GITNUXSOFTWARE ADVICE
SecurityTop 10 Best Digital Risk Protection Software of 2026
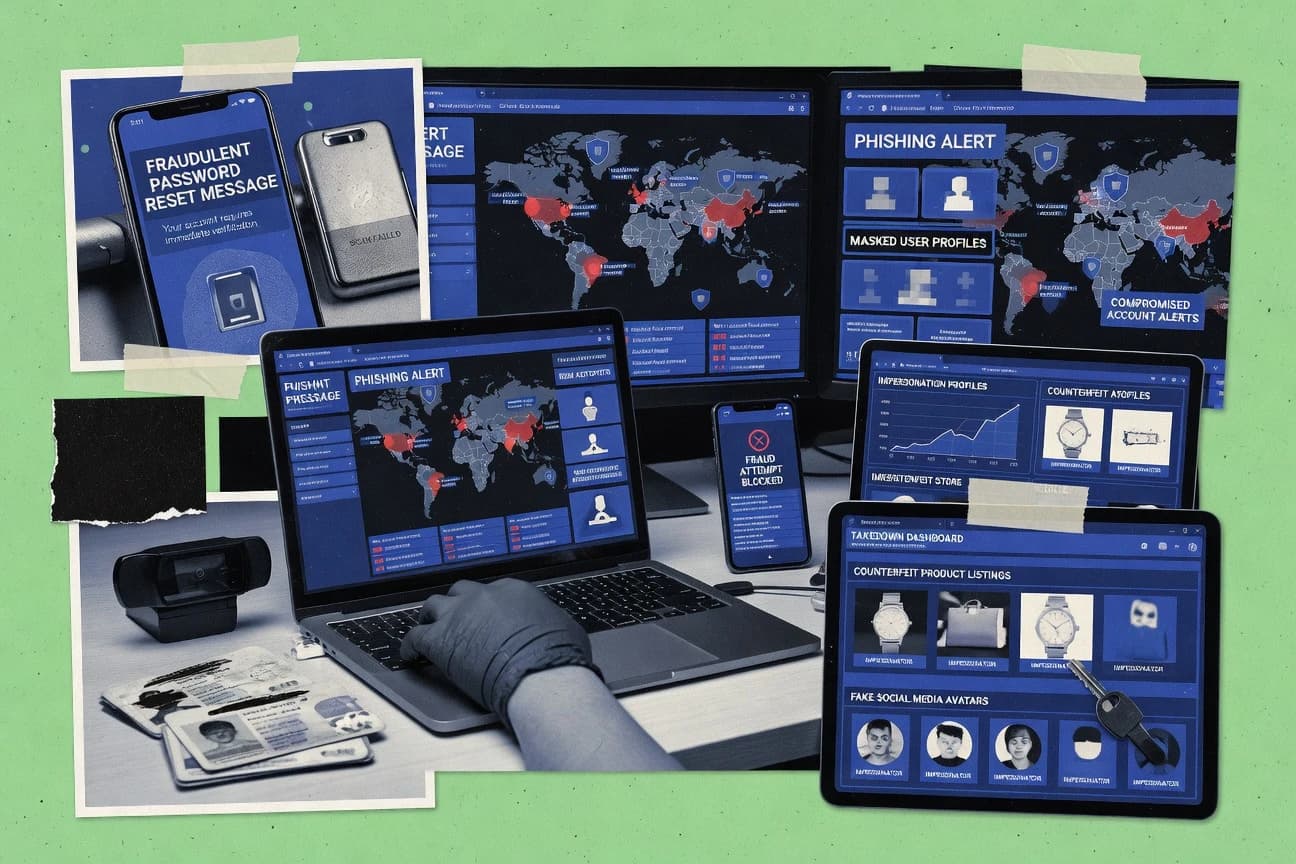
Explore the top 10 best digital risk protection software.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
Digital Shadows
Continuous monitoring and investigation across open web and dark web sources
Built for enterprises managing brand, customer, and exposure risk with analyst-led investigations.
