GITNUXSOFTWARE ADVICE
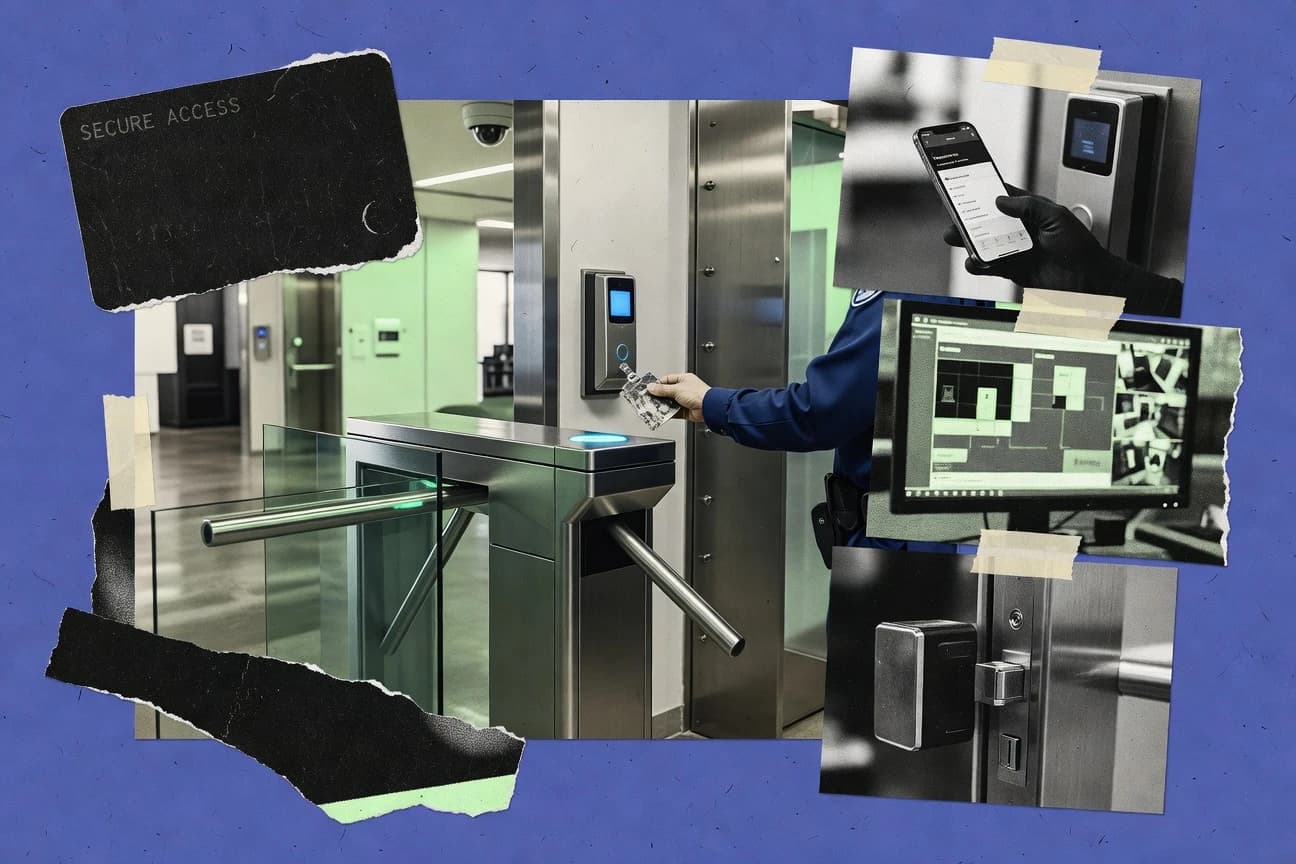
SecurityTop 10 Best Physical Access Control Software of 2026
Explore the top 10 physical access control software solutions. Compare features and find your ideal fit today.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor’s top 3 picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
2N Access Commander
Centralized device event monitoring and reporting across 2N controllers in one interface
Built for organizations standardizing on 2N hardware for multi-door access control management.
Brivo Access
Brivo hosted connectivity for controller-to-cloud communication and remote monitoring
Built for multi-site teams needing centralized access control with strong auditability.
CDVI Controller Software
Controller event logging tied to credentials and access schedules across connected doors
Built for organizations managing door access using CDVI controllers and schedules.
