync and logs) Syncthing enables device-to-device file synchronization and provides detailed logs that show who accessed what data through sync activity records. | open-source | 6.8/10 | 7.0/10 | 6.2/10 | 8.4/10 |
ActivTrak monitors employee and user activity across applications and websites with analytics, alerts, and investigation-ready reporting.
Teramind provides user activity monitoring with behavior analytics, screen recording, alerts, and compliance-oriented audit trails.
Securonix UEBA correlates user and entity activity signals to detect insider risk and account misuse with investigative workflows.
Veriato monitors digital behavior with activity tracking, investigations, and configurable policies for security and compliance use cases.
Verint delivers digital intelligence for workforce and enterprise monitoring with analytics, governance, and audit support.
Nextiva provides user and agent activity visibility through contact center and VoIP analytics that track interactions and performance signals.
Hubstaff tracks time and activity with productivity analytics, screenshots, and task-oriented reporting for distributed teams.
RescueTime monitors application and website usage and produces insights and reports about how time is spent.
DeskTime monitors computer activity and time usage with automatic tracking, reports, and optional screenshots.
Syncthing enables device-to-device file synchronization and provides detailed logs that show who accessed what data through sync activity records.
ActivTrak
enterpriseActivTrak monitors employee and user activity across applications and websites with analytics, alerts, and investigation-ready reporting.
Policy-based alerts that trigger on defined activity thresholds across users and apps
ActivTrak stands out with strong employee activity analytics that tie actions to specific applications, websites, and user groups. It provides clear usage reporting, custom dashboards, and alerting so managers can spot unusual patterns and productivity shifts. The platform supports audit-focused monitoring with searchable activity logs and configurable policies for acceptable use.
Pros
- Granular visibility across apps, websites, and user groups
- Custom dashboards and searchable activity logs for investigations
- Policy-based alerting for suspicious or policy-breaking behavior
- Supports audit trails that help governance and compliance needs
Cons
- Advanced analysis can require training to configure well
- Browser and app categorization accuracy varies by environment
- Deep reporting setup can take time for multi-department rollouts
Best For
Mid-market and enterprise teams needing governance-grade user activity monitoring
More related reading
Teramind
behavior-analyticsTeramind provides user activity monitoring with behavior analytics, screen recording, alerts, and compliance-oriented audit trails.
Behavior analytics with policy-based alerting tied to monitored user actions
Teramind stands out for combining user activity monitoring with configurable policy controls for security and compliance. It captures end-user actions across endpoints and key business apps, then maps events to alerts, dashboards, and investigative timelines. Its feature set extends beyond passive logging with behavior analytics, content and app activity tracking, and admin workflows for governance. Implementation supports both surveillance and incident response use cases with role-based oversight and configurable retention.
Pros
- Granular visibility into endpoint, app, and session-level activity
- Configurable policies turn monitoring signals into actionable alerts
- Strong investigation workflow with timeline-based event reviews
Cons
- Initial setup and tuning policies takes administrator effort
- Power-user dashboards can feel complex without training
- High monitoring depth increases operational and privacy management overhead
Best For
Security teams monitoring regulated workflows across distributed endpoints
Securonix User and Entity Behavior Analytics
UEBASecuronix UEBA correlates user and entity activity signals to detect insider risk and account misuse with investigative workflows.
Behavior-based risk scoring for users and entities across authentication and access activity
Securonix User and Entity Behavior Analytics focuses on UEBA for spotting suspicious activity by modeling behavior across users, endpoints, and identities. It performs continuous analytics on authentication, access, and user actions to surface anomalies and investigation-ready alerts. The solution ties detections to identity and device context to reduce noise during investigations. It is best suited for security teams that need behavioral detections integrated with SIEM workflows and case handling.