Flashpoint
Investigation case management that ties alerts, evidence, and actions into one workflow
Built for enterprises needing investigative digital risk monitoring with case workflows.
Recorded Future
Intelligence graphs that visualize relationships behind digital risk findings
Built for enterprises needing intelligence-led monitoring for brand, vendors, and cyber risk.
Related reading
Comparison Table
This comparison table reviews digital risk protection software options used for monitoring, threat intelligence, and brand and impersonation exposure management. You will see how tools such as Digital Shadows, Flashpoint, Recorded Future, Brandwatch, and Palo Alto Networks Brand Protection differ in coverage, data sources, investigation workflows, and typical integrations for security and brand teams.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | Digital Shadows Digital Shadows provides digital risk monitoring across the web, dark web, and social channels with identity, fraud, and brand protection workflows. | enterprise MDR | 9.2/10 | 9.3/10 | 7.8/10 | 8.6/10 |
| 2 | Flashpoint Flashpoint delivers online risk intelligence with data collection from the open and deep web to support brand, fraud, and cyber threat response. | OSINT intelligence | 8.6/10 | 9.0/10 | 7.8/10 | 8.2/10 |
| 3 | Recorded Future Recorded Future offers threat intelligence that includes digital risk signals for brand monitoring, fraud indicators, and targeted actor exposure. | threat intel | 8.6/10 | 9.1/10 | 7.4/10 | 7.8/10 |
| 4 | Brandwatch Brandwatch provides social listening and risk monitoring to detect brand misuse, impersonation signals, and public sentiment shifts tied to digital risk. | social monitoring | 8.1/10 | 8.8/10 | 7.2/10 | 7.6/10 |
| 5 | Palo Alto Networks Brand Protection Palo Alto Networks Brand Protection monitors and identifies counterfeit and impersonation activity to support coordinated takedown and response. | brand enforcement | 8.0/10 | 8.6/10 | 7.3/10 | 7.2/10 |
| 6 | ZeroFox ZeroFox provides digital risk protection using detection and response for threats such as phishing, impersonation, and brand abuse across online channels. | automated takedown | 7.8/10 | 8.4/10 | 6.9/10 | 7.2/10 |
| 7 | Cymulate Cymulate runs continuous external attack surface testing to validate digital exposure, simulate abuse paths, and reduce risk from adversary activity. | attack surface testing | 8.2/10 | 9.0/10 | 7.6/10 | 7.7/10 |
| 8 | Barkly Barkly monitors leaked credentials, exposed personal data, and digital footprints to support identity and privacy risk reduction for individuals and organizations. | leak monitoring | 7.4/10 | 7.8/10 | 7.2/10 | 7.0/10 |
| 9 | RiskIQ RiskIQ monitors digital exposure by identifying assets, impersonation signals, and threat indicators to support brand and cyber risk reduction. | external exposure | 7.4/10 | 8.3/10 | 6.8/10 | 6.9/10 |
| 10 | ThreatConnect ThreatConnect centralizes threat intelligence and response workflows to help teams triage digital risk data and coordinate actions across environments. | security orchestration | 7.1/10 | 8.0/10 | 6.6/10 | 6.8/10 |
Digital Shadows provides digital risk monitoring across the web, dark web, and social channels with identity, fraud, and brand protection workflows.
Flashpoint delivers online risk intelligence with data collection from the open and deep web to support brand, fraud, and cyber threat response.
Recorded Future offers threat intelligence that includes digital risk signals for brand monitoring, fraud indicators, and targeted actor exposure.
Brandwatch provides social listening and risk monitoring to detect brand misuse, impersonation signals, and public sentiment shifts tied to digital risk.
Palo Alto Networks Brand Protection monitors and identifies counterfeit and impersonation activity to support coordinated takedown and response.
ZeroFox provides digital risk protection using detection and response for threats such as phishing, impersonation, and brand abuse across online channels.
Cymulate runs continuous external attack surface testing to validate digital exposure, simulate abuse paths, and reduce risk from adversary activity.
Barkly monitors leaked credentials, exposed personal data, and digital footprints to support identity and privacy risk reduction for individuals and organizations.