Related reading
Comparison Table
This comparison table evaluates physical access control software options such as 2N Access Commander, Brivo Access, CDVI Controller Software, ExacqVision, and LenelS2 OnGuard. Each entry summarizes core capabilities like credential and door control, user management, alarm and event handling, and how the system integrates with cameras and other security components.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | 2N Access Commander Centralizes management of physical access using 2N door controllers and access control hardware through a software command center. | door-controller management | 8.2/10 | 8.4/10 | 7.9/10 | 8.3/10 |
| 2 | Brivo Access Manages physical access permissions and mobile or credential-based entry for doors and access control systems. | cloud access management | 8.0/10 | 8.4/10 | 7.6/10 | 7.7/10 |
| 3 | CDVI Controller Software Provides configuration and monitoring for CDVI access control hardware and controllers used for physical entry points. | controller configuration | 7.1/10 | 7.4/10 | 6.9/10 | 7.0/10 |
| 4 | ExacqVision Combines video surveillance with access control events by integrating with compatible access systems for incident response. | video-driven access | 7.4/10 | 7.6/10 | 7.3/10 | 7.3/10 |
| 5 | LenelS2 OnGuard Enables enterprise physical access control via integrated door control, credentialing, and alarm handling. | enterprise on-prem access | 8.1/10 | 8.8/10 | 7.2/10 | 7.9/10 |
| 6 | Openpath Manages cloud-based mobile and credential access workflows for multi-tenant buildings using compatible locks and controllers. | cloud access control | 7.6/10 | 7.6/10 | 8.2/10 | 6.9/10 |
| 7 | SALTO KS Orchestrates keyless access by controlling digital keys, permissions, and audit trails for SALTO electronic locks. | keyless digital control | 7.4/10 | 7.6/10 | 6.9/10 | 7.8/10 |
| 8 | S2 NetBox Operates as a central management and integration platform for access control, combining events, credentials, and alarm data. | integration platform | 8.0/10 | 8.3/10 | 7.6/10 | 8.0/10 |
| 9 | Tyco Software House C-CURE 9000 Supports enterprise physical security with credentialing, access rules, door control, and event workflows. | enterprise access security | 7.1/10 | 7.6/10 | 6.4/10 | 7.2/10 |
| 10 | Tyco Software House C-CURE 800 Provides physical access control for mid-sized deployments with centralized rules, schedules, and alarm monitoring. | mid-market access security | 7.1/10 | 7.6/10 | 6.4/10 | 7.0/10 |
Centralizes management of physical access using 2N door controllers and access control hardware through a software command center.
Manages physical access permissions and mobile or credential-based entry for doors and access control systems.
Provides configuration and monitoring for CDVI access control hardware and controllers used for physical entry points.
Combines video surveillance with access control events by integrating with compatible access systems for incident response.
Enables enterprise physical access control via integrated door control, credentialing, and alarm handling.
Manages cloud-based mobile and credential access workflows for multi-tenant buildings using compatible locks and controllers.
Orchestrates keyless access by controlling digital keys, permissions, and audit trails for SALTO electronic locks.
Operates as a central management and integration platform for access control, combining events, credentials, and alarm data.
Supports enterprise physical security with credentialing, access rules, door control, and event workflows.
Provides physical access control for mid-sized deployments with centralized rules, schedules, and alarm monitoring.
2N Access Commander
door-controller managementCentralizes management of physical access using 2N door controllers and access control hardware through a software command center.
Centralized device event monitoring and reporting across 2N controllers in one interface
2N Access Commander stands out by centering on 2N door controllers and integrating access control with a workflow-style management experience. The product supports user and credential management, door and time-profile configuration, and centralized event monitoring from connected devices. It also provides reporting and administrative controls aimed at operators managing multiple entrances from one console. The overall solution fits physical access deployments that prioritize reliable device integration over highly generic integrations.
Pros
- Strong focus on managing 2N door controllers from a central console
- Centralized event monitoring with practical reporting for day-to-day operations
- Time profiles and access rules enable detailed scheduling per door
- Administrative workflows support managing users and door permissions cleanly
- Designed for real-world site operations with clear device-centric organization
Cons
- Best results depend on using compatible 2N hardware for full coverage
- Advanced custom integrations require additional effort beyond core management
- Initial setup can be configuration-heavy for larger multi-building sites
Best For
Organizations standardizing on 2N hardware for multi-door access control management
More related reading
Brivo Access
cloud access managementManages physical access permissions and mobile or credential-based entry for doors and access control systems.