Pros
- UEBA detections built on identity, endpoint, and behavior signals
- Investigation-focused alerts with contextual risk scoring
- Supports integration patterns for SIEM and SOC investigation workflows
- Continuous monitoring for anomalous user and entity actions
Cons
- Tuning detections and baselines can take time and expert effort
- Alert volume can increase without careful policy configuration
- Implementation complexity is higher than simpler activity monitoring tools
Best For
Mid-market to enterprise SOCs needing UEBA-driven user activity detection
Veriato
investigationVeriato monitors digital behavior with activity tracking, investigations, and configurable policies for security and compliance use cases.
Veriato Behavioral Analytics that scores suspicious activity patterns for investigation prioritization
Veriato focuses on employee device and application activity monitoring, combining behavioral analytics with user visibility for compliance and investigation. It supports policy-based monitoring, centralized case review, and alerting tied to user and system events. The solution is built to track digital work patterns across endpoints rather than only capturing basic login telemetry. Its value shows most in incident investigation workflows where audit-ready evidence and timelines matter.
Pros
- Strong event and activity timeline for investigations across endpoints
- Policy-driven monitoring to target specific apps, actions, and users
- Behavioral analytics help flag suspicious patterns beyond simple logs
- Central case review supports audit-style evidence organization
Cons
- Setup and tuning require admin time to avoid noisy monitoring
- Dashboards can feel dense without investigation structure
- Pricing and scope fit mid-market needs more than small teams
- Onboarding may require tighter endpoint readiness planning
Best For
Security and compliance teams investigating endpoint behavior across mid-market workforces
Verint
workforce-monitoringVerint delivers digital intelligence for workforce and enterprise monitoring with analytics, governance, and audit support.
Case management and investigator workflows tied to captured user activity events
Verint stands out for deep enterprise behavior analytics that blend user activity monitoring with case-driven investigation workflows. The product suite supports session-level monitoring, event capture, and security-focused alerting to help teams trace suspicious actions across systems. It also emphasizes auditability and governance so monitored activity can be reviewed for compliance and operational forensics. Integration depth with enterprise environments is a core differentiator compared to lightweight activity trackers.
Pros
- Strong investigative workflow support for monitored activity and alerts
- Enterprise-grade audit trail features for governance and compliance reviews
- Broad integration capability for complex IT and security environments
Cons
- Setup and tuning require more administrator time than simpler monitoring tools
- Dashboards can feel complex when you only need basic user tracking
- Licensing and implementation costs can be high for smaller teams
Best For
Large enterprises needing governed user activity monitoring with investigation workflows
Nextiva (VoIP and contact center user activity visibility)
contact-centerNextiva provides user and agent activity visibility through contact center and VoIP analytics that track interactions and performance signals.
Agent and call activity analytics in Nextiva Contact Center dashboards
Nextiva stands out with deep visibility into voice and contact center activity through its VoIP and call center tooling. It captures call and agent performance signals such as call recordings, call outcomes, and interaction metrics tied to users. Admins can monitor usage patterns across phone calls and contact center workflows rather than generic device or app activity. The result is strong operational oversight for voice-based teams with weaker coverage for non-telephony user actions.
Pros
- Call and agent activity visibility tightly integrated into VoIP and contact center workflows
- Supports call recordings and interaction metrics for audit-ready review and coaching
- Central admin dashboards surface user-level performance and call outcomes
Cons
- User activity monitoring mainly covers phone and contact center actions, not broad app usage
- Reporting and configuration can feel complex for teams without contact center experience
- Visibility depends on consistent agent routing and logging across call flows
Best For
Contact center teams needing user activity visibility for calls and agent workflows
More related reading
Hubstaff
productivityHubstaff tracks time and activity with productivity analytics, screenshots, and task-oriented reporting for distributed teams.
Screenshot capture tied to time tracking and idle detection
Hubstaff is distinct for combining user activity monitoring with time tracking and payroll-ready reporting for distributed teams. It captures screenshots, tracks app and website usage, and reports idle time with automatic work summaries. Managers can enforce productivity policies with alerts for prolonged inactivity and generate detailed timesheets for billing or internal cost tracking.