RiskIQ monitors digital exposure by identifying assets, impersonation signals, and threat indicators to support brand and cyber risk reduction.
ThreatConnect centralizes threat intelligence and response workflows to help teams triage digital risk data and coordinate actions across environments.
Digital Shadows
enterprise MDRDigital Shadows provides digital risk monitoring across the web, dark web, and social channels with identity, fraud, and brand protection workflows.
Continuous monitoring and investigation across open web and dark web sources
Digital Shadows specializes in digital risk protection through continuous discovery of exposed data, identities, and web assets across open and dark web sources. It supports threat visibility for brand and customer risk by linking findings to intelligence workflows that help teams prioritize remediation. The platform emphasizes investigation and monitoring use cases with case management, enrichment, and reporting for stakeholders. It is designed for organizations that need ongoing exposure management rather than one-time scans.
Pros
- Continuous exposure monitoring across open web and dark web sources
- Case management supports investigation workflows from discovery to remediation
- Strong identity and data leakage tracking for brand and customer risk
- Enrichment helps analysts connect findings to real-world context
Cons
- Setup and tuning often require analyst effort to reduce noise
- Core value depends on data source coverage and configuration choices
- User experience can feel heavy for teams focused on simple scanning
Best For
Enterprises managing brand, customer, and exposure risk with analyst-led investigations
More related reading
Flashpoint
OSINT intelligenceFlashpoint delivers online risk intelligence with data collection from the open and deep web to support brand, fraud, and cyber threat response.
Investigation case management that ties alerts, evidence, and actions into one workflow
Flashpoint focuses on digital risk protection using monitored sources like social media, web pages, and dark web leak locations. It provides alerting and investigations with case management so teams can track signals through resolution. Its workflows emphasize intelligence collection around brand, reputations, and adversarial activity rather than generic monitoring alone. Reporting supports stakeholder-ready summaries for investigations that need clear audit trails.
Pros
- Broad monitoring coverage including leak and threat relevant sources
- Case management helps teams centralize investigations and evidence
- Alerting supports fast triage for emerging brand and threat signals
- Investigation workflows provide clear tracking from detection to resolution
Cons
- Setup and query tuning take time for accurate signal quality
- Advanced investigation depth can feel heavy for small teams
- Costs can be high when only basic monitoring is needed
Best For
Enterprises needing investigative digital risk monitoring with case workflows
Recorded Future
threat intelRecorded Future offers threat intelligence that includes digital risk signals for brand monitoring, fraud indicators, and targeted actor exposure.
Intelligence graphs that visualize relationships behind digital risk findings
Recorded Future stands out for its intelligence-driven digital risk monitoring that connects threat signals to actionable context. It supports collection, enrichment, and analysis of open-source and proprietary data to surface risks tied to brands, vendors, and organizations. Teams can use risk scoring, intelligence graphs, and analyst workflows to investigate findings and track exposure trends over time.
Pros
- Actionable risk scoring for brand and cyber exposure monitoring
- Strong threat intelligence enrichment across open-source and proprietary signals
- Investigation workflows with context-rich intelligence graphs
Cons
- Analyst workflows feel heavy for small teams without dedicated analysts
- Integration and setup typically require skilled security or intelligence staff
- Cost can be high for organizations focused on limited monitoring needs
Best For
Enterprises needing intelligence-led monitoring for brand, vendors, and cyber risk
More related reading
Brandwatch
social monitoringBrandwatch provides social listening and risk monitoring to detect brand misuse, impersonation signals, and public sentiment shifts tied to digital risk.
Brandwatch Alerts for proactive monitoring of risk keywords, entities, and topics
Brandwatch stands out for combining social and digital media intelligence with digital risk workflows across the consumer web. It delivers advanced data collection, topic tracking, and audience analytics for monitoring reputational threats, emerging narratives, and harmful content patterns. Its governance and reporting capabilities support teams that need audit-ready evidence for brand safety and compliance actions. The platform’s breadth makes it strongest when risk teams can operationalize insights into investigations and escalation processes.
Pros
- Robust social and digital intelligence for early risk signal detection
- Strong query, taxonomy, and filtering for precise investigations
- Enterprise-grade reporting for compliance and stakeholder updates
Cons
- Setup and configuration are heavier than simpler brand safety tools
- Costs escalate quickly when scaling data sources and users
- Analyst-centric workflows can slow teams needing quick takedown actions
Best For
Enterprise digital risk teams monitoring narratives, brand safety, and compliance evidence
Palo Alto Networks Brand Protection
brand enforcementPalo Alto Networks Brand Protection monitors and identifies counterfeit and impersonation activity to support coordinated takedown and response.
Evidence-based investigation workflow for brand abuse cases using trademark-aware monitoring
Palo Alto Networks Brand Protection focuses on identifying and monitoring brand abuse across digital channels tied to your brand assets. It combines trademark-aware monitoring with workflow capabilities that help route findings to legal and security teams. The solution is built to integrate with Palo Alto Networks ecosystems, which supports broader security and risk operations. Brand Protection emphasizes evidence collection for investigations rather than only producing dashboards.
Pros
- Strong brand-abuse monitoring aligned to trademark and brand investigation workflows
- Evidence-focused reports support legal review and escalation decisions
- Integration fit with Palo Alto Networks security operations for end-to-end risk handling
Cons
- Workflow setup and tuning can be complex for teams without prior digital risk tooling
- Value depends on scale because monitoring outcomes often require more onboarding effort
- Less ideal as a standalone tool for non-enterprise brand programs
Best For
Enterprises needing trademark-aware digital brand monitoring with investigation-ready evidence
ZeroFox
automated takedownZeroFox provides digital risk protection using detection and response for threats such as phishing, impersonation, and brand abuse across online channels.
Digital impersonation monitoring with evidence-backed case workflows for brand abuse
ZeroFox stands out with a threat-intelligence approach that focuses on digital impersonation, brand abuse, and account risk across public internet signals. It provides monitoring for social platforms, domain and URL abuse, and exposed or compromised credentials tied to impersonation campaigns. The platform supports investigations and analyst workflows with case management, evidence capture, and prioritized remediation guidance. ZeroFox also emphasizes coordinated response by helping teams track activity over time and link related findings to reduce manual triage.
Pros
- Strong coverage for brand impersonation and social abuse signals
- Case management supports evidence collection and analyst-driven workflows
- Investigation views help connect related digital risk findings
- Monitoring can track domains, URLs, and public internet indicators
Cons
- Operational setup and workflow tuning can require specialist effort
- Reporting and dashboards feel less self-serve than simpler platforms
- Costs can be high for smaller teams with limited investigation volume
- Alert volumes can increase when monitoring is broadly configured
Best For
Security and risk teams reducing brand and account impersonation impact
More related reading
Cymulate
attack surface testingCymulate runs continuous external attack surface testing to validate digital exposure, simulate abuse paths, and reduce risk from adversary activity.
Cymulate Attack Simulation Platform with automated phishing simulations and measurable user impact
Cymulate stands out for running controlled, repeatable digital attack simulations that validate phishing, credential theft, and exposure paths. Its platform combines attack surface monitoring with automated test workflows and measurable outcomes for security awareness and incident readiness. Cymulate also supports reportable metrics that help track improvement across users, templates, and remediation cycles. The focus stays on simulation and visibility rather than providing a full SOC platform or ticketing suite.
Pros
- Automates end-to-end attack simulations with reusable templates and scheduled campaigns
- Provides measurable phishing outcomes with per-user and organizational reporting
- Validates exposure paths through controlled discovery and response testing
- Integrates with common identity and security workflows for smoother adoption
Cons
- Setup for realistic simulations can require security and email-system expertise
- Simulation coverage depends on external data sources and target configurations
- Reporting depth can feel complex without clear baseline benchmarks
- Cost grows with user count and campaign scale
Best For
Organizations validating phishing readiness and digital exposure using repeatable simulations
Barkly
leak monitoringBarkly monitors leaked credentials, exposed personal data, and digital footprints to support identity and privacy risk reduction for individuals and organizations.
Human-in-the-loop review and escalation workflows for digital risk alerts
Barkly stands out by combining digital risk monitoring with human-in-the-loop actions for brand and cyber exposure. It tracks mentions and risky content so teams can triage alerts and manage response workflows. The platform focuses on review, escalation, and reporting to support repeatable handling of emerging threats. Barkly is strongest for ongoing monitoring programs where teams need faster decisioning than manual scanning.
Pros
- Centralizes digital risk monitoring with triage workflows
- Supports structured review and escalation for faster responses
- Provides reporting to track issues and resolution outcomes
Cons
- Fewer advanced automation options than top-tier DDR suites
- Setup and tuning of monitoring rules takes operational time
- Reporting depth depends on how you model workflows
Best For
Teams running recurring brand and digital exposure monitoring with managed workflows
More related reading
RiskIQ
external exposureRiskIQ monitors digital exposure by identifying assets, impersonation signals, and threat indicators to support brand and cyber risk reduction.
Digital risk intelligence correlations for impersonation, phishing infrastructure, and external exposure
RiskIQ stands out for large-scale external attack surface and digital identity monitoring that focuses on real-world exposure signals. It provides brand and threat intelligence workflows that correlate findings across domains, assets, and abuse patterns. Its core strength is turning visibility from cybercrime, impersonation, and exposed infrastructure into prioritized risk cases for remediation teams.
Pros
- Extensive discovery for exposed digital assets across web and related sources
- Strong enrichment that links findings to brand impersonation and abuse patterns
- Case workflows support triage and handoff to remediation teams
- Threat intelligence context improves prioritization of risky exposures
Cons
- Setup complexity can slow time to first meaningful findings
- User experience feels geared to security analysts over casual reviewers
- Costs can be high for organizations needing only basic monitoring
- Customization effort is required to tune results for narrow scopes
Best For
Enterprises managing brand risk, impersonation, and external exposure across many assets
ThreatConnect
security orchestrationThreatConnect centralizes threat intelligence and response workflows to help teams triage digital risk data and coordinate actions across environments.
Case Management workflow that ties enriched threat intelligence to investigation tasks
ThreatConnect stands out with a case-driven threat intelligence workflow that connects enrichment, investigations, and response tasks in one place. The platform supports structured threat data, indicator management, and collaboration for security teams that need repeatable investigation processes. It also integrates with external feeds and other security tooling to accelerate triage and reduce manual coordination during digital risk activities.
Pros
- Case-centric workflows link intel enrichment to investigations
- Strong indicator and threat data management for team collaboration
- Integrations support faster enrichment and downstream security actions
Cons
- Digital risk use cases may require configuration and playbooks
- Workflow setup can be heavy for small teams with limited admins
- Enterprise pricing and scope can reduce cost predictability
Best For
Security teams automating threat intel investigations and digital risk workflows
Conclusion
After evaluating 10 security, Digital Shadows stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Digital Risk Protection Software
This buyer's guide explains how to select digital risk protection software using concrete evaluation signals from Digital Shadows, Flashpoint, Recorded Future, Brandwatch, Palo Alto Networks Brand Protection, ZeroFox, Cymulate, Barkly, RiskIQ, and ThreatConnect. It maps real capabilities like dark web exposure monitoring, investigation case management, intelligence graphs, and attack simulation to specific buying decisions. It also highlights common setup pitfalls like heavy analyst workflows and tuning effort so you can choose the right operational fit.
What Is Digital Risk Protection Software?
Digital risk protection software continuously discovers and monitors exposure across open web, deep web, and dark web signals tied to brand, customers, impersonation, leaked credentials, or threat infrastructure. These tools turn raw mentions, domains, URLs, identities, and assets into investigation-ready findings with enrichment, risk context, and escalation workflows. Teams use them to reduce fraud and impersonation impact, improve remediation prioritization, and document evidence for legal and compliance actions. In practice, Digital Shadows focuses on continuous exposure monitoring with open and dark web investigation workflows, while Flashpoint centers on alerting plus investigation case management that tracks signals to resolution.
Key Features to Look For
The right feature set determines whether you get actionable evidence and repeatable workflows or noisy alerts that demand heavy analyst tuning.
Continuous open and dark web exposure monitoring with investigation workflows
Choose tools that monitor continuously across open and dark web sources so findings stay current instead of relying on one-time scans. Digital Shadows is built around continuous monitoring and investigation across open web and dark web sources, and RiskIQ focuses on large-scale external attack surface and digital identity monitoring with correlations for impersonation and exposed infrastructure.
Case management that ties alerts, evidence, and actions into one workflow
Prioritize investigation workflows that keep evidence, enrichment, and resolution steps connected so handoffs do not lose context. Flashpoint delivers investigation case management that ties alerts, evidence, and actions into one workflow, and ThreatConnect provides a case-driven threat intelligence workflow that links enrichment to investigation tasks.
Intelligence enrichment and context models that make findings usable
Look for enrichment that connects findings to real-world context like actors, impersonation patterns, or relationships behind risk. Recorded Future emphasizes intelligence-driven monitoring with intelligence graphs that visualize relationships behind digital risk findings, and RiskIQ provides threat intelligence correlations that link exposures to impersonation, phishing infrastructure, and external exposure patterns.
Trademark-aware or brand-abuse evidence capture for takedown decisioning
If your workflow depends on legal review and escalation, require evidence-focused outputs and brand-abuse monitoring tied to your brand assets. Palo Alto Networks Brand Protection monitors counterfeit and impersonation activity with trademark-aware monitoring and produces evidence-based investigation workflow outputs, and ZeroFox supports digital impersonation monitoring with evidence-backed case workflows for brand abuse.
Proactive detection for brand risk keywords, entities, and topics
Use tools that support proactive monitoring around risk terms and entities so you catch narratives and impersonation signals early. Brandwatch Alerts deliver proactive monitoring of risk keywords, entities, and topics, while Brandwatch also provides governance and enterprise-grade reporting for stakeholder updates and compliance evidence.
Repeatable external attack validation through attack simulations
For organizations focused on proving phishing readiness and validating exposure paths, simulation capabilities provide measurable outcomes rather than only passive monitoring. Cymulate runs automated phishing simulations and attack simulations with reusable templates and per-user and organizational reporting, and it validates exposure paths through controlled discovery and response testing.
How to Choose the Right Digital Risk Protection Software
Pick the tool whose investigation and evidence workflow matches how your team actually triages, escalates, and documents risk.
Match monitoring depth to your threat surface needs
If your program must track ongoing exposure across open and dark web sources, evaluate Digital Shadows because it is built for continuous monitoring and investigation across open web and dark web sources. If your program centers on digital identity and external attack surface at scale, compare RiskIQ and its focus on correlated impersonation signals and exposed infrastructure. If you need investigative intelligence across open and deep web leaks with fast triage, Flashpoint aligns to alerting plus investigation case workflows.
Select a workflow model that fits your staffing and escalation process
For analyst-led programs that can tune signals, prioritize tools designed for case management and investigation evidence like Flashpoint and Digital Shadows. For teams with structured threat intelligence processes, ThreatConnect connects enrichment to investigation tasks in a repeatable case workflow. If you want evidence and legal-ready investigations around trademark-aware brand abuse, Palo Alto Networks Brand Protection is designed for that routed takedown and response workflow.
Verify enrichment and context capabilities match your prioritization style
If you make decisions using relationship context across findings, evaluate Recorded Future because its intelligence graphs visualize relationships behind digital risk findings. If you prioritize correlations that connect impersonation, phishing infrastructure, and exposure patterns, compare RiskIQ for its digital risk intelligence correlations. If your prioritization uses proactive topic and entity detection, Brandwatch Alerts for risk keywords and topics supports early signal detection.
Choose outputs that support takedown, escalation, and audits
If your team needs evidence packages for legal decisions and security escalation, focus on evidence-based investigation workflows like Palo Alto Networks Brand Protection and ZeroFox. If compliance reporting and audit-ready stakeholder updates drive adoption, Brandwatch delivers enterprise-grade reporting and governance oriented outputs. If you need faster human review and escalation decisions, Barkly emphasizes human-in-the-loop review and escalation workflows with structured review and reporting.
Add simulation only when you need measurable exposure validation
If your goal includes validating phishing paths and user impact with repeatable measurements, Cymulate provides automated phishing simulations with measurable per-user and organizational outcomes. If your primary need is ongoing detection of impersonation, leaked credentials, and threat signals, simulation-first tools will not replace case management workflows like those in Flashpoint and ThreatConnect.
Who Needs Digital Risk Protection Software?
Different digital risk teams need different mixes of monitoring, enrichment, case workflows, and evidence handling.
Enterprise teams running analyst-led brand, customer, and exposure investigations
Digital Shadows is a strong match for organizations managing brand, customer, and exposure risk with continuous monitoring and investigation across open web and dark web sources. Flashpoint is also a fit when investigative digital risk monitoring needs case workflows that tie alerts, evidence, and actions to resolution.
Enterprise intelligence teams that operationalize context-rich threat signals
Recorded Future fits teams needing intelligence-led monitoring for brand, vendors, and cyber risk with risk scoring and intelligence graphs for investigation context. RiskIQ fits programs that manage brand risk, impersonation, and external exposure across many assets using correlated intelligence tied to abuse patterns.
Brand safety, compliance, and narrative monitoring teams
Brandwatch fits teams monitoring narratives, brand misuse, impersonation signals, and sentiment shifts with proactive Brandwatch Alerts for risk keywords, entities, and topics. It is designed for enterprise reporting needs where governance and audit-ready evidence matter alongside investigations.
Organizations validating phishing readiness and exposure paths with repeatable tests
Cymulate is built for organizations validating phishing readiness using repeatable attack simulation campaigns with measurable user impact. It supports scheduled templates and outcome reporting to track improvement across users and remediation cycles.
Common Mistakes to Avoid
These pitfalls appear repeatedly across the top tools because many platforms need operational tuning to deliver signal quality and workflow efficiency.
Buying passive monitoring when your process requires case-driven evidence and resolution tracking
If you need proof for escalation and a closed loop from detection to resolution, avoid tools that do not center case workflows. Flashpoint ties alerts, evidence, and actions into one investigation workflow, and ThreatConnect links enrichment to investigation tasks through case management.
Underestimating tuning effort and noise reduction work
Tools that aim for deep coverage often require analyst effort to tune monitoring and reduce noise. Digital Shadows and Flashpoint both note that setup and tuning take analyst effort to improve signal quality, and Brandwatch also involves heavier setup and configuration when scaling monitoring precision.
Assuming investigation UX will be light without dedicated analysts
Platforms that provide context-rich workflows can feel heavy for small teams without dedicated analysts. Recorded Future and RiskIQ both emphasize that their analyst workflows and setup complexity can slow first meaningful outcomes when staffing is limited.
Skipping brand-abuse evidence needs for legal and security routing
If you require trademark-aware monitoring and evidence for legal escalation, avoid generic monitoring approaches. Palo Alto Networks Brand Protection is built around trademark-aware monitoring with evidence-based investigation workflows, and ZeroFox provides evidence-backed case workflows for digital impersonation and brand abuse.
How We Selected and Ranked These Tools
We evaluated Digital Shadows, Flashpoint, Recorded Future, Brandwatch, Palo Alto Networks Brand Protection, ZeroFox, Cymulate, Barkly, RiskIQ, and ThreatConnect across overall capability strength, features coverage, ease of use, and value fit for different operational models. We prioritized how directly each tool connects discovery to usable outcomes like investigation case management, evidence capture, intelligence enrichment, and relationship context. Digital Shadows separated itself by combining continuous exposure monitoring across open and dark web sources with case management and enrichment that supports investigation-to-remediation workflows. Tools lower in the set often mapped better to narrower workflows like simulations in Cymulate or human-in-the-loop review in Barkly, which can leave teams without the full investigation and enrichment depth they need.
Frequently Asked Questions About Digital Risk Protection Software
How do Digital Risk Protection tools differ in source coverage between open web, dark web, and social signals?
Digital Shadows focuses on continuous discovery across open and dark web sources and links findings to investigation workflows. Flashpoint and Brandwatch emphasize monitoring signals from social media and the consumer web. ZeroFox and RiskIQ also prioritize public internet signals that connect impersonation and exposed infrastructure to risk cases.
Which platforms are best for investigation case management instead of only alert dashboards?
Flashpoint provides case management that tracks signals from alerting through resolution with audit-ready reporting. Digital Shadows and ZeroFox support analyst workflows with enrichment and evidence capture inside investigation processes. ThreatConnect centralizes enrichment, indicator management, and response tasks so investigations stay structured and repeatable.
What solution fits organizations that need intelligence graphs or relationship mapping across risk entities?
Recorded Future stands out for intelligence graphs that visualize relationships behind digital risk findings. RiskIQ correlates exposure signals across domains and abuse patterns to produce prioritized risk cases. ThreatConnect complements this with structured threat data that supports repeatable investigation workflows.
Which tools are designed specifically for brand abuse and trademark-aware monitoring?
Palo Alto Networks Brand Protection monitors brand abuse with trademark-aware monitoring and routes evidence to legal and security workflows. Brandwatch focuses on reputational threats, emerging narratives, and harmful content patterns with governance and reporting. Cymulate does not target brand abuse directly because it emphasizes controlled attack simulations rather than brand enforcement evidence.
How do impersonation-focused platforms help teams reduce manual triage during emerging account or domain abuse?
ZeroFox concentrates on digital impersonation, domain and URL abuse, and exposed or compromised credentials linked to impersonation campaigns. RiskIQ correlates impersonation and phishing infrastructure signals across many external assets to prioritize remediation. ThreatConnect supports this with a case-driven workflow that ties enriched context to investigation tasks.
What should teams consider if their main goal is validating phishing readiness and exposure paths?
Cymulate is built for repeatable attack simulations that test phishing and credential theft scenarios with measurable outcomes. It pairs exposure monitoring with automated test workflows so teams can track improvement across templates and users. Digital Risk Protection platforms like Digital Shadows and Flashpoint focus on real-world discovery and investigation rather than simulated training outcomes.
Which solution supports human-in-the-loop review and faster escalation than manual scanning?
Barkly combines digital risk monitoring with human-in-the-loop review, escalation, and reporting workflows for brand and cyber exposure. It helps teams triage alerts and manage response actions without relying solely on manual scanning. Brandwatch provides proactive monitoring, but Barkly is oriented around managed review and escalation execution.
How do these tools integrate into existing security operations workflows and evidence collection processes?
Palo Alto Networks Brand Protection integrates with Palo Alto Networks ecosystems and emphasizes evidence collection for brand abuse investigations. ThreatConnect integrates with external feeds and other security tooling to accelerate triage and reduce coordination overhead. Flashpoint and ZeroFox both support evidence capture in case workflows so findings connect to remediation actions.
What common problem do teams face when investigating digital exposure, and how do leading tools address it?
A common bottleneck is scattered evidence and context that forces analysts to rebuild the story manually. Flashpoint addresses this by linking alerts, evidence, and actions inside case management. Digital Shadows and RiskIQ use enrichment and correlation to connect exposed assets, identities, and abuse patterns into prioritized investigations.
What’s the fastest way to start a digital risk monitoring program using these platforms?
Start by selecting monitoring coverage that matches your risk model and then run investigation workflows on discovered entities. Digital Shadows and RiskIQ support continuous discovery and correlation so teams can translate exposure signals into risk cases quickly. For teams that need social and narrative monitoring, Brandwatch Alerts provides proactive tracking of risk keywords, entities, and topics before escalation.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Security alternatives
See side-by-side comparisons of security tools and pick the right one for your stack.
Compare security tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.