GITNUXSOFTWARE ADVICE
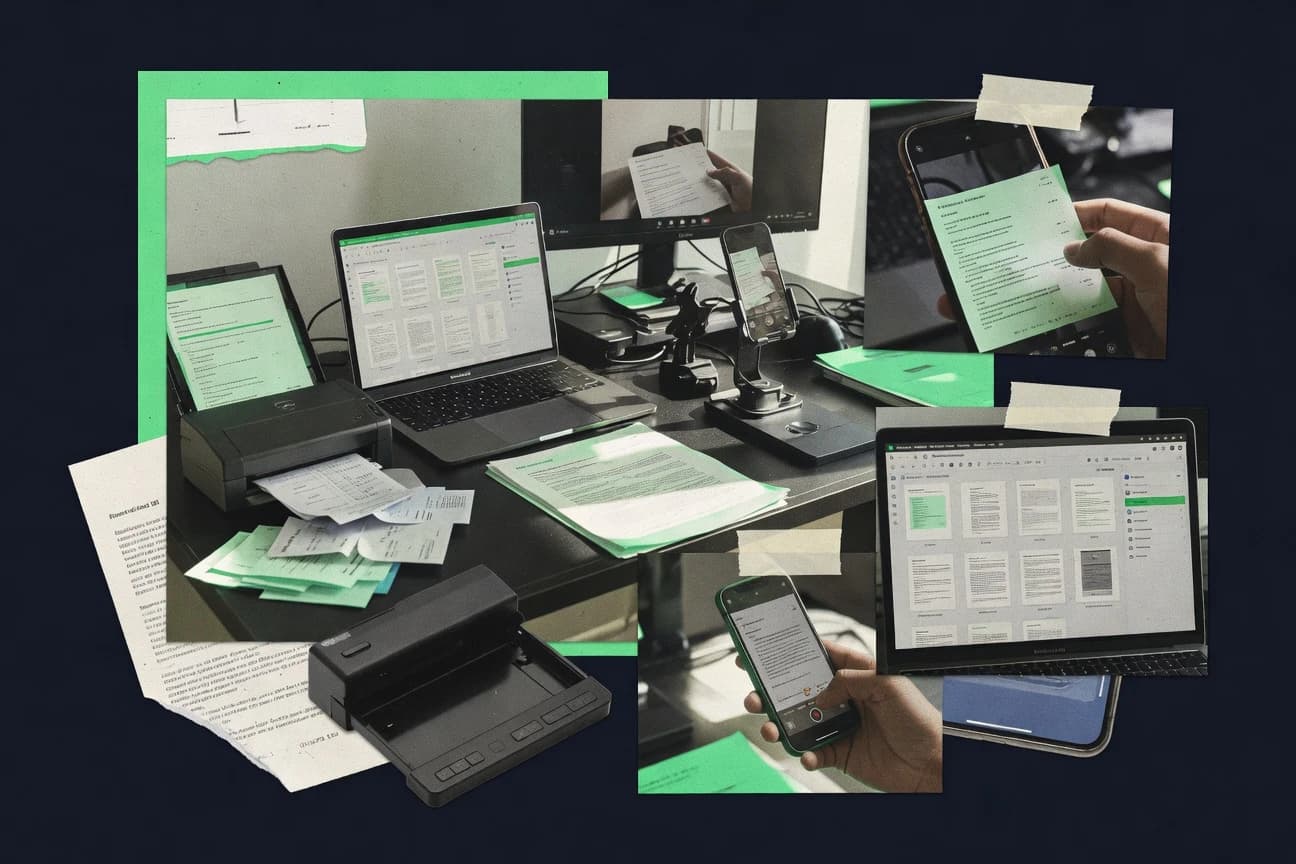
Technology Digital MediaTop 10 Best Remote Scanning Software of 2026
Discover top remote scanning software tools to streamline document management. Find your ideal fit today.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
Splunk Enterprise Security
Notable events from correlation searches that generate prioritized security findings
Built for enterprise SOC teams needing centralized remote detection and investigation.
