GITNUXSOFTWARE ADVICE
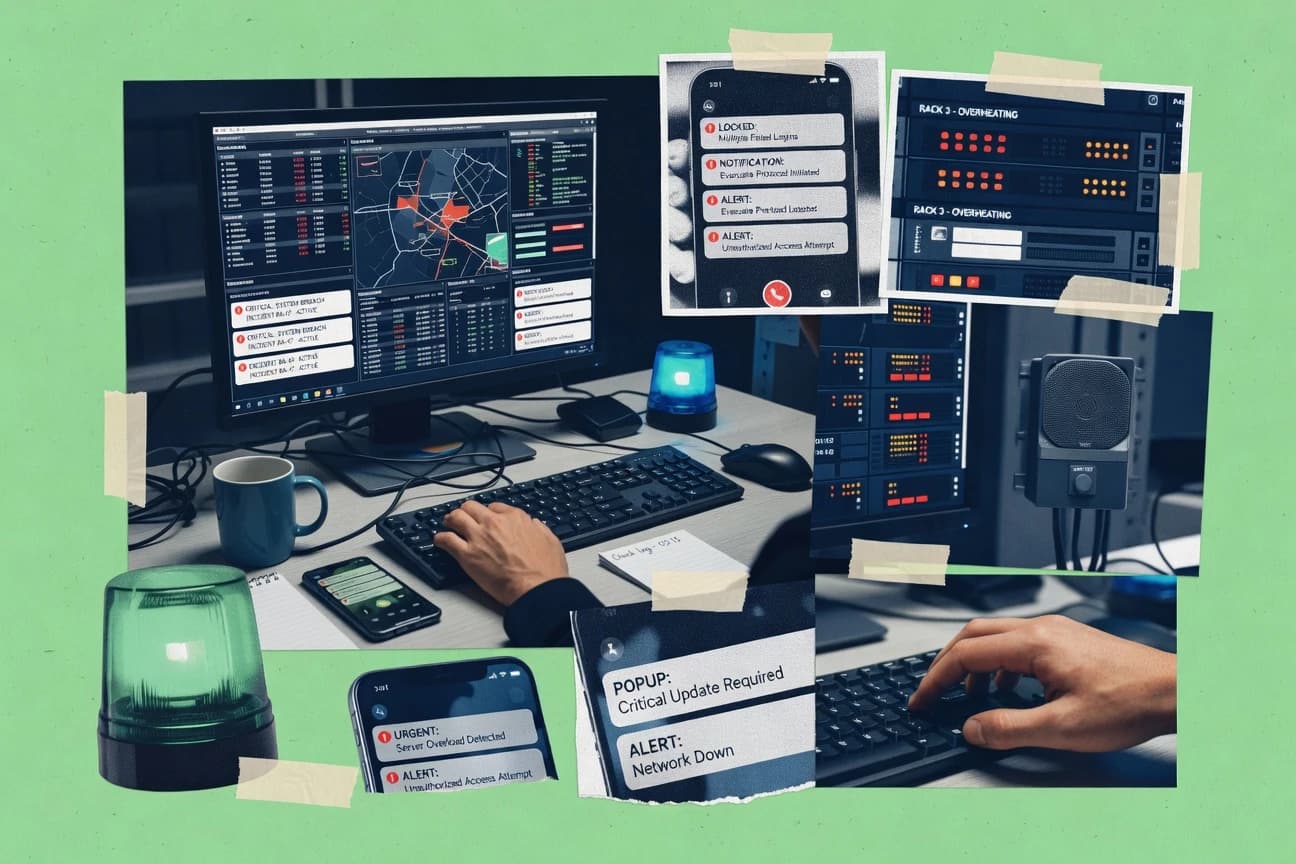
Technology Digital MediaTop 10 Best Alert Software of 2026
Discover top 10 alert software solutions to stay informed.
How we ranked these tools
Core product claims cross-referenced against official documentation, changelogs, and independent technical reviews.
Analyzed video reviews and hundreds of written evaluations to capture real-world user experiences with each tool.
AI persona simulations modeled how different user types would experience each tool across common use cases and workflows.
Final rankings reviewed and approved by our editorial team with authority to override AI-generated scores based on domain expertise.
Score: Features 40% · Ease 30% · Value 30%
Gitnux may earn a commission through links on this page — this does not influence rankings. Editorial policy
Editor picks
Three quick recommendations before you dive into the full comparison below — each one leads on a different dimension.
PagerDuty
Escalation policies that automatically route incidents across on-call rotations
Built for teams that need reliable alert-to-incident workflows with clear ownership.
Splunk On-Call
Alert-to-incident automation powered by Splunk alert inputs and escalation policies
Built for operations teams using Splunk to automate alert triage and escalation.