Pros
- App and website tracking with idle-time reports for clear activity visibility
- Screenshot capture and timestamped evidence support audits and attendance checks
- Automated timesheets and reports help measure billable and internal work
- Project and client tagging makes monitoring data easier to organize
Cons
- Setup and monitoring configuration take time to avoid noisy alerts
- Screenshot capture can feel intrusive for teams with strict privacy needs
- Deep analytics depend on correct tagging and consistent team usage
- Policy enforcement features can require careful tuning to match roles
Best For
Teams needing evidence-based time tracking and activity monitoring for projects
RescueTime
self-monitoringRescueTime monitors application and website usage and produces insights and reports about how time is spent.
Focus time alerts and goals based on tracked app and website categories
RescueTime stands out by turning passive computer activity tracking into actionable productivity insights with automated reports. It categorizes applications and websites into custom or predefined productivity levels and shows time breakdowns by day and week. You can set focus goals, block distractions by category, and review analytics that highlight trends and recurring time sinks.
Pros
- Accurate app and website tracking feeds detailed time analytics
- Custom category rules let you define productivity for your workflows
- Daily and weekly reports highlight trends without manual tagging
Cons
- Advanced insights like team views require higher-tier access
- Website tracking depends on browser integration settings
- Distraction blocking focuses on categories, not individual URLs
Best For
Individuals and small teams tracking productivity without invasive monitoring
DeskTime
time-trackingDeskTime monitors computer activity and time usage with automatic tracking, reports, and optional screenshots.
Idle time alerts that flag inactive users based on detected activity
DeskTime stands out for combining lightweight time tracking with user activity monitoring that updates with minimal manual input. It captures application and website usage and produces team and individual activity reports for productivity and attendance insights. The software includes alerts for idle time and time tracking controls that support timesheet workflows. It also supports integrations for exporting or connecting tracking data to common business tools.
Pros
- Automatic application and website tracking reduces manual timesheet work
- Idle time alerts help managers spot stalled work quickly
- Team dashboards show productivity patterns across projects and roles
- Timesheet support fits periodic approval and reporting workflows
Cons
- Monitoring depth can feel intrusive for privacy-sensitive teams
- Admin setup and policy tuning take time to align with team expectations
- Reporting flexibility is limited for highly customized analytics needs
- Reviewing activity details is slower for large orgs
Best For
Teams needing app and idle monitoring with timesheet reporting
Open-source: Syncthing (activity via device sync and logs)
open-sourceSyncthing enables device-to-device file synchronization and provides detailed logs that show who accessed what data through sync activity records.
Per-device synchronization status and detailed log history for transfer and error events
Syncthing is distinct because it monitors activity through real-time device-to-device synchronization events and detailed per-node logs. It tracks what was shared, when transfers started, and the outcome of each sync via its status pages and log history. Syncthing also supports scheduled maintenance windows and bandwidth controls that influence sync behavior and the activity you see. For user activity monitoring, it works best as device-level activity visibility tied to file changes rather than as individual app or user action tracking.
Pros
- Real-time sync status shows what each device is uploading and downloading
- Detailed logs record sync attempts, errors, and completion results
- Open-source design supports self-hosting and full transparency into activity
- Fine-grained bandwidth throttling helps keep monitoring stable during transfers
Cons
- Activity is file-and-device centric, not per-user or per-application
- Initial setup and secure device pairing can be time-consuming
- Monitoring requires reading logs and interpreting sync timelines
- No built-in reporting for compliance-style dashboards and audit trails
Best For
Teams needing device-level file sync activity visibility with log-based audit trails
Conclusion
After evaluating 10 security, ActivTrak stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right User Activity Monitoring Software
This buyer's guide helps you pick the right User Activity Monitoring Software using concrete evaluation points across ActivTrak, Teramind, Securonix User and Entity Behavior Analytics, Veriato, Verint, Nextiva, Hubstaff, RescueTime, DeskTime, and Syncthing. It maps monitoring scope, investigation workflows, and alerting behavior to the teams these tools are best suited for. You will use the same checklist to narrow options for app and website governance, endpoint investigations, voice and contact center oversight, and device-level file sync activity tracking.
What Is User Activity Monitoring Software?
User Activity Monitoring Software records and analyzes end-user or user-adjacent behavior so teams can investigate activity, detect suspicious patterns, and support audit and compliance needs. The category ranges from app and website visibility in tools like ActivTrak to endpoint and behavior analytics in Teramind and Veriato. Many deployments use monitoring signals to trigger alerts and to organize evidence into investigation-ready timelines. Other solutions focus on specific workflows such as voice and contact center activity in Nextiva and evidence-based time tracking with screenshots in Hubstaff.
Key Features to Look For
The features below determine whether monitoring becomes usable investigation evidence or noisy logs that teams cannot act on.
Policy-based alerts tied to activity thresholds
ActivTrak delivers policy-based alerts that trigger on defined activity thresholds across users and apps. Teramind also converts monitored user actions into actionable alerts using configurable policy controls.
Investigation-ready timelines and searchable activity evidence
ActivTrak provides searchable activity logs and custom dashboards that support investigation-ready reporting. Veriato focuses on a strong event and activity timeline that helps teams review endpoint behavior evidence with centralized case review.
Behavior analytics and risk scoring for suspicious patterns
Teramind combines monitoring with behavior analytics so suspicious behavior can be prioritized through policy controls. Securonix User and Entity Behavior Analytics adds behavior-based risk scoring across authentication and access activity to reduce noise during investigations.
Governed audit trails with case management workflows
Verint emphasizes enterprise audit trail features and case management and investigator workflows tied to captured user activity events. ActivTrak also supports audit-focused monitoring with activity logs that support governance and compliance reviews.
Scope that matches your environment instead of generic telemetry
Nextiva concentrates on VoIP and contact center workflows and surfaces agent and call activity analytics in its contact center dashboards. Hubstaff focuses on app and website usage plus screenshot capture tied to time tracking and idle detection, which fits distributed workforce oversight and evidence collection.
Productivity-focused monitoring with goals and category-based controls
RescueTime tracks application and website usage into custom or predefined productivity levels and supports focus goals and distraction blocking by category. DeskTime pairs automatic app and website tracking with idle time alerts designed to flag inactive users inside timesheet workflows.
How to Choose the Right User Activity Monitoring Software
Use the steps below to match your monitoring scope, investigation workflow, and alerting needs to the specific strengths of each tool.
Start with the activity scope you actually need to monitor
If you need governance-grade visibility across applications and websites, start with ActivTrak because it monitors employee and user activity across apps and websites with analytics and investigation-ready logs. If you need endpoint and regulated workflow visibility, shortlist Teramind or Veriato because both focus on endpoint and behavioral patterns rather than simple login telemetry. If your oversight is primarily voice and agent performance, choose Nextiva because it captures call and agent activity signals like recordings and call outcomes tied to users.
Choose an alerting model that supports action, not just detection
For alerting that maps directly to investigation triggers, prioritize ActivTrak for policy-based alerts across users and apps. For behavior-driven detection and policy-based alerts tied to monitored user actions, prioritize Teramind. For SOC-style detection with identity context, evaluate Securonix User and Entity Behavior Analytics because its behavior-based risk scoring ties anomalous activity to identity and device context.
Confirm that investigations can be organized into evidence timelines
If investigations need searchable logs and custom dashboards, use ActivTrak because it supports custom dashboards and searchable activity logs. If your workflow requires centralized case review built around monitored behavior events, use Veriato because it includes centralized case review and audit-style evidence timelines. If your organization requires case management for investigators, evaluate Verint because it ties case management and investigator workflows to captured user activity events.
Match reporting complexity to your admin capacity and rollout plan
If you can invest time in setup and tuning across multiple departments, consider ActivTrak, Teramind, Veriato, or Verint because each delivers deep monitoring that can require training or admin effort. If you want lightweight productivity monitoring with clear daily and weekly reporting, use RescueTime or DeskTime because both are built around category-based insights and idle alerts with reporting designed for day to day review. If you need evidence-based time tracking and attendance checks, choose Hubstaff because it combines screenshot capture with timestamps, idle detection, and automated timesheets.
Validate coverage for nonstandard activity sources
If your real requirement is device-to-device file activity rather than app and user behavior, choose Syncthing because it provides per-device synchronization status and detailed logs showing transfer start, outcome, and errors. If you are monitoring distributed work but your key signals are app usage and inactivity, choose Hubstaff, RescueTime, or DeskTime because each turns app and website tracking into alerts, idle detection, and reporting tied to focus or attendance workflows.
Who Needs User Activity Monitoring Software?
User Activity Monitoring Software fits a range of teams because tools vary from governance-grade user activity auditing to productivity analytics to device-level file sync monitoring.
Mid-market and enterprise governance teams that need app and website audit-grade visibility
ActivTrak fits this segment because it monitors employee and user activity across applications and websites with custom dashboards, searchable activity logs, and policy-based alerts tied to user and app activity thresholds. Teramind can also fit governance-heavy security teams due to its configurable policy controls, investigation timelines, and audit-oriented monitoring.
Security teams monitoring regulated workflows across distributed endpoints
Teramind is built for this segment because it captures endpoint and session-level activity, applies configurable policies, and supports timeline-based event reviews for investigations. Veriato also fits because it provides policy-driven monitoring and behavioral analytics that score suspicious patterns for investigation prioritization.
SOC teams that want UEBA-style detections integrated into investigations
Securonix User and Entity Behavior Analytics fits this segment because it correlates user and entity signals and produces investigation-focused alerts with contextual risk scoring. It is especially appropriate when authentication and access activity must be analyzed with identity and device context to reduce investigation noise.
Large enterprises that require investigation workflows tied to governed audit trails
Verint fits this segment because it emphasizes enterprise-grade audit trail features and investigator workflows tied to captured user activity events. ActivTrak can be a strong alternative for teams that want audit-focused monitoring across apps and websites with policy-based alerts and searchable logs.
Contact center teams that need user activity visibility for calls and agent workflows
Nextiva fits this segment because it concentrates on VoIP and contact center activity and provides dashboards for agent and call activity analytics. It also supports audit-ready review through call recordings and call outcome metrics tied to users.
Distributed teams that need evidence-based time tracking and activity proof
Hubstaff fits this segment because it combines screenshot capture with time tracking, idle detection, and automated timesheets and project tagging for organizing monitoring data. DeskTime also fits teams that want app and idle monitoring paired with timesheet support for periodic approval workflows.
Individuals and small teams that want productivity insights without invasive surveillance
RescueTime fits this segment because it turns passive computer activity tracking into actionable productivity insights with time breakdowns, focus goals, and distraction blocking by category. It is a better fit than deep incident investigation tools when the primary objective is time spent analysis rather than governed audit investigations.
Teams that need device-level file sync activity visibility rather than per-user app activity
Syncthing fits this segment because it is designed around real-time device-to-device synchronization events and detailed per-node logs. It provides per-device synchronization status and log history for transfer outcomes and errors, which is aligned with file sync auditing rather than user action monitoring.
Common Mistakes to Avoid
These pitfalls show up across the tools because monitoring depth, alert tuning, and privacy impact differ sharply by solution.
Choosing broad deep monitoring when you actually need a narrow workflow
If your oversight requirement is primarily call and agent performance, choosing a general user activity monitor can leave gaps in telephony signals. Nextiva provides agent and call activity analytics tied to contact center workflows, which directly matches that need.
Launching policy alerts without planning for tuning and baseline behavior
Deep monitoring tools like Teramind, Veriato, and Securonix require policy or baseline tuning to avoid excessive alert volume. ActivTrak also supports policy-based alerts, but its advanced analysis can require training to configure well.
Expecting file sync tools to deliver app and user behavior auditing
Syncthing monitors device-level file synchronization and detailed transfer logs, not per-user or per-application actions. If you need app and website investigations, tools like ActivTrak and Teramind provide the correct behavior granularity.
Using screenshot capture when your privacy posture cannot support it
Hubstaff includes screenshot capture tied to time tracking, which can feel intrusive for teams with strict privacy needs. DeskTime offers optional screenshots and pairs monitoring with idle alerts, so you can reduce privacy impact by aligning configuration with team expectations.
How We Selected and Ranked These Tools
We evaluated ActivTrak, Teramind, Securonix User and Entity Behavior Analytics, Veriato, Verint, Nextiva, Hubstaff, RescueTime, DeskTime, and Syncthing across overall capability, feature depth, ease of use, and value fit for their intended use cases. We separated stronger options by how directly they turn monitoring signals into investigation workflows, which is why ActivTrak stands out with policy-based alerts plus searchable activity logs and audit-focused monitoring. We also penalized tools when setup and tuning require significant administrator effort for organizations that need rapid rollout, which is consistent with the operational overhead called out across Teramind, Veriato, Securonix, and Verint. We treated scope alignment as a major differentiator by giving dedicated workflow tools like Nextiva and productivity tools like RescueTime their own strengths rather than forcing them into the same capability expectations as governed audit platforms.
Frequently Asked Questions About User Activity Monitoring Software
How do ActivTrak and Teramind differ in how they create alerts for unusual employee behavior?
ActivTrak uses policy-based alerts that trigger when defined activity thresholds across users and apps are met. Teramind expands beyond thresholds by adding behavior analytics and mapping monitored end-user actions into alerts, dashboards, and investigation timelines.
Which tools are best suited for SOC workflows, including anomaly detection and case handling?
Securonix User and Entity Behavior Analytics focuses on UEBA with behavior-based risk scoring tied to authentication and access activity, producing investigation-ready signals for SOC triage. Verint adds case-driven investigation workflows that connect captured user activity events to session-level monitoring and security-focused alerting.
What’s the best option for compliance investigations that require audit-ready timelines rather than just login telemetry?
Veriato tracks digital work patterns across endpoints with behavioral analytics, then ties activity to centralized case review and alerting for incident investigation timelines. Veriato’s coverage is designed to support audit-ready evidence during investigations, not only basic login events.
How do Nextiva and contact center monitoring differ from endpoint app monitoring tools like ActivTrak or Hubstaff?
Nextiva centers monitoring on VoIP and contact center workflows, capturing call and agent performance signals such as call outcomes and recording-related metrics tied to users. ActivTrak and Hubstaff focus on application, website, and user activity patterns on endpoints and don’t provide the same call-centered interaction visibility.
When teams need evidence for productivity and idle time, which tools provide the strongest operational signals?
Hubstaff combines user activity monitoring with screenshots, app and website usage tracking, and idle time detection that feeds automatic work summaries. DeskTime provides idle time alerts and team or individual activity reporting that updates with minimal manual input.
Which tool is better for productivity-only monitoring with low intrusiveness, such as tracking time sinks without investigative timelines?
RescueTime is built for passive computer activity tracking that categorizes apps and websites into productivity levels and generates automated day and week reports. It supports focus goals and distraction control by category rather than investigator workflows like Verint or Teramind.
How does Securonix reduce alert noise compared with tools that mainly report activity logs?
Securonix uses UEBA-style modeling across users, endpoints, and identities to detect anomalies and attach identity and device context to detections. This context-aware approach targets investigations with less noise than simple activity log review.
What are the integration and workflow considerations when using tools that support SIEM or case management?
Securonix is designed for SOC environments and integrates behavior analytics into SIEM workflows and case handling. Verint and Teramind both emphasize governance workflows, including investigator-facing timelines and administrative oversight tied to monitored activity.
Can Syncthing be used as user activity monitoring, and what does it actually capture compared to app-level monitoring tools?
Syncthing captures device-to-device synchronization events and per-node log history, including transfer start and outcomes. It works best as device-level activity visibility tied to file changes rather than individual app actions like those tracked in ActivTrak or Hubstaff.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Security alternatives
See side-by-side comparisons of security tools and pick the right one for your stack.
Compare security tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
