GITNUXSOFTWARE ADVICE
SecurityTop 10 Best Multi Factor Authentication Software of 2026
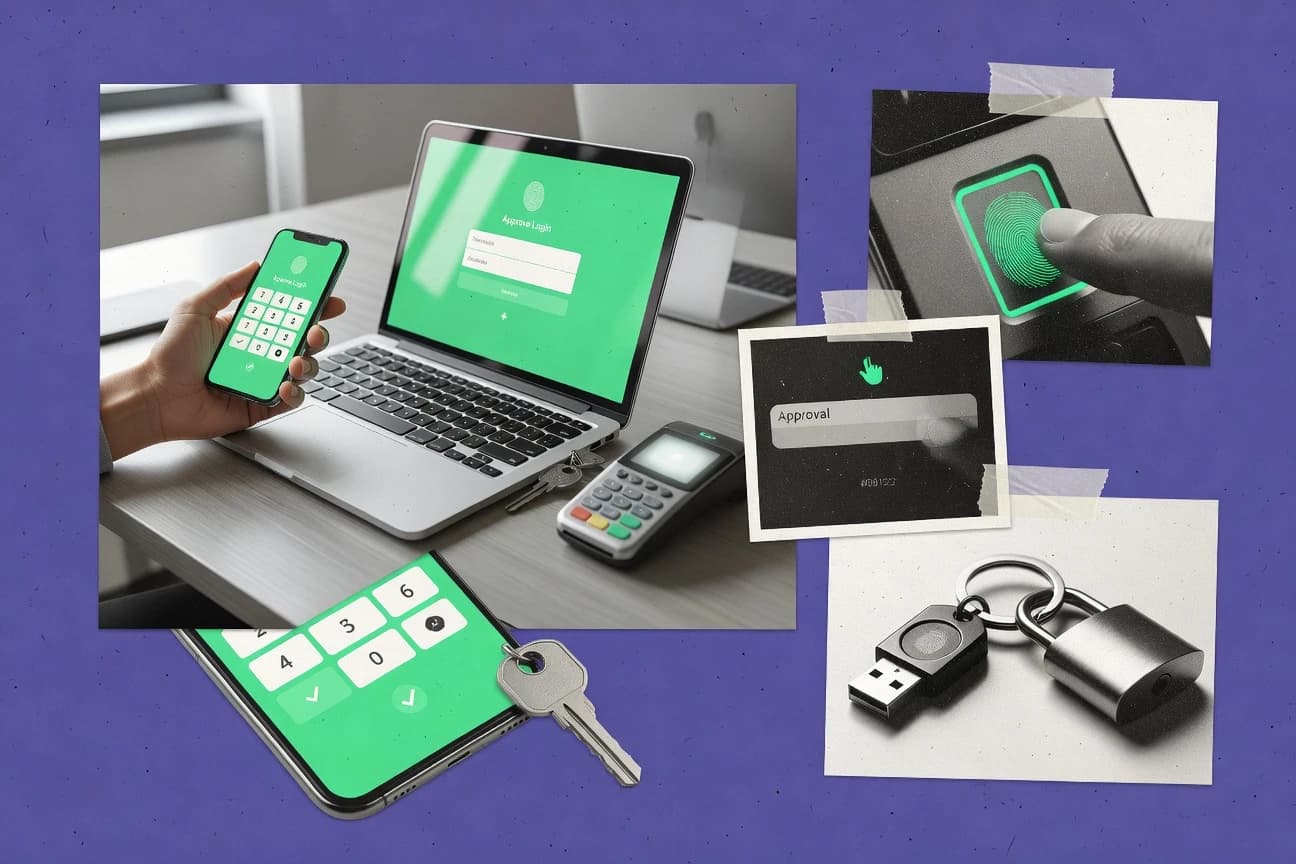
Discover the top 10 best multi factor authentication software to boost security. Protect your accounts effectively with our curated list. Explore now.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
Okta Workforce Identity Cloud
Conditional Access policies that trigger MFA based on risk signals and device posture
Built for enterprises needing policy based, phishing resistant MFA across many apps.
Microsoft Entra ID
Conditional Access with risk-based MFA and phishing-resistant authentication via FIDO2 security keys
Built for enterprises standardizing MFA with SSO, conditional access, and security key authentication.