Brivo hosted connectivity for controller-to-cloud communication and remote monitoring
Brivo Access stands out for browser-based physical access management that pairs with hosted controller connectivity. It supports credential-based door control, real-time event monitoring, and multi-location supervision through a centralized system. Admins can configure rules for access schedules and automate responses to incidents using integrations that extend beyond basic door status. The platform targets distributed sites where cardholder governance and audit trails matter as much as day-to-day access control.
Pros
- Cloud-managed access control reduces on-site controller maintenance overhead.
- Centralized multi-location administration supports unified cardholder and door policies.
- Real-time event logs provide strong audit trails for access and door activity.
Cons
- Advanced workflows often require careful system design across doors and schedules.
- Integrations can add complexity for environments needing deep custom logic.
Best For
Multi-site teams needing centralized access control with strong auditability
CDVI Controller Software
controller configurationProvides configuration and monitoring for CDVI access control hardware and controllers used for physical entry points.
Controller event logging tied to credentials and access schedules across connected doors
CDVI Controller Software stands out by serving as a controller-centric access management tool built around CDVI hardware integrations for doors and zones. It supports core physical access control functions like user credential management, access schedules, and event logging tied to connected controllers. The system’s practical strength is centralizing monitoring and control for installations that need consistent behavior across multiple access points. It also emphasizes integration workflows rather than standalone enterprise identity features.
Pros
- Strong CDVI hardware integration for door control and controller-based workflows
- Access schedules and credential assignment support consistent time-based access
- Centralized event logs help troubleshooting and audit review for connected hardware
Cons
- Interface complexity can slow configuration for multi-site or high-door-count deployments
- Advanced enterprise features like deep identity federation are not a primary focus
- Usability depends heavily on installer-led setup and correct controller mapping
Best For
Organizations managing door access using CDVI controllers and schedules
ExacqVision
video-driven accessCombines video surveillance with access control events by integrating with compatible access systems for incident response.
Video and access event correlation for investigation-ready incident timelines
ExacqVision stands out by merging video surveillance management with physical access workflows in one operator experience. It supports credential reader integrations, alarm handling, and event-driven responses tied to doors and zones. The platform emphasizes centralized monitoring for security teams that need consistent audit trails across access activity and video evidence. Core deployments rely on site-specific hardware and integrations rather than a fully self-contained access panel experience.
Pros
- Event-driven access and alarm workflows tied to camera views
- Centralized investigations with synchronized video playback for access incidents
- Scales across multi-site deployments with unified operator monitoring
Cons
- Access control configuration depends heavily on supported hardware integration
- User workflows can feel complex without standardized operating procedures
- Advanced customization requires deeper system administration effort
Best For
Security teams needing unified video evidence and access event management
LenelS2 OnGuard
enterprise on-prem accessEnables enterprise physical access control via integrated door control, credentialing, and alarm handling.
OnGuard LenelS2 event and alarm workflows that coordinate actions across integrated security devices
LenelS2 OnGuard stands out for its deep enterprise physical security lineage and wide ecosystem support across access control, video, and intrusion integration. Core capabilities include role-based access management, configurable alarm and event workflows, and support for credential and reader-based control across multiple sites. The platform also provides centralized reporting with audit trails and integrates with common security systems to coordinate response actions.
Pros
- Strong enterprise integration with access control, video, and alarms workflows
- Centralized event reporting and audit trails for investigations and compliance
- Scalable architecture for multi-site deployments and complex access rules
Cons
- Configuration depth can slow rollout for smaller facilities and limited teams
- System design choices require experienced administrators to avoid misconfiguration
- Workflow customization can increase ongoing admin overhead
Best For
Enterprises needing scalable access control integrations across sites and security domains
Openpath
cloud access controlManages cloud-based mobile and credential access workflows for multi-tenant buildings using compatible locks and controllers.
Mobile app access control for unlocking doors using managed credentials
Openpath centers physical access control on smartphone-based credentials combined with door hardware integrations. It supports granting access, managing schedules, and administering users across locations through a cloud-managed system. Core capabilities include door-level control, access rules, and operational tools for onboarding and managing people in near real time.
Pros
- Mobile-first access credentials reduce reliance on physical keycards
- Cloud administration enables rapid access changes without site visits
- Door-level scheduling supports common building access policies
Cons
- Best results depend on compatible door and reader hardware availability
- Advanced enterprise workflows and integrations can require specialized implementation
- Multi-site governance features are less robust than top-tier access platforms
Best For
Small to mid-size teams managing door access with mobile credentials
More related reading
SALTO KS
keyless digital controlOrchestrates keyless access by controlling digital keys, permissions, and audit trails for SALTO electronic locks.
Centralized access scheduling and rules management tied to SALTO controller hardware
SALTO KS stands out by centering physical access control around SALTO’s electronic locking ecosystem. The platform manages credentials, schedules, and access rules through centralized administration that connects to SALTO controllers. It also supports event monitoring and audit trails for door activity tied to users, systems, and time profiles.
Pros
- Strong alignment with SALTO electronic locks and controllers
- Centralized scheduling, credential management, and access rules
- Door events and audit trails support troubleshooting and compliance
Cons
- Configuration complexity rises with larger multi-site deployments
- Broader integration options can be limited outside SALTO environments
- Role and workflow setup can feel procedural for small teams
Best For
Organizations standardizing on SALTO locks for managed access control
S2 NetBox
integration platformOperates as a central management and integration platform for access control, combining events, credentials, and alarm data.
Rule-based access permissions linked to door controller and alarm event workflows
S2 NetBox focuses on physical access management by combining credential control with door and alarm integration for facility security workflows. The system supports rule-based access permissions, event logging, and configurable hardware integration for card or credential readers tied to access points. It also provides administrative tooling for managing identities and access rights across multiple areas, rather than treating access as a standalone door feature.
Pros
- Strong door-level access control tied to configurable hardware integrations
- Detailed event logging supports auditing across access attempts and alarm events
- Centralized identity and access right management across multiple locations
Cons
- Configuration depth can slow setup for multi-site deployments
- User permissions and workflow tuning require careful administrative planning
- Interface learning curve is higher than simpler access systems
Best For
Organizations managing multiple doors and alarm events with disciplined access administration
Tyco Software House C-CURE 9000
enterprise access securitySupports enterprise physical security with credentialing, access rules, door control, and event workflows.
Rule-based access control with centralized door and reader event processing across sites.
Tyco Software House C-CURE 9000 stands out as a legacy enterprise access control platform built around database-centered system control and centralized site management. It supports cardholder and credential management, configurable door and reader monitoring, and rule-based access and anti-passback style behaviors for physical security workflows. Administrators can manage alarm inputs, integrate with field hardware, and coordinate events across doors and systems under a unified software suite. Large deployments benefit from mature operational patterns, but the platform typically demands careful configuration and experienced system administration to maintain performance and correctness.
Pros
- Strong enterprise controls for door schedules, reader logic, and access rules
- Centralized event and alarm management across multi-door deployments
- Proven fit for complex physical security operations and integration-heavy environments
Cons
- Setup and tuning require experienced administrators and consistent database practices
- User experience is less modern than newer access platforms
- Complex configurations increase risk of misconfigurations without disciplined change control
Best For
Enterprise security teams running door-heavy sites with existing Tyco hardware.
Tyco Software House C-CURE 800
mid-market access securityProvides physical access control for mid-sized deployments with centralized rules, schedules, and alarm monitoring.
Advanced event and alarm correlation tied directly to access and door activity
C-CURE 800 from Tyco Software House is a security management platform designed around enterprise-style physical access control workflows and device integration. It supports credential and door control logic across distributed hardware, plus alarm monitoring and event reporting tied to access activity. The system is built for large deployments that need configurable policies, centralized oversight, and operational audit trails across sites.
Pros
- Strong enterprise-grade access control with centralized policy management
- Detailed event and alarm handling tied to door and credential activity
- Supports distributed integrations for multi-site access control deployments
Cons
- Configuration and administration can feel heavy for smaller operations
- User interfaces require training for day-to-day controller and alarm work
- Integrations and system design depend heavily on installer expertise
Best For
Enterprise teams managing multi-site access control with centralized monitoring
Conclusion
After evaluating 10 security, 2N Access Commander stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Physical Access Control Software
This buyer's guide explains how to select physical access control software using concrete examples from 2N Access Commander, Brivo Access, LenelS2 OnGuard, Openpath, SALTO KS, S2 NetBox, ExacqVision, CDVI Controller Software, and Tyco Software House C-CURE 9000 and C-CURE 800. It focuses on device connectivity, centralized event visibility, identity and credential workflows, scheduling rules, and incident-ready reporting. It also covers common setup pitfalls that show up with controller mapping, multi-site configuration depth, and integration scope.
What Is Physical Access Control Software?
Physical access control software centralizes user and credential management for door readers and controllers, plus schedules and rules that decide when access is granted. It also consolidates event logs so operators can audit access attempts and investigate alarms with consistent timelines. Solutions like Brivo Access handle cloud-managed permissions with real-time event monitoring across multiple locations. Controller-centric tools like 2N Access Commander and CDVI Controller Software focus on configuring and monitoring door controllers and their connected access behavior from a central console.
Key Features to Look For
Evaluating these capabilities against real deployment needs prevents slow rollouts, misconfiguration risk, and weak operational visibility once doors go live.
Centralized event monitoring and audit-ready reporting
Event visibility across controllers and doors is the core operational requirement for day-to-day access administration. 2N Access Commander and Brivo Access emphasize centralized event monitoring and reporting across connected devices and locations. S2 NetBox and LenelS2 OnGuard further strengthen auditability by combining event logging with rule-based access administration and audit trails.
Door scheduling with time profiles and rule-based access logic
Door-level scheduling determines when credentials unlock and how access windows align to roles. 2N Access Commander provides time profiles and access rules per door, while SALTO KS centralizes access scheduling and rules tied to SALTO controller hardware. S2 NetBox and Tyco Software House C-CURE 9000 focus on rule-based access permissions that coordinate access decisions across doors and events.
Credential and identity administration with clean user-to-door permissions
Credential administration must support user assignment, credential changes, and consistent permission governance across multiple entrances. 2N Access Commander includes administrative workflows for user and door permission management. Brivo Access centralizes multi-location supervision for cardholder governance and audit trails, while LenelS2 OnGuard adds role-based access management for large-scale identity-driven security programs.
Controller integration model that matches installed hardware
Access control software must integrate reliably with the controller ecosystem already deployed at doors and zones. 2N Access Commander is designed for centralized management of 2N door controllers, and CDVI Controller Software centers on CDVI controller integrations for door and zone control. SALTO KS similarly centers on SALTO electronic locks and controllers, while Tyco Software House C-CURE 9000 and C-CURE 800 align with enterprise deployments that use Tyco field hardware patterns.
Incident workflows with alarm handling and event correlation
Security operations need event correlation that connects access activity to alarms and other evidence. LenelS2 OnGuard coordinates event and alarm workflows across integrated security devices, and S2 NetBox ties rule-based access permissions to door controller and alarm event workflows. ExacqVision correlates video surveillance with access events so investigations can include synchronized video playback with incident timelines.
Multi-site administration for distributed teams and multiple entrances
Multi-site operations require centralized oversight so administrators can manage users, doors, and schedules without site-by-site handling. Brivo Access provides browser-based physical access management with hosted controller connectivity for remote monitoring across locations. Openpath enables cloud administration that supports near real-time onboarding and access changes across locations, and Openpath focuses on door-level control for smartphone credentials.
How to Choose the Right Physical Access Control Software
The selection process should match the software integration model, operational workflows, and access credential format to the actual doors, controllers, and security process.
Map software to the controller and lock ecosystem already on the doors
If the installed hardware is 2N, 2N Access Commander is built around centralized management of 2N door controllers and connected access devices. If the installed hardware is CDVI, CDVI Controller Software centers on controller-centric configuration and monitoring tied to CDVI integrations for doors and zones. If the lock ecosystem is SALTO, SALTO KS is aligned to SALTO electronic locks and controllers with centralized credential schedules and door event monitoring.
Define the operational workflow for access events and incident handling
If security teams need access evidence tied to camera context, ExacqVision is built to correlate video surveillance with access and alarm workflows using compatible access system integrations. If the organization runs coordinated security device response, LenelS2 OnGuard provides event and alarm workflows that coordinate actions across integrated security devices. If the priority is access administration paired with alarms and audit trails, S2 NetBox links rule-based permissions to door controller and alarm event workflows.
Confirm the scheduling and rule model fits the access policy complexity
If policies vary by door and time window, 2N Access Commander supports time profiles and access rules per door so schedules can be granular. If policies emphasize mobile and credential-based access with door-level scheduling, Openpath supports door-level scheduling and cloud-managed credential workflows for managed unlocking. If the deployment relies on enterprise rule processing, Tyco Software House C-CURE 9000 supports rule-based access control with centralized door and reader event processing across sites.