Datadog Monitor Alerts
Composite monitors with multiple conditions and logical functions
Built for operations and engineering teams needing observability-driven alerting at scale.
Comparison Table
This comparison table reviews Alert Software options alongside major incident and monitoring platforms such as PagerDuty, Splunk On-Call, Datadog Monitor Alerts, New Relic Alerts, and VictorOps. It highlights how each tool handles alert routing, escalation and on-call workflows, integrations, and operational visibility so you can match capabilities to your alerting and incident response requirements.
| # | Tool | Category | Overall | Features | Ease of Use | Value |
|---|---|---|---|---|---|---|
| 1 | PagerDuty PagerDuty detects incidents from alerts and routes them to the right teams with automated escalation, on-call scheduling, and incident workflows. | enterprise incident response | 9.3/10 | 9.4/10 | 8.4/10 | 8.6/10 |
| 2 | Splunk On-Call Splunk On-Call delivers intelligent alert routing and incident management using alert sources from Splunk and integrated monitoring systems. | alert routing | 8.4/10 | 8.8/10 | 7.6/10 | 7.9/10 |
| 3 | Datadog Monitor Alerts Datadog monitors and alerting evaluate metrics, logs, and traces with rule-based notifications and automated escalation. | monitoring and alerting | 8.4/10 | 9.3/10 | 7.8/10 | 7.6/10 |
| 4 | New Relic Alerts New Relic Alerts correlates performance signals across apps and infrastructure to trigger alerts and automate response workflows. | observability alerting | 8.3/10 | 8.9/10 | 7.6/10 | 8.0/10 |
| 5 | VictorOps VictorOps provides on-call alerting, routing, and incident management workflows that integrate with monitoring tools. | on-call management | 7.8/10 | 8.3/10 | 7.2/10 | 7.4/10 |
| 6 | Opsgenie Opsgenie centralizes alert management with rules, escalation policies, and scheduling for reliable on-call handling. | on-call escalation | 7.6/10 | 8.3/10 | 7.1/10 | 7.2/10 |
| 7 | Grafana Alerting Grafana Alerting evaluates dashboard rules and sends notifications through multiple channels with configurable routing. | open alerting | 7.6/10 | 8.2/10 | 7.2/10 | 7.4/10 |
| 8 | Zabbix Zabbix monitors infrastructure and applications, generates alerts on triggers, and notifies teams through built-in and external integrations. | open-source monitoring | 7.4/10 | 8.3/10 | 6.6/10 | 7.8/10 |
| 9 | Prometheus Alertmanager Alertmanager groups, deduplicates, and routes Prometheus alerts to notification endpoints with inhibition and silencing controls. | alert aggregation | 7.6/10 | 8.1/10 | 6.9/10 | 8.6/10 |
| 10 | Uptime Kuma Uptime Kuma monitors websites and services, triggers status alerts, and sends notifications for downtime events. | self-hosted uptime alerts | 6.6/10 | 7.2/10 | 7.6/10 | 7.4/10 |
PagerDuty detects incidents from alerts and routes them to the right teams with automated escalation, on-call scheduling, and incident workflows.
Splunk On-Call delivers intelligent alert routing and incident management using alert sources from Splunk and integrated monitoring systems.
Datadog monitors and alerting evaluate metrics, logs, and traces with rule-based notifications and automated escalation.
New Relic Alerts correlates performance signals across apps and infrastructure to trigger alerts and automate response workflows.
VictorOps provides on-call alerting, routing, and incident management workflows that integrate with monitoring tools.
Opsgenie centralizes alert management with rules, escalation policies, and scheduling for reliable on-call handling.
Grafana Alerting evaluates dashboard rules and sends notifications through multiple channels with configurable routing.
Zabbix monitors infrastructure and applications, generates alerts on triggers, and notifies teams through built-in and external integrations.
Alertmanager groups, deduplicates, and routes Prometheus alerts to notification endpoints with inhibition and silencing controls.
Uptime Kuma monitors websites and services, triggers status alerts, and sends notifications for downtime events.
PagerDuty
enterprise incident responsePagerDuty detects incidents from alerts and routes them to the right teams with automated escalation, on-call scheduling, and incident workflows.
Escalation policies that automatically route incidents across on-call rotations
PagerDuty stands out for workflow-driven incident management that turns alerts into accountable response tasks. It delivers multi-channel alerting, escalation policies, and on-call scheduling that route incidents until resolution. Integrations with common monitoring tools and collaboration systems support automated triage and faster handoffs. Its reporting and incident timelines help teams analyze alert noise and improve runbooks over time.