Rapid7 InsightVM
Vulnerability validation plus risk-based prioritization using exposure and asset criticality
Built for security teams managing large endpoint fleets needing prioritized remote vulnerability scanning.
Tenable Nessus Professional
Authenticated scanning with detailed vulnerability evidence for accurate patch and configuration assessment
Built for security teams running recurring authenticated scans with compliance evidence.
Related reading
- Technology Digital MediaTop 10 Best Scanning Document Management Software of 2026
- Technology Digital MediaTop 10 Best Remote Computer Access Software of 2026
- Technology Digital MediaTop 10 Best Remote Working Tracking Software of 2026
- Technology Digital MediaTop 10 Best Remote Iot Device Management Software of 2026
Comparison Table
This comparison table evaluates remote scanning software used for vulnerability detection, misconfiguration checks, and exposure reporting across environments. It side-by-side maps key capabilities of tools such as Splunk Enterprise Security, Rapid7 InsightVM, Tenable Nessus Professional, Qualys, and OpenVAS so you can compare scanning scope, result accuracy, remediation workflows, and integration options.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | Splunk Enterprise Security Use endpoint, network, and vulnerability intelligence to support remote scanning workflows and centralized security triage. | SIEM-driven | 9.2/10 | 9.4/10 | 8.3/10 | 8.0/10 |
| 2 | Rapid7 InsightVM Run vulnerability scanning and asset-based risk detection with support for remote management and continuous assessment. | vulnerability | 8.6/10 | 9.1/10 | 7.8/10 | 8.2/10 |
| 3 | Tenable Nessus Professional Deploy remote vulnerability scanning to identify exposures and prioritize remediation across networks and systems. | vulnerability | 8.6/10 | 9.1/10 | 7.8/10 | 7.6/10 |
| 4 | Qualys Perform cloud-based vulnerability management with remote scanning, compliance workflows, and continuous security visibility. | cloud-managed | 8.2/10 | 9.0/10 | 7.4/10 | 7.8/10 |
| 5 | OpenVAS Run open-source vulnerability scanning with remote target assessment using the Greenbone Community Edition stack. | open-source | 7.4/10 | 8.6/10 | 6.8/10 | 8.2/10 |
| 6 | Greenbone Security Manager Manage remote vulnerability scans and reporting with a centralized platform for target assessment and remediation workflows. | enterprise-scanner | 8.1/10 | 8.6/10 | 7.4/10 | 8.3/10 |
| 7 | Nmap Use remote host discovery and port scanning with script-based checks to quickly map exposures across networks. | network-scanner | 7.6/10 | 8.8/10 | 6.6/10 | 8.4/10 |
| 8 | Acunetix Conduct remote web application vulnerability scanning and automated verification for attack surface findings. | web-scanner | 7.6/10 | 8.4/10 | 7.2/10 | 7.0/10 |
| 9 | Netsparker Scan web applications for remotely discoverable vulnerabilities with automated issue validation and reporting. | web-scanner | 8.1/10 | 8.7/10 | 7.6/10 | 7.4/10 |
| 10 | Vuls Use a lightweight vulnerability scanner that supports remote checks against target software versions and packages. | lightweight | 6.9/10 | 7.1/10 | 6.6/10 | 7.0/10 |
Use endpoint, network, and vulnerability intelligence to support remote scanning workflows and centralized security triage.
Run vulnerability scanning and asset-based risk detection with support for remote management and continuous assessment.
Deploy remote vulnerability scanning to identify exposures and prioritize remediation across networks and systems.
Perform cloud-based vulnerability management with remote scanning, compliance workflows, and continuous security visibility.
Run open-source vulnerability scanning with remote target assessment using the Greenbone Community Edition stack.
Manage remote vulnerability scans and reporting with a centralized platform for target assessment and remediation workflows.
Use remote host discovery and port scanning with script-based checks to quickly map exposures across networks.
Conduct remote web application vulnerability scanning and automated verification for attack surface findings.
Scan web applications for remotely discoverable vulnerabilities with automated issue validation and reporting.
Use a lightweight vulnerability scanner that supports remote checks against target software versions and packages.
Splunk Enterprise Security
SIEM-drivenUse endpoint, network, and vulnerability intelligence to support remote scanning workflows and centralized security triage.
Notable events from correlation searches that generate prioritized security findings
Splunk Enterprise Security stands out with deep security analytics built on Splunk indexing and search, plus correlation that maps events to known attack behaviors. It supports remote security monitoring workflows by collecting logs and security telemetry, normalizing fields, and using dashboards for investigation across many endpoints and networks. It also includes guided detection and response use cases through correlation searches and notable events, which helps security teams triage remotely without manual log spelunking. As a remote scanning solution, it is strongest when your “scan” inputs come from centralized telemetry sources like SIEM logs, endpoint detection, and vulnerability scanner exports.
Pros
- Rich correlation rules and notable events accelerate remote triage
- Dashboards and drilldowns support investigation across distributed data sources
- Extensive search and field extraction improves detection coverage
- Scales well with large log volumes for enterprise SOC operations
Cons
- Requires strong Splunk tuning to reduce noise and improve signal
- Remote scanning outputs depend on log quality and integration completeness
- Implementation and administration effort can be high for smaller teams
Best For
Enterprise SOC teams needing centralized remote detection and investigation
More related reading
Rapid7 InsightVM
vulnerabilityRun vulnerability scanning and asset-based risk detection with support for remote management and continuous assessment.
Vulnerability validation plus risk-based prioritization using exposure and asset criticality
Rapid7 InsightVM stands out for combining vulnerability scanning with strong compliance and risk prioritization workflows built for enterprise environments. It performs agentless scans and also supports authenticated checks to improve accuracy for Windows, Linux, and network device discovery. The platform maps findings to vulnerability categories and exports evidence for reporting, enabling teams to focus remediation by asset criticality and exposure. Its breadth of scan coverage and remediation context make it a strong remote scanning option for security operations teams managing large fleets.
Pros
- Authenticated scanning improves detection accuracy across endpoints and hosts
- Risk and exposure context helps prioritize remediation by business impact
- Compliance-focused reporting supports audit evidence generation
- Broad integrations fit security operations workflows and ticketing processes
Cons
- Initial configuration and tuning takes time for large environments
- Reporting setup can require expertise to match stakeholder expectations
- Scan performance may require careful scheduling to avoid bottlenecks
Best For
Security teams managing large endpoint fleets needing prioritized remote vulnerability scanning
Tenable Nessus Professional
vulnerabilityDeploy remote vulnerability scanning to identify exposures and prioritize remediation across networks and systems.
Authenticated scanning with detailed vulnerability evidence for accurate patch and configuration assessment
Tenable Nessus Professional stands out for its vulnerability scanning depth across networks, hosts, and web-facing services using a large plugin set. It delivers authenticated scanning options, CIS and compliance-oriented checks, and rich evidence-style reports for remediation workflows. Nessus also supports scheduled scans and centralized management through Tenable-compatible tooling, which helps keep remote scanning consistent across environments. The platform is strongest when you need repeatable coverage and actionable findings from internal and external assets.
Pros
- High-fidelity vulnerability detection with extensive plugin coverage
- Authenticated scanning supports accurate results on patch state and misconfigurations
- Compliance checks like CIS guidance streamline governance reporting
- Scheduled scans enable repeatable remote scanning across changing assets
Cons
- Advanced configuration takes time for dependable scan performance
- Alerting and integrations rely on additional Tenable components for full workflows
- Licensing costs can be high for smaller teams with limited assets
Best For
Security teams running recurring authenticated scans with compliance evidence
More related reading
Qualys
cloud-managedPerform cloud-based vulnerability management with remote scanning, compliance workflows, and continuous security visibility.
Qualys Policy Compliance with audit evidence tied to validated control checks
Qualys stands out with highly automated vulnerability and configuration assessment delivered through agent and agentless scanning options. It combines vulnerability management, threat detection, and compliance reporting in a single workflow that supports asset discovery, scan scheduling, and remediation prioritization. Its Remote Scanning capabilities focus on discovering exposed services, validating weaknesses against checks, and producing audit-ready evidence. The platform is stronger for organizations that want centralized governance across many networks than for teams needing lightweight point tools.
Pros
- Strong vulnerability validation with extensive checks and repeatable scan policies
- Unified dashboards for findings, remediation tracking, and compliance evidence
- Flexible scanning modes that support both agent-based and agentless coverage
- Deep reporting for audits using standardized compliance views
Cons
- Setup and tuning scans for accuracy can require specialist time
- Large environments can create heavy operational overhead for administrators
- Licensing complexity can make budgeting difficult for smaller teams
Best For
Enterprises standardizing remote vulnerability scanning and compliance reporting at scale
OpenVAS
open-sourceRun open-source vulnerability scanning with remote target assessment using the Greenbone Community Edition stack.
Greenbone Security Feed NVT updates power extensive vulnerability detection.
OpenVAS stands out as a community-driven vulnerability scanner built around the Greenbone Security Feed and the NVT library. It supports authenticated and unauthenticated remote scanning over standard network services and produces detailed findings with severity and evidence. Its web interface, scanner management, and reporting help coordinate scans and track results across hosts. It runs as self-hosted software with a focus on enterprise-style control rather than lightweight cloud scanning.
Pros
- Rich vulnerability coverage via Greenbone Security Feed and NVT library
- Supports authenticated scanning to improve accuracy for real hosts
- Detailed reports with severity, scan context, and evidence output
Cons
- Self-hosting and setup complexity can slow initial deployment
- Resource-heavy scans can strain CPU, memory, and network links
- Less polished UI workflows than commercial remote scanning platforms
Best For
Organizations running self-hosted vulnerability scanning with authenticated depth
Greenbone Security Manager
enterprise-scannerManage remote vulnerability scans and reporting with a centralized platform for target assessment and remediation workflows.
Credentialed remote vulnerability scanning with reusable scan profiles and target management
Greenbone Security Manager focuses on remote vulnerability management by coordinating authenticated and unauthenticated scans against assets. It provides report-driven workflows with role-based access and configurable scan schedules, which helps teams turn scan results into tracked remediation tasks. The product pairs well with Greenbone Community Edition for setting up management and reporting while keeping centralized control of targets, credentials, and scan policies. It also supports integration paths for exporting findings and feeding other security processes.
Pros
- Authenticated scanning with credential management improves accuracy for remote findings
- Centralized scan scheduling and reporting supports repeatable vulnerability workflows
- Strong policy configuration for targets, scan profiles, and result handling
Cons
- Setup and tuning require time to model assets and scan credentials correctly
- Dashboard workflows are less streamlined than some purpose-built SaaS scanners
- Integration and export options may need additional engineering for complex pipelines
Best For
Teams managing vulnerability scans on internal infrastructure with credentialed accuracy
More related reading
Nmap
network-scannerUse remote host discovery and port scanning with script-based checks to quickly map exposures across networks.
Nmap Scripting Engine with NSE modules for automated enumeration, checks, and validation
Nmap stands out for its scriptable network discovery and security auditing engine built around fast port scanning. It runs as a remote scanning tool by initiating scans from your scanner host to target IPs, ranges, and domain-resolved hosts. Core capabilities include TCP SYN scanning, UDP scanning, service and version detection, OS fingerprinting, and extensive NSE script support for verification and enumeration. It also supports scan scheduling modes via command-line automation and output formats that integrate with reporting pipelines.
Pros
- Accurate TCP SYN scanning with fine-grained timing and rate control
- Service and version detection using probes and fingerprint libraries
- OS fingerprinting and robust NSE scripting for deep enumeration
- Output formats support automation into logs and reporting workflows
Cons
- Requires command-line expertise to build reliable scan profiles
- High scan noise and overhead can occur without careful tuning
- Not a GUI-first remote scanning platform for non-engineers
- Reporting and remediation workflows require external tooling
Best For
Teams running scanner hosts and automation pipelines for repeatable network discovery
Acunetix
web-scannerConduct remote web application vulnerability scanning and automated verification for attack surface findings.
Authenticated scanning with session handling for verified findings behind application logins
Acunetix stands out for highly accurate web vulnerability scanning that focuses on real HTTP responses and issue validation instead of generic crawl results. It supports authenticated scans for areas behind logins, plus continuous recurring scans so teams can track remediations over time. The platform includes WAF-evasion aware crawling, vulnerability verification, and detailed findings with proof details for security and app teams. Its remote scanning approach is well suited to managing multiple targets and scan schedules from a central interface.
Pros
- Accurate vulnerability validation reduces false positives versus simple rule-based scanners
- Authenticated scanning supports complex apps behind login and session workflows
- Recurring scan scheduling supports continuous monitoring and remediation tracking
- Crawl and detection handle dynamic web behavior with WAF awareness
- Detailed issue evidence helps developers reproduce findings
Cons
- Setup for authenticated scanning and scan scope takes time
- Reporting and workflows can feel heavier for small teams
- Remote scanning value drops when you only need a few basic checks
Best For
Application security teams running authenticated web scans across multiple production targets
More related reading
Netsparker
web-scannerScan web applications for remotely discoverable vulnerabilities with automated issue validation and reporting.
Automated Proof-Based Scanning verifies vulnerabilities with reproducible evidence screenshots
Netsparker stands out with crawler-based remote scanning and built-in verification that aims to reduce false positives. It supports authenticated scanning so it can test areas behind logins and session flows. The tool generates actionable findings with risk context and evidence screenshots to speed remediation workflows. It also integrates scanning schedules and reports for recurring exposure assessment across applications.
Pros
- Automated vulnerability verification reduces false positives for reported issues
- Authenticated scanning tests logged-in areas and session-reliant pages
- Evidence-driven reports include reproducible details for faster remediation
Cons
- Advanced scan configuration takes time for teams without security tooling experience
- Larger app scopes can slow scans and increase operational overhead
- Reporting and collaboration features lag behind top-tier application security platforms
Best For
Security teams running periodic remote scans with authenticated coverage and evidence-based reporting
Vuls
lightweightUse a lightweight vulnerability scanner that supports remote checks against target software versions and packages.
Scan result organization that supports repeatable remote scanning and remediation tracking
Vuls focuses on remote security scanning workflows that emphasize quick visibility into findings and repeatable checks. The platform supports vulnerability scanning and tracking for external-facing assets and internal targets with results organized for remediation. It also provides reporting and audit-friendly exports so teams can share scan progress and outcomes with stakeholders. The experience is strongest for teams that want operational scanning cadence rather than deep manual lab-style testing.
Pros
- Structured scan results that help track issues through remediation cycles
- Reporting and exports support sharing findings with non-technical stakeholders
- Remote scanning workflows fit ongoing vulnerability management schedules
- Asset and scan organization reduces time spent locating prior results
Cons
- Workflow setup can feel heavy compared with simpler scanner dashboards
- Limited depth for advanced customization of scanning logic
- Remediation guidance is less prescriptive than leading vulnerability platforms
- UI can require extra clicks to move from findings to action
Best For
Teams needing recurring remote vulnerability scans with clear reporting
Conclusion
After evaluating 10 technology digital media, Splunk Enterprise Security stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Remote Scanning Software
This buyer’s guide explains how to pick remote scanning software using concrete examples from Splunk Enterprise Security, Rapid7 InsightVM, Tenable Nessus Professional, Qualys, OpenVAS, Greenbone Security Manager, Nmap, Acunetix, Netsparker, and Vuls. You will see which feature types matter, who each tool fits best, how pricing typically works, and where teams usually make avoidable selection mistakes.
What Is Remote Scanning Software?
Remote scanning software tests systems and applications that are not physically present by pulling target inputs such as network ranges, host inventories, and credentialed service checks. It solves exposure discovery and validation by producing evidence-rich findings like patch status gaps in Tenable Nessus Professional and authenticated web issues in Acunetix and Netsparker. Many teams also use it for recurring scans that turn results into remediation workflows with scheduling and reporting in Qualys and Greenbone Security Manager. Enterprise SOC and security operations teams use tools like Splunk Enterprise Security to centralize remote triage from security telemetry and correlation-driven notable events.
Key Features to Look For
Remote scanning outcomes depend on how reliably each tool can validate findings, prioritize risk, and fit your workflow and reporting expectations.
Notable events and correlation-driven prioritization for remote triage
Splunk Enterprise Security elevates scan-adjacent findings by generating prioritized results from correlation searches and notable events. This reduces manual log investigation for distributed endpoints and networks when your scan “inputs” come from SIEM and endpoint security telemetry.
Authenticated scanning with credential management for higher-fidelity results
Tenable Nessus Professional, Rapid7 InsightVM, Qualys, Greenbone Security Manager, OpenVAS, Acunetix, and Netsparker all emphasize authenticated checks that improve accuracy versus unauthenticated discovery. Greenbone Security Manager pairs credentialed remote scanning with reusable scan profiles and target management for repeatable execution.
Risk-based prioritization using exposure and asset criticality
Rapid7 InsightVM maps findings into prioritization context so teams focus remediation by business impact and exposure. This is especially useful when you manage large endpoint fleets because evidence and risk framing help decide what to fix first.
Compliance and audit-ready evidence tied to validated checks
Qualys provides Policy Compliance with audit evidence tied to validated control checks, which supports governance reporting at scale. Tenable Nessus Professional also delivers compliance-oriented checks and evidence-style reporting for patch and configuration assessment.
Automated validation to reduce false positives in web scanning
Acunetix validates issues using real HTTP responses and proof details instead of generic crawl results. Netsparker further reduces false positives with automated Proof-Based Scanning that includes reproducible evidence screenshots for remediation.
Scriptable discovery and repeatable network enumeration for scanner-host workflows
Nmap focuses on remote host discovery and port scanning with TCP SYN scanning, OS fingerprinting, and extensive NSE script modules. This makes it a strong fit for teams that run scanner hosts and automation pipelines and want outputs that integrate into logs and reporting.
How to Choose the Right Remote Scanning Software
Match your remote scanning goals to tool strengths in validation, prioritization, workflow integration, and deployment model.
Start with your target type and validation depth
Choose Tenable Nessus Professional, Rapid7 InsightVM, Qualys, or Greenbone Security Manager when you need authenticated vulnerability checks across Windows, Linux, and network device discovery. Choose Acunetix or Netsparker when your target is web applications and you need authenticated scanning plus verification that produces proof details or evidence screenshots.
Decide how you want results prioritized and turned into action
Use Rapid7 InsightVM when risk-based prioritization must reflect exposure and asset criticality for large endpoint fleets. Use Splunk Enterprise Security when you want correlation searches and notable events to generate prioritized findings for remote SOC triage from centralized security telemetry.
Plan for compliance reporting and evidence requirements
Use Qualys when audit-ready evidence must be tied to validated control checks through Policy Compliance views. Use Tenable Nessus Professional when CIS and compliance-oriented checks must be paired with authenticated scanning evidence for recurring governance assessments.
Choose your operating model and integration path
Use OpenVAS and Greenbone Security Manager when you want self-hosted control and credentialed scan orchestration paired with asset and policy configuration. Use Nmap when you need free and open-source remote discovery and port scanning that you can run from scanner hosts and automate through command-line workflows.
Validate implementation effort against your team capacity
Splunk Enterprise Security and Qualys require strong setup and tuning to reduce noise and operational overhead when data quality and integration completeness vary. Rapid7 InsightVM, Tenable Nessus Professional, and Greenbone Security Manager require configuration time in large environments and credential modeling to avoid bottlenecks and inaccurate coverage.
Who Needs Remote Scanning Software?
Remote scanning software fits teams that must discover exposures remotely, validate them with higher fidelity checks, and drive remediation using repeatable workflows.
Enterprise SOC teams centralizing remote security triage
Splunk Enterprise Security fits teams that already centralize security telemetry and want remote triage accelerated by notable events from correlation searches. It is strongest when scan inputs come from SIEM logs, endpoint detection, and vulnerability scanner exports across many distributed sources.
Security teams managing large endpoint fleets with prioritized vulnerability remediation
Rapid7 InsightVM fits teams that need agentless scanning plus authenticated checks to improve accuracy for Windows, Linux, and network devices. It helps teams prioritize remediation by mapping vulnerabilities to exposure and asset criticality for large fleets.
Security teams running recurring authenticated scans with compliance evidence
Tenable Nessus Professional fits teams that need repeatable coverage from scheduled scans and authenticated checks that produce detailed vulnerability evidence. It also includes compliance-oriented checks like CIS guidance to streamline governance reporting.
Enterprises standardizing remote vulnerability management and audit reporting at scale
Qualys fits enterprises that want centralized governance with vulnerability and configuration assessment across many networks and scan policies. It pairs automated scanning modes with Qualys Policy Compliance for audit evidence tied to validated control checks.
Pricing: What to Expect
Nmap is free and open-source with no paid tiers or per-user licensing, and commercial support is sold by third parties. Splunk Enterprise Security is paid enterprise software with pricing dependent on deployment size and support needs, and you must contact sales for a quote because implementation and indexing infrastructure can add cost. Rapid7 InsightVM, Tenable Nessus Professional, Qualys, Greenbone Security Manager, Acunetix, Netsparker, and Vuls all start paid plans at $8 per user monthly billed annually, with enterprise pricing available on request for larger deployments. OpenVAS does not price community availability, and enterprise support and deployments are sold through vendors, so cost typically depends on your chosen vendor package.
Common Mistakes to Avoid
Common pitfalls come from mismatching scanner depth to target type, underestimating setup effort, and expecting remediation workflows without the right evidence and integration path.
Buying a scanner without authenticated coverage when credentials matter
Web and host accuracy drops when scans run without authenticated checks for logins or patch state, which is why Tenable Nessus Professional and Rapid7 InsightVM emphasize authenticated scanning. Acunetix and Netsparker also require session handling for verified findings behind application logins.
Underestimating tuning work that reduces noise and prevents operational bottlenecks
Splunk Enterprise Security needs strong Splunk tuning to reduce noise and improve signal for remote triage. Qualys, Rapid7 InsightVM, and Tenable Nessus Professional also require configuration and scheduling care in large environments to avoid heavy operational overhead or scan performance bottlenecks.
Expecting a full remediation workflow from the scanner UI alone
Nmap is strong for discovery and enumeration but its reporting and remediation workflows require external tooling because it is not a GUI-first platform. Vuls provides structured result organization for remediation tracking, but advanced customization and prescriptive remediation guidance are less complete than leading vulnerability platforms.
Ignoring evidence requirements for compliance and stakeholder communication
Qualys is built for audit-ready evidence through Qualys Policy Compliance with validated control checks. Tenable Nessus Professional and Netsparker provide evidence-style outputs like authenticated vulnerability evidence and proof-based evidence screenshots to support governance and faster developer action.
How We Selected and Ranked These Tools
We evaluated Splunk Enterprise Security, Rapid7 InsightVM, Tenable Nessus Professional, Qualys, OpenVAS, Greenbone Security Manager, Nmap, Acunetix, Netsparker, and Vuls using four rating dimensions: overall, features, ease of use, and value. We separated Splunk Enterprise Security from lower-ranked options by prioritizing practical remote triage acceleration, because it generates prioritized security findings from correlation searches and notable events while supporting dashboards and drilldowns across distributed telemetry. We also weighted feature depth that directly reduces false positives or improves confidence, such as authenticated scanning evidence in Tenable Nessus Professional and Rapid7 InsightVM and automated proof validation in Acunetix and Netsparker. We considered implementation friction using ease of use and value dimensions because tools like OpenVAS and Splunk Enterprise Security can require more setup effort than purpose-built vulnerability workflows.
Frequently Asked Questions About Remote Scanning Software
Which remote scanning tools are best for enterprise SOC workflows that need centralized investigation from existing telemetry?
Splunk Enterprise Security fits SOC teams that want remote scanning inputs from centralized telemetry like SIEM logs and endpoint detection outputs, then correlated prioritization via notable events. Rapid7 InsightVM and Tenable Nessus Professional also support large-fleet scanning, but they focus more on vulnerability and risk workflows than SOC-style investigation dashboards.
What tool choice makes the biggest difference between vulnerability scanning and web application scanning?
Use Acunetix for web vulnerability scanning that validates issues from real HTTP responses and supports authenticated sessions behind logins. Use Tenable Nessus Professional or Qualys for host and network vulnerability and compliance checks that produce audit-ready evidence.
When should I use authenticated remote scans instead of unauthenticated scans?
Tenable Nessus Professional and Rapid7 InsightVM support authenticated scanning to improve accuracy for Windows, Linux, and network device discovery. Greenbone Security Manager is designed for credentialed remote vulnerability scanning with reusable scan profiles and target management, which is critical when exposed details require valid credentials.
Which options offer a free starting point for remote scanning?
Nmap is free and open-source and supports script-driven remote scanning with TCP SYN, UDP, service detection, and OS fingerprinting. OpenVAS is community-driven with NVT updates via the Greenbone Security Feed, but enterprise support and deployments are sold through vendors.
How do Splunk Enterprise Security and vulnerability scanners handle prioritization and triage after scans?
Splunk Enterprise Security prioritizes by correlating security events into known attack behaviors and generating notable events for investigation without manual log spelunking. Rapid7 InsightVM prioritizes by mapping findings into vulnerability categories and combining exposure context with asset criticality to guide remediation.
What technical setup differences should I expect for self-hosted scanners versus SaaS-style scanning?
OpenVAS and Greenbone Security Manager are typically deployed as self-hosted components with a management layer for scheduling and reporting, which requires local infrastructure planning. Splunk Enterprise Security and Qualys are commonly integrated with existing environments and central governance workflows, which changes the operational burden from hosting to configuration and onboarding.
Which tool is strongest for repeatable, scheduled scans across large environments?
Tenable Nessus Professional supports scheduled scans and centralized management patterns through Tenable-compatible tooling so recurring coverage stays consistent. Qualys provides automated scan scheduling and compliance evidence generation for standardized remote vulnerability assessment across many networks.
How can I reduce false positives during remote scanning?
Netsparker reduces false positives by combining crawler-based discovery with built-in verification and Proof-Based Scanning that produces reproducible evidence screenshots. Acunetix improves verification by focusing on real HTTP responses and validating findings instead of relying on generic crawl results.
What should I choose if I need quick visibility and remediation tracking across recurring scans?
Vuls emphasizes operational remote scanning cadence with results organized for remediation, plus reporting and audit-friendly exports for stakeholder updates. Greenbone Security Manager also supports report-driven workflows with role-based access and configurable scan schedules that convert scan results into tracked remediation tasks.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Technology Digital Media alternatives
See side-by-side comparisons of technology digital media tools and pick the right one for your stack.
Compare technology digital media tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