Plan for admin roles, permissions, and identity workflows across your locations
Multi-location governance is strongest when the platform supports centralized administration and clear audit trails. Brivo Access centralizes multi-location supervision for unified cardholder and door policies with real-time event logs. LenelS2 OnGuard adds role-based access management and scalable multi-site integration across access, video, and alarms domains.
Stress-test configuration and integration effort for your deployment size
If door count and building count are high, verify that controller mapping and workflow setup can be completed without slowing rollout. CDVI Controller Software and Tyco Software House C-CURE 9000 both emphasize controller mapping and complex configuration workflows that depend on installer-led setup and disciplined administration. For environments that demand rapid access changes with less on-site administration, Openpath and Brivo Access emphasize cloud-managed configuration and remote monitoring for operational agility.
Who Needs Physical Access Control Software?
Physical access control software fits teams that need centralized permission governance, reliable controller connectivity, and operational visibility across doors and events.
Organizations standardizing on a single controller ecosystem
2N Access Commander is a strong fit for teams standardized on 2N door controllers because centralized device event monitoring and reporting is built around 2N hardware. CDVI Controller Software fits organizations using CDVI controllers for consistent door and zone behavior tied to credentials and access schedules. SALTO KS fits organizations standardized on SALTO locks because centralized scheduling and rules management are tied to SALTO controller hardware.
Multi-site teams that need cloud-managed access administration and strong audit trails
Brivo Access is designed for distributed sites using browser-based physical access management paired with hosted controller connectivity for remote monitoring and real-time event logs. Openpath fits small to mid-size teams managing door access with mobile-first credentials because it supports cloud administration for rapid access changes without site visits. Both options provide centralized event visibility that helps teams maintain audit trails across locations.
Security operations teams that must investigate incidents with video and access timelines
ExacqVision is built for unified operator monitoring by correlating video surveillance with access events and alarm workflows tied to doors and zones. This improves investigations because operators can link access activity to video evidence in a consistent workflow.
Enterprises coordinating access control with alarms and other security devices
LenelS2 OnGuard fits enterprises needing scalable access control integrations across sites and security domains because it coordinates event and alarm workflows across integrated security devices. S2 NetBox fits organizations managing multiple doors and alarm events with disciplined access administration because it provides rule-based access permissions linked to door controller and alarm event workflows. Tyco Software House C-CURE 9000 and C-CURE 800 fit enterprise security teams managing door-heavy sites using existing Tyco hardware patterns with centralized event and alarm correlation.
Common Mistakes to Avoid
Several recurring pitfalls show up when deployments mismatch software integration scope, operational workflow needs, or administration maturity.
Selecting software that does not match the installed door hardware ecosystem
2N Access Commander delivers best results when deployments use compatible 2N door controllers because it is centered on centralized management of 2N hardware. CDVI Controller Software depends heavily on correct CDVI controller mapping, which can slow setup when hardware is mixed. SALTO KS similarly relies on SALTO electronic lock and controller environments for full coverage.
Underestimating multi-site configuration depth and workflow tuning
LenelS2 OnGuard offers deep enterprise workflows, and configuration depth can slow rollout for smaller facilities and limited teams. S2 NetBox provides detailed rule-based access administration tied to hardware integrations, and interface learning curve increases when administrators are not prepared. Tyco Software House C-CURE 9000 and C-CURE 800 both require experienced system administration to maintain correct behavior in complex installations.
Ignoring the operational need for incident correlation between access events and alarms or video
ExacqVision is designed to correlate video and access events for investigation-ready incident timelines, so teams that need evidence correlation can lose time with tools that focus only on access logs. LenelS2 OnGuard and S2 NetBox emphasize alarm-aware workflows, so skipping those capabilities can weaken incident response. Tyco Software House C-CURE 800 and C-CURE 9000 both emphasize event and alarm correlation tied to door and credential activity.
Designing advanced access workflows without disciplined governance across doors and schedules
Brivo Access can require careful system design for advanced workflows across doors and schedules, especially in environments with complex incident response requirements. Openpath supports mobile-first credentials and cloud administration, but advanced enterprise workflows and integrations can require specialized implementation for large governance models. S2 NetBox requires careful administrative planning because user permissions and workflow tuning directly affect access enforcement outcomes.