Pros
- Robust orchestration with escalation chains and on-call handoffs
- Deep integrations with monitoring, cloud, and ticketing workflows
- Strong incident timelines and reporting for post-incident analysis
Cons
- Setup complexity increases with advanced routing and large teams
- Alert noise control depends on careful configuration and tuning
- Cost grows quickly when adding more users and integrations
Best For
Teams that need reliable alert-to-incident workflows with clear ownership
Splunk On-Call
alert routingSplunk On-Call delivers intelligent alert routing and incident management using alert sources from Splunk and integrated monitoring systems.
Alert-to-incident automation powered by Splunk alert inputs and escalation policies
Splunk On-Call stands out for pairing Splunk data with real-time incident workflows and on-call escalation. It routes alerts to the right responder using team schedules, rotations, and escalation policies, with support for acknowledgement and status updates. It integrates with common paging and notification channels to reduce time to acknowledgement for alert-driven operations. It is strongest for organizations already using Splunk Enterprise or Splunk Observability Cloud to operationalize telemetry into actionable incidents.
Pros
- Uses Splunk alerts to drive incident creation and routing
- Supports rotations, schedules, and escalation policies for correct ownership
- Keeps responders aligned with acknowledgement and incident status updates
- Integrates with paging and notification systems for fast escalation
Cons
- Setup complexity is higher when teams need custom routing logic
- Best results depend on having strong Splunk alert definitions
Best For
Operations teams using Splunk to automate alert triage and escalation
Datadog Monitor Alerts
monitoring and alertingDatadog monitors and alerting evaluate metrics, logs, and traces with rule-based notifications and automated escalation.
Composite monitors with multiple conditions and logical functions
Datadog Monitor Alerts stands out for turning live observability data into actionable alerting across metrics, logs, traces, and infrastructure signals. You can build monitors with threshold logic, anomaly detection, event-based triggers, and composite logic to reduce noisy alerts. The platform supports alert routing, notification controls, and escalation policies tied to teams and services. Built-in dashboards and correlation workflows help you move from alert to investigation without switching tools.
Pros
- Composite monitors combine multiple conditions to cut alert noise
- Anomaly detection helps detect unusual behavior beyond fixed thresholds
- Alert routing supports schedules, grouping, and escalation policies
- Unified correlation across metrics, logs, and traces speeds triage
- SLA-style monitor testing and notification previews reduce surprises
Cons
- Monitor setup can get complex for large organizations and estates
- High-cardinality environments can drive monitoring costs upward
- Learning curve is steeper than simpler alerting tools
- Alert tuning often requires iterative maintenance and ownership
Best For
Operations and engineering teams needing observability-driven alerting at scale
New Relic Alerts
observability alertingNew Relic Alerts correlates performance signals across apps and infrastructure to trigger alerts and automate response workflows.
Entity-scoped alert conditions with grouping and routing built around New Relic observability data
New Relic Alerts ties alerting directly to New Relic observability data from APM, infrastructure, and logs. It supports threshold alerts, anomaly-style conditions, and flexible grouping so you can route issues by service, environment, or other entity dimensions. Alert channels include email, webhooks, and integrations with tools like Slack and PagerDuty for incident workflows. The alert lifecycle ties into New Relic’s incident management so responders can acknowledge, resolve, and track recurring problems.
Pros
- Alert rules evaluate across APM, infrastructure, and log signals in one system
- Routing and grouping support service and environment-based alert strategies
- Incident-style workflows include acknowledge and resolve states
- Webhook and integration options enable fast handoffs to ticketing and on-call tools
Cons
- Advanced alert logic requires familiarity with New Relic query language and entities
- High alert volume can increase operational overhead without strong noise controls
Best For
Teams standardizing on New Relic for alerting, incident response, and noise reduction
VictorOps
on-call managementVictorOps provides on-call alerting, routing, and incident management workflows that integrate with monitoring tools.
Splunk alert to on-call escalation with incident timelines and status-aware handoffs
VictorOps stands out for incident-centric alert routing that focuses on on-call engagement and fast escalation paths. The platform integrates with Splunk so alert conditions can trigger paging, status-aware handoffs, and operational workflows across teams. It also emphasizes incident timelines and bi-directional updates to keep responders aligned during active events.
Pros
- Tight Splunk integration for alert-to-incident workflows
- On-call aware escalation with paging and responder handoffs
- Incident timelines support clearer post-incident investigation
- Status updates keep teams synchronized during active alerts
Cons
- Setup and tuning require careful alert and routing configuration
- Advanced operational workflows can feel complex for smaller teams
- Value drops when you rely on non-Splunk alert sources
Best For
Operations teams using Splunk that need fast alert escalation and incident timelines
Opsgenie
on-call escalationOpsgenie centralizes alert management with rules, escalation policies, and scheduling for reliable on-call handling.