Auth0
WebAuthn passkeys for phishing-resistant MFA
Built for teams needing MFA plus scalable authentication workflows across apps and APIs.
Related reading
Comparison Table
This comparison table evaluates multi factor authentication software across major identity platforms and dedicated MFA providers, including Okta Workforce Identity Cloud, Microsoft Entra ID, Auth0, Ping Identity, and Cisco Duo Security. You will compare setup and user enrollment paths, supported authentication methods, integration options with SSO and apps, policy controls, and operational features like reporting and admin workflows. Use the results to map each product’s strengths to your deployment and compliance requirements.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | Okta Workforce Identity Cloud Provides adaptive multi-factor authentication with policy controls, device context, and strong authenticator options for workforce and customer sign-in flows. | enterprise | 9.2/10 | 9.5/10 | 8.6/10 | 7.9/10 |
| 2 | Microsoft Entra ID Delivers multi-factor authentication and modern strong authentication with conditional access policies across enterprise applications. | enterprise | 8.9/10 | 9.2/10 | 7.9/10 | 8.3/10 |
| 3 | Auth0 Offers MFA and passwordless authentication with configurable risk-based policies for web, mobile, and enterprise identity workflows. | API-first | 8.3/10 | 9.1/10 | 7.6/10 | 7.9/10 |
| 4 | Ping Identity Implements MFA and strong authentication with centralized policy enforcement for access management and identity assurance. | enterprise | 8.4/10 | 9.1/10 | 7.2/10 | 7.6/10 |
| 5 | Cisco Duo Security Delivers reliable MFA using push approvals, passcodes, and authentication policy controls for workforce access and VPN logins. | MFA gateway | 8.7/10 | 9.1/10 | 7.9/10 | 8.2/10 |
| 6 | ForgeRock Identity Platform Provides MFA and identity policies within an enterprise identity platform for secure authentication, registration, and access. | enterprise | 7.4/10 | 8.7/10 | 6.8/10 | 6.9/10 |
| 7 | SecurEnvoy Provides OTP-based multi-factor authentication with SMS and email delivery plus strong enrollment and authentication policies. | OTP-focused | 7.4/10 | 7.6/10 | 7.2/10 | 7.5/10 |
| 8 | SuperOps Adds multi-factor authentication and identity protections for the operational layer by securing access to systems and accounts. | security add-on | 7.8/10 | 8.1/10 | 7.3/10 | 8.0/10 |
| 9 | Google Authenticator Supports time-based one-time passwords for MFA by generating codes in a mobile authenticator app. | TOTP client | 6.8/10 | 7.0/10 | 8.3/10 | 7.2/10 |
| 10 | FreeOTP Generates TOTP codes for multi-factor authentication using a lightweight authenticator application. | open-source | 6.8/10 | 6.5/10 | 8.2/10 | 9.0/10 |
Provides adaptive multi-factor authentication with policy controls, device context, and strong authenticator options for workforce and customer sign-in flows.
Delivers multi-factor authentication and modern strong authentication with conditional access policies across enterprise applications.
Offers MFA and passwordless authentication with configurable risk-based policies for web, mobile, and enterprise identity workflows.
Implements MFA and strong authentication with centralized policy enforcement for access management and identity assurance.
Delivers reliable MFA using push approvals, passcodes, and authentication policy controls for workforce access and VPN logins.
Provides MFA and identity policies within an enterprise identity platform for secure authentication, registration, and access.
Provides OTP-based multi-factor authentication with SMS and email delivery plus strong enrollment and authentication policies.
Adds multi-factor authentication and identity protections for the operational layer by securing access to systems and accounts.
Supports time-based one-time passwords for MFA by generating codes in a mobile authenticator app.
Generates TOTP codes for multi-factor authentication using a lightweight authenticator application.
Okta Workforce Identity Cloud
enterpriseProvides adaptive multi-factor authentication with policy controls, device context, and strong authenticator options for workforce and customer sign-in flows.
Conditional Access policies that trigger MFA based on risk signals and device posture
Okta Workforce Identity Cloud stands out for strong identity governance built around modern authentication flows and policy-driven access controls. It supports multi factor authentication with phishing resistant options like FastPass and WebAuthn, plus app sign in and user verification across enterprise apps. Administrators get centralized MFA enrollment, conditional access policies, and deep integration with directory sources and common SSO ecosystems. It is also strong for workforce lifecycle controls that help keep MFA aligned as users move through onboarding, role changes, and deprovisioning.
Pros
- Phishing resistant MFA options like FastPass and WebAuthn reduce credential theft risk
- Conditional access policies apply MFA based on risk, device, and user context
- Centralized enrollment and lifecycle controls keep MFA consistent across workforce changes
- Wide SSO and app integration coverage simplifies rolling out MFA to many apps
- Strong admin tooling for reporting, policy testing, and authentication troubleshooting
Cons
- Advanced workforce and authentication setups can be complex to design correctly
- Cost increases with scale due to enterprise licensing and add-on capabilities
- Some specialized MFA behaviors require configuration work and operational upkeep
Best For
Enterprises needing policy based, phishing resistant MFA across many apps
More related reading
Microsoft Entra ID
enterpriseDelivers multi-factor authentication and modern strong authentication with conditional access policies across enterprise applications.
Conditional Access with risk-based MFA and phishing-resistant authentication via FIDO2 security keys
Microsoft Entra ID stands out by bundling MFA with enterprise identity, conditional access, and SSO for Microsoft and non-Microsoft apps. It supports modern authentication methods like FIDO2 security keys, certificate-based authentication, and push or one-time password MFA. Conditional Access policies let you require MFA by user, app, device state, and risk signals. Reporting and integration with Microsoft security tooling support audit trails for authentication and policy decisions.
Pros
- Conditional Access enforces MFA by user, app, device, and sign-in risk
- FIDO2 security key support reduces phishing risk compared to OTP
- Strong SSO coverage for Microsoft apps and integrated third-party applications
- Detailed sign-in logs enable fast investigation of authentication failures
- Works well with device management signals to restrict access on unmanaged devices
Cons
- Policy design can be complex for organizations without existing identity governance
- Advanced configuration requires careful testing to avoid lockouts
- MFA method availability depends on licensing and tenant settings
- User experience varies across apps when integration is inconsistent
- Migration from legacy MFA providers can involve multiple moving parts
Best For
Enterprises standardizing MFA with SSO, conditional access, and security key authentication
Auth0
API-firstOffers MFA and passwordless authentication with configurable risk-based policies for web, mobile, and enterprise identity workflows.
WebAuthn passkeys for phishing-resistant MFA
Auth0 stands out for combining MFA enforcement with a full identity platform for web, mobile, and APIs. It supports multiple MFA methods including TOTP-based authenticator apps, SMS, and WebAuthn for phishing-resistant passkeys. Auth0 can require MFA at login or step-up during sensitive actions using authentication policies and rules. Its extensive SDK and standards support helps integrate MFA into existing applications with configurable user flows.
Pros
- Supports TOTP, SMS, and WebAuthn passkeys for strong MFA coverage
- Step-up authentication enables MFA only for sensitive actions
- Configurable user authentication flows fit web, mobile, and APIs
- Integrates with major identity and authentication standards
Cons
- MFA policy setup can feel complex for smaller teams
- Costs can rise quickly with high login volume and advanced features
- Custom rules increase maintenance burden for code-heavy deployments
Best For
Teams needing MFA plus scalable authentication workflows across apps and APIs
Ping Identity
enterpriseImplements MFA and strong authentication with centralized policy enforcement for access management and identity assurance.
Adaptive MFA with context-aware authentication policies in PingOne Identity Cloud
Ping Identity stands out for its enterprise-grade identity assurance approach to authentication and access control. Its PingOne and PingAccess offerings support multi-factor authentication with configurable policies across web, mobile, and enterprise applications. The platform integrates with directory services and integrates with existing IAM and risk signals to strengthen login decisions beyond simple OTP challenges. Its focus on protocol support and authentication orchestration makes it a strong fit for complex environments.
Pros
- Policy-driven MFA with flexible authentication chains
- Strong enterprise integration with directories and IAM ecosystems
- Broad protocol support for consistent authentication flows
Cons
- Setup and tuning require specialized identity engineering
- Higher total cost for organizations that only need basic MFA
- Complex deployments can increase time to production
Best For
Enterprises needing policy-based MFA orchestration across many applications
Cisco Duo Security
MFA gatewayDelivers reliable MFA using push approvals, passcodes, and authentication policy controls for workforce access and VPN logins.
Adaptive MFA policies driven by device trust and identity context
Cisco Duo Security stands out with strong MFA coverage for VPN, web apps, and administrative logins. It supports push approvals, one-time passcodes, and passkey-based authentication options to reduce phishing risk. Duo also provides adaptive policies, device trust signals, and detailed access logs for investigation and compliance. Its tight integration approach with common enterprise systems makes deployment predictable for IAM and network access use cases.
Pros
- Push MFA with fast user approvals and strong phishing resistance
- Policy controls combine identities, groups, device signals, and risk
- Works well for VPN, SSO, and admin access logins
- Comprehensive audit logs for security investigations
Cons
- Initial setup can be complex across multiple protected applications
- More advanced policy tuning requires deeper admin configuration
- Message-based notifications add operational dependency for some flows
Best For
Enterprises standardizing MFA for VPN, SSO, and administrator access
ForgeRock Identity Platform
enterpriseProvides MFA and identity policies within an enterprise identity platform for secure authentication, registration, and access.
Authentication trees that chain factors with conditional step-up based on policy and risk.
ForgeRock Identity Platform stands out with strong identity orchestration across authentication, authorization, and lifecycle flows. It supports MFA through configurable authentication trees, including WebAuthn, OTP, and out-of-band patterns that integrate with external factors. It also provides risk-based evaluation hooks so step-up authentication can trigger when sessions look suspicious. The platform targets enterprises that need centralized control across multiple channels and applications.
Pros
- Flexible authentication trees support complex step-up MFA journeys
- WebAuthn support enables strong phishing-resistant MFA options
- Unified identity and policy tooling reduces duplicated authentication logic
Cons
- MFA configuration requires deeper engineering and identity integration effort
- Setup and customization can be heavy for teams without IAM specialists
- Cost is high when you need full enterprise capabilities and scaling
Best For
Enterprises consolidating IAM and MFA across many applications and channels
More related reading
SecurEnvoy
OTP-focusedProvides OTP-based multi-factor authentication with SMS and email delivery plus strong enrollment and authentication policies.
Policy driven verification links that deliver OTP challenges based on user and group rules
SecurEnvoy focuses on identity verification flows that emphasize recipient control and operational flexibility for multi factor authentication. It supports OTP based challenges and verification links that administrators can tailor to user, group, and risk conditions. The product integrates with common authentication ecosystems and is designed for teams that need stronger login protection than password only access. Deployment is positioned for organizations that want MFA workflows without building custom authentication logic.
Pros
- OTP and verification link flows support multiple MFA challenge patterns
- Flexible policy targeting for users and groups reduces unnecessary prompts
- Clear administrative controls for enrollment and authentication enforcement
- Works for common enterprise MFA use cases without custom coding
Cons
- Fewer advanced authentication options than top MFA vendors
- Setup complexity increases when integrating with multiple identity sources
- Reporting depth is limited compared with security focused MFA platforms
Best For
Organizations needing practical OTP MFA with admin-managed challenge policies
SuperOps
security add-onAdds multi-factor authentication and identity protections for the operational layer by securing access to systems and accounts.
Conditional access policies tied to authentication context and user enrollment state
SuperOps focuses on multi-factor authentication workflows that support both IT control and developer-friendly operations. It provides centralized MFA policy management, conditional access options, and enrollment flows designed to reduce helpdesk tickets. The platform also emphasizes automated security response around authentication events and user onboarding. SuperOps is a strong fit for teams that want tighter identity security without heavy manual scripting.
Pros
- Centralized MFA policy control across users and apps
- Conditional access options for stronger authentication enforcement
- Automation helps reduce manual onboarding and access friction
- Authentication event handling supports faster security response
Cons
- Setup and tuning require more operational effort than basic MFA tools
- Advanced authentication workflow configuration can feel complex
- Limited out-of-the-box guidance for edge-case identity scenarios
Best For
Mid-size teams automating MFA enforcement with conditional access
Google Authenticator
TOTP clientSupports time-based one-time passwords for MFA by generating codes in a mobile authenticator app.
TOTP offline codes generated without internet connectivity
Google Authenticator stands out for offering simple time-based one-time passwords and quick code generation on mobile. It supports offline use for TOTP verification and uses QR code enrollment to link accounts to the app. The app can store multiple accounts in one interface and provides codes without network access. It has limitations for enterprise-scale administration because it focuses on user-held secrets rather than centralized fleet management.
Pros
- Fast TOTP code generation with offline support
- QR code enrollment streamlines adding new accounts
- Multiple issuer accounts in a single authenticator interface
Cons
- No built-in enterprise recovery workflow for lost devices
- Limited centralized admin controls for MFA enrollment
- Device migration depends on manual re-enrollment
Best For
Small teams needing free, offline TOTP MFA with minimal setup friction
FreeOTP
open-sourceGenerates TOTP codes for multi-factor authentication using a lightweight authenticator application.
Offline TOTP and HOTP code generation from QR-imported secrets
FreeOTP distinguishes itself with offline-friendly one-time password generation using simple TOTP and HOTP support. It stores secrets on your device and works with authenticator QR codes from major MFA providers. The core capability is generating changing six- to eight-digit codes for account logins without a cloud dependency. It also supports manual key entry for cases where QR codes are unavailable.
Pros
- Free and open-source, with TOTP and HOTP support
- Offline code generation reduces reliance on network connectivity
- Simple QR-code onboarding supports most authenticator workflows
Cons
- No built-in backup or migration tools for account recovery
- Limited enterprise controls like device enrollment and admin policies
- No audit logs or centralized management for MFA rollouts
Best For
Personal accounts needing free offline TOTP codes and quick setup
Conclusion
After evaluating 10 security, Okta Workforce Identity Cloud stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Multi Factor Authentication Software
This buyer’s guide helps you choose Multi Factor Authentication Software that fits your identity architecture and risk posture. It covers enterprise platforms like Okta Workforce Identity Cloud and Microsoft Entra ID as well as developer-friendly MFA platforms like Auth0. It also addresses simpler TOTP options like Google Authenticator and FreeOTP when offline authentication is the main requirement.
What Is Multi Factor Authentication Software?
Multi Factor Authentication Software enforces additional verification steps during sign-in using factors such as push approvals, one-time passcodes, authenticator apps, and phishing-resistant passkeys. It reduces account takeover risk by requiring more than a password and by applying MFA based on user, device posture, and sign-in context. Enterprises typically use tools like Okta Workforce Identity Cloud to apply Conditional Access policies across many apps. Organizations that already rely on SSO also use Microsoft Entra ID to combine MFA, conditional access, and FIDO2 security key sign-in for Microsoft and non-Microsoft applications.
Key Features to Look For
These features determine whether MFA is enforceable at scale, resistant to phishing, and operationally manageable during onboarding, changes, and investigations.
Risk-based Conditional Access that triggers MFA from context
Okta Workforce Identity Cloud and Cisco Duo Security can trigger MFA based on risk signals and device trust context, which reduces unnecessary prompts while strengthening high-risk sessions. Microsoft Entra ID also supports Conditional Access policies that require MFA by user, app, device state, and sign-in risk.
Phishing-resistant authentication with WebAuthn and security keys
Okta Workforce Identity Cloud includes phishing-resistant options like FastPass and WebAuthn, which reduces credential theft compared to OTP-only flows. Auth0 and Ping Identity support WebAuthn passkeys for phishing-resistant MFA, and Microsoft Entra ID supports FIDO2 security keys.
Step-up authentication for sensitive actions
Auth0 supports step-up authentication so MFA can be required only for sensitive actions instead of every login. ForgeRock Identity Platform can chain factors with conditional step-up based on policy and risk to enforce stronger verification during suspicious sessions.
Centralized MFA enrollment and workforce or user lifecycle controls
Okta Workforce Identity Cloud provides centralized MFA enrollment and lifecycle controls that keep MFA aligned during onboarding, role changes, and deprovisioning. Microsoft Entra ID and Ping Identity also support policy-driven enforcement across enterprise applications with centralized administration for consistent access decisions.
Authentication orchestration across apps and channels with strong protocol support
Ping Identity supports configurable policies across web, mobile, and enterprise applications through identity assurance and orchestration. ForgeRock Identity Platform supports flexible authentication trees that integrate with external factors, which helps when you need coordinated MFA behavior across multiple channels.
Operational auditability and investigation-ready sign-in logs
Microsoft Entra ID provides detailed sign-in logs that help investigate authentication failures and policy decisions. Cisco Duo Security also provides comprehensive audit logs and access logs for investigation and compliance needs.
How to Choose the Right Multi Factor Authentication Software
Choose the tool that matches your authentication workflows, your app footprint, and your risk and compliance requirements.
Start with your MFA goal: always-on verification or step-up MFA
If you want MFA enforced broadly during sign-in based on context, prioritize policy-driven Conditional Access like Okta Workforce Identity Cloud and Microsoft Entra ID. If you want MFA only when actions look risky, use Auth0 step-up authentication or ForgeRock Identity Platform authentication trees that trigger conditional step-up based on policy and risk.
Match phishing resistance requirements to supported factors
If phishing resistance is a priority, prioritize WebAuthn passkeys and security keys using tools like Okta Workforce Identity Cloud, Auth0, Ping Identity, and Microsoft Entra ID with FIDO2 security keys. If your environment needs strong adaptive policies before you roll out passkeys everywhere, Cisco Duo Security can combine push approvals with adaptive device trust driven policies.
Plan for enrollment and lifecycle operations
If you need MFA to remain consistent during onboarding, role changes, and deprovisioning, Okta Workforce Identity Cloud’s centralized enrollment and lifecycle controls fit workforce management workflows. If your team prefers MFA built into an existing SSO and conditional access program, Microsoft Entra ID provides Conditional Access enforcement across apps and device state signals.
Confirm integration fit for the apps and sign-in paths you run
If you must orchestrate authentication across web, mobile, and multiple enterprise applications, Ping Identity’s PingOne and PingAccess policy-driven approach is built for complex environments. If you are consolidating IAM and MFA logic across many applications and channels, ForgeRock Identity Platform’s unified identity and policy tooling helps reduce duplicated authentication logic.
Decide whether you need enterprise-grade administration or simple offline TOTP
If you need centralized MFA enrollment controls, audit logs, and policy management for enterprise sign-in, choose an enterprise identity platform like Microsoft Entra ID or Cisco Duo Security. If your requirement is offline TOTP generation for small teams or personal accounts, Google Authenticator and FreeOTP generate offline TOTP codes using authenticator apps and QR code enrollment.
Who Needs Multi Factor Authentication Software?
Different teams need MFA platforms for different reasons, from enterprise policy enforcement to developer workflows and offline TOTP support.
Enterprises rolling out phishing-resistant MFA across many workforce and customer apps
Okta Workforce Identity Cloud is a strong fit because it supports Conditional Access that triggers MFA based on risk and device posture plus phishing-resistant options like FastPass and WebAuthn. Enterprises standardizing this across many apps benefit from Okta’s wide SSO and app integration coverage with centralized enrollment and troubleshooting tools.
Enterprises standardizing MFA with SSO and conditional access for Microsoft and non-Microsoft apps
Microsoft Entra ID fits because it combines MFA with Conditional Access policies tied to user, app, device state, and sign-in risk. It also supports phishing-resistant FIDO2 security key authentication and includes detailed sign-in logs for investigation of authentication failures.
Teams building MFA into web apps, mobile apps, and APIs with step-up policies
Auth0 fits because it offers MFA methods including TOTP, SMS, and WebAuthn passkeys plus step-up authentication for sensitive actions. It also supports configurable user authentication flows and SDK integration for web, mobile, and APIs.
Organizations that want policy-based MFA orchestration with flexible authentication chains
Ping Identity fits organizations that need adaptive MFA with context-aware policies across many applications using PingOne Identity Cloud. ForgeRock Identity Platform fits when you need authentication trees that chain factors and trigger conditional step-up based on policy and risk across multiple channels.
Common Mistakes to Avoid
The most common failures come from selecting MFA factors and policy design approaches that do not match your authentication ecosystem and operational needs.
Using OTP-only MFA without a phishing-resistant migration path
If your threat model includes phishing, prioritize WebAuthn passkeys and security keys using tools like Okta Workforce Identity Cloud, Auth0, Ping Identity, and Microsoft Entra ID with FIDO2 security keys. Cisco Duo Security still provides strong adaptive policies with push approvals, but passkeys and security keys offer direct phishing-resistant authentication.
Overcomplicating policy design and risking lockouts
Microsoft Entra ID and Okta Workforce Identity Cloud both support advanced Conditional Access behavior tied to risk and device posture, and that complexity requires careful testing to avoid lockouts. Ping Identity and ForgeRock Identity Platform also support flexible authentication orchestration, which increases the need for tuning before broad deployment.
Skipping lifecycle controls when staff changes drive identity risk
Okta Workforce Identity Cloud’s centralized MFA enrollment and lifecycle controls prevent MFA drift across onboarding, role changes, and deprovisioning. If you do not plan for lifecycle behavior in your chosen platform, you may end up with inconsistent authentication enforcement across apps and user states.
Assuming offline TOTP apps provide enterprise management and recovery
Google Authenticator and FreeOTP generate offline TOTP codes with QR code onboarding, but they lack built-in enterprise recovery workflows and centralized admin policies. For enterprise environments that require centralized enforcement and investigation support, Cisco Duo Security and Microsoft Entra ID provide policy management and audit logs instead of relying on device-held secrets.
How We Selected and Ranked These Tools
We evaluated each MFA platform by overall capability, features coverage, ease of use, and value fit based on the authentication and administration workflows it supports. We prioritized Conditional Access enforcement and phishing-resistant authentication options such as WebAuthn passkeys and FIDO2 security keys because these capabilities reduce credential theft risk during real-world sign-ins. Okta Workforce Identity Cloud separated itself by combining risk-based Conditional Access that triggers MFA from device posture plus phishing-resistant FastPass and WebAuthn support with centralized enrollment and lifecycle controls across workforce changes. Tools like Google Authenticator and FreeOTP scored lower for enterprise needs because they focus on offline TOTP generation with limited centralized administration and recovery automation.
Frequently Asked Questions About Multi Factor Authentication Software
Which multi factor authentication solution is best for policy-based MFA across many enterprise apps?
Okta Workforce Identity Cloud supports centralized MFA enrollment and conditional access policies that trigger MFA based on risk signals and device posture. Ping Identity adds configurable MFA policies in PingOne and PingAccess for orchestration across web, mobile, and enterprise applications.
What tool is strongest for phishing-resistant MFA methods like WebAuthn and security keys?
Microsoft Entra ID supports FIDO2 security keys and enables phishing-resistant authentication through Conditional Access. Auth0 also supports WebAuthn passkeys, and Okta Workforce Identity Cloud offers WebAuthn and phishing-resistant FastPass options.
Which platform handles conditional step-up MFA during sensitive actions instead of only at login?
Auth0 can require MFA at login or step up during sensitive actions using authentication policies and rules. ForgeRock Identity Platform supports risk-based evaluation hooks so step-up authentication triggers when sessions look suspicious.
Which option is best when you need a single workflow that chains multiple factors with authentication trees?
ForgeRock Identity Platform uses authentication trees to chain factors like WebAuthn, OTP, and out-of-band patterns based on policy and risk. Ping Identity focuses on context-aware authentication orchestration, which helps route users through stronger verification steps.
What multi factor authentication software is a good fit for VPN and administrator login protection?
Cisco Duo Security is built for MFA on VPN, web apps, and administrative logins with push approvals and one-time passcodes. Duo also provides adaptive policies driven by device trust and detailed access logs for investigations.
Which tool provides device posture and risk-driven enforcement with strong audit trails?
Microsoft Entra ID pairs Conditional Access with risk signals and device state requirements and produces reporting tied to authentication and policy decisions. Okta Workforce Identity Cloud similarly uses conditional access triggered by risk signals and device posture.
Which platform is best for developers that need MFA enforcement across web, mobile, and APIs?
Auth0 integrates MFA enforcement into a broader identity platform that supports web, mobile, and APIs with SDK-based user flows. ForgeRock Identity Platform also centralizes authentication and lifecycle flows across multiple channels, including MFA orchestration.
How do offline-friendly authenticator apps compare to enterprise MFA platforms for availability?
Google Authenticator and FreeOTP generate TOTP codes offline, which helps when network connectivity is intermittent. Enterprise platforms like Okta Workforce Identity Cloud and Microsoft Entra ID focus on centralized policy enforcement and device or risk context rather than offline-only code generation.
What is a practical starting point if you want OTP challenges with admin-managed controls without building custom logic?
SecurEnvoy supports OTP challenges and administrator-tailored verification links that target users, groups, and risk conditions. SuperOps also provides centralized MFA policy management and enrollment workflows designed to reduce helpdesk friction without heavy manual scripting.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Security alternatives
See side-by-side comparisons of security tools and pick the right one for your stack.
Compare security tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