How We Selected and Ranked These Tools
We evaluated every tool using three sub-dimensions, features with weight 0.4, ease of use with weight 0.3, and value with weight 0.3. The overall rating is the weighted average computed as overall = 0.40 × features + 0.30 × ease of use + 0.30 × value. 2N Access Commander separated from lower-ranked options because its features score is anchored in centralized device event monitoring and reporting across 2N controllers in one interface, which directly supports operator workflows for door-heavy management. That device-centric operational visibility also improves day-to-day administration efficiency, which raised ease of use relative to tools that emphasize broader enterprise integration depth.
Frequently Asked Questions About Physical Access Control Software
Which physical access control software best fits organizations standardizing on a single door-controller ecosystem?
2N Access Commander is built around 2N door controllers and centers administration on device event monitoring, door configuration, and time profiles in one console. SALTO KS targets organizations standardizing on SALTO electronic locking by tying credential rules and schedules to SALTO controller hardware. CDVI Controller Software similarly centers on CDVI controller integrations for consistent door and zone behavior.
Which tools provide centralized access management for multiple locations with strong audit trails?
Brivo Access uses hosted connectivity to centralize credential-based door control, real-time event monitoring, and multi-location supervision with auditability. LenelS2 OnGuard supports enterprise reporting with audit trails and coordinates actions across access, video, and intrusion integrations. S2 NetBox provides administrative tooling for identities and access rights across multiple areas while logging events tied to door and alarm workflows.
Which physical access control platforms correlate access events with video evidence or alarm workflows?
ExacqVision merges video surveillance management with physical access workflows so events tied to doors and zones can be handled alongside video evidence. LenelS2 OnGuard supports alarm and event workflows that coordinate actions across integrated security systems. Tyco Software House C-CURE 800 and Tyco Software House C-CURE 9000 both tie alarm monitoring and event reporting directly to access activity.
Which solution is best for smartphone-based credentials and near-real-time onboarding across locations?
Openpath centers physical access control on smartphone-based credentials with door hardware integrations and cloud-managed user and schedule administration. It targets near-real-time operational onboarding and managing people across locations without relying on traditional card issuance flows. Brivo Access also supports centralized access schedules and incident response automation, but it is built around hosted controller connectivity rather than mobile-first credentials.
Which tools are strongest for disciplined rule-based access administration across doors and alarm events?
S2 NetBox focuses on rule-based access permissions linked to door controller and alarm event workflows, which helps keep governance consistent across multiple access points. Tyco Software House C-CURE 9000 emphasizes rule-based access behaviors like anti-passback and centralized site management for door-heavy deployments. Openpath supports rules and schedules, but it typically aligns more with teams that need mobile credential administration rather than deep anti-passback style logic.
What software options prioritize controller-centric monitoring instead of a fully self-contained access panel experience?
CDVI Controller Software is controller-centric and centralizes monitoring and control for doors and zones using connected CDVI controllers. 2N Access Commander provides centralized device event monitoring and reporting across connected 2N controllers with workflow-style administration. ExacqVision relies on site-specific hardware for its unified video and access event workflows rather than presenting a standalone access panel experience.
How do these platforms handle credential, user, and schedule management in day-to-day operations?
LenelS2 OnGuard supports role-based access management with configurable alarm and event workflows plus credential and reader-based control across multiple sites. SALTO KS centralizes access scheduling, credentials, and access rules through administration connected to SALTO controllers. Openpath manages user onboarding and door-level rules through a cloud-managed system that can update access permissions quickly.
Which enterprise platforms are better suited for large deployments that require mature operational patterns and careful administration?
Tyco Software House C-CURE 9000 is a legacy enterprise platform built around database-centered system control and centralized site management, which benefits large door-heavy installations. Tyco Software House C-CURE 800 is also designed for large deployments with configurable policies and centralized oversight tied to distributed hardware. Both Tyco platforms typically demand experienced system administration to keep configurations correct and performant.
What are common implementation pitfalls readers should plan for when selecting an access control software stack?
For controller ecosystem alignment, SALTO KS and 2N Access Commander work best when deployments standardize on their respective controller and locking ecosystems. For integration-heavy environments, LenelS2 OnGuard and ExacqVision require attention to how access events and alarms are correlated with reader status and video evidence. For distributed sites, Brivo Access and Openpath depend on reliable hosted connectivity and operational workflows that keep schedules and credentials consistent across locations.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Security alternatives
See side-by-side comparisons of security tools and pick the right one for your stack.
Compare security tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