SLA-based escalation with scheduled on-call rotations and escalation chains
Opsgenie’s alert routing and incident workflows stand out because they integrate alert suppression, escalation logic, and on-call collaboration in one place. It supports deduplication, grouping, and SLA-based escalation so alerts turn into timed responses instead of noisy tickets. Automated routing with policies, schedules, and integrations with major monitoring and ticketing systems helps teams reduce manual triage. Incident timelines and post-incident actions support operational reviews once the alert storm ends.
Pros
- Sophisticated escalation policies with schedules, rotations, and overrides
- Strong alert deduplication, grouping, and noise-reduction controls
- Automation ties monitoring alerts to incidents and on-call workflows
- Clear incident timelines and handoffs across teams
Cons
- Routing setup complexity increases with multi-team alert ownership models
- Advanced governance features require deliberate configuration
- Operational overhead grows with many integrations and escalation paths
Best For
Operations teams needing SLA escalations and automated alert-to-incident routing
Grafana Alerting
open alertingGrafana Alerting evaluates dashboard rules and sends notifications through multiple channels with configurable routing.
Notification policies with contact points enable routing by labels and grouping.
Grafana Alerting stands out by unifying alert rules for dashboards and data sources inside Grafana, with a central alerting engine and routing. It supports alert evaluation on schedules, multi-dimensional queries, and configurable notification policies that send alerts to common endpoints. It also includes alert state management with deduplication, silences, and integration with Grafana OnCall and other contact points. The tight Grafana coupling makes deployment and governance straightforward when your observability stack is Grafana-first.
Pros
- Centralized alert rules and routing inside Grafana
- Notification policies with contact points for multiple destinations
- Alert state tracking with silences and deduplication
Cons
- Complex rule evaluation and routing can slow initial setup
- Grafana-first workflow limits fit for non-Grafana stacks
- Advanced multi-team governance needs careful configuration
Best For
Teams using Grafana for monitoring that want integrated alert routing and state control
Zabbix
open-source monitoringZabbix monitors infrastructure and applications, generates alerts on triggers, and notifies teams through built-in and external integrations.
Trigger-based alerting with calculated expressions and event-driven escalation via actions
Zabbix stands out with deep, agent-based monitoring and alerting tuned for large-scale infrastructure. It generates alerts from server, host, and service metrics using triggers that you can calculate and route to multiple endpoints. It also supports automation with event correlation, acknowledgements, and recurring maintenance windows. You get strong alert logic and visibility, but the configuration-heavy setup can slow down teams that need rapid deployment.
Pros
- Highly configurable trigger expressions for complex alert conditions
- Supports agent, SNMP, and log monitoring for broad infrastructure coverage
- Multi-step alert escalation with actions tied to event lifecycle
- Event correlation and maintenance windows reduce noise and false positives
- Built-in dashboards and history for alert context and troubleshooting
Cons
- UI configuration and trigger tuning demand sustained admin effort
- Alert routing setup can feel complex for teams new to Zabbix concepts
- Scaling advanced environments requires careful sizing and monitoring of Zabbix itself
Best For
Large infrastructure teams needing configurable alert logic without external tooling
Prometheus Alertmanager
alert aggregationAlertmanager groups, deduplicates, and routes Prometheus alerts to notification endpoints with inhibition and silencing controls.
Alert inhibition rules that automatically suppress lower-priority alerts from higher-priority states
Prometheus Alertmanager routes and deduplicates Prometheus alerts through configurable alert receivers. It supports alert grouping, inhibition rules, and silence management to reduce noisy notifications. Core capabilities include configurable routing trees, webhook and email-style integrations, and templated notification content. It is strongest for teams already operating Prometheus and needing deterministic alert delivery behavior.
Pros
- Powerful routing tree with grouping to control alert fanout
- Built-in inhibition rules suppress downstream alerts from upstream conditions
- Deduplication and silence features reduce notification noise effectively
- Template-based notifications produce consistent messages per alert
Cons
- Configuration-heavy YAML makes complex routing hard to maintain
- UI is minimal, so operational workflows rely on API and logs
- Limited incident management features beyond silences and routing
- Not a general monitoring replacement for alert source logic
Best For
Teams using Prometheus needing reliable routing and noise control for alerts
Uptime Kuma
self-hosted uptime alertsUptime Kuma monitors websites and services, triggers status alerts, and sends notifications for downtime events.
Unified monitor dashboard plus downtime history with per-service alert thresholds and notifications.
Uptime Kuma stands out for its self-hosted status monitoring that turns simple pings into a real-time dashboard. It supports many alert sources and notification channels, including email, webhooks, and push-based options, so you can route incidents to your tools. The tool provides downtime tracking, uptime history charts, and per-monitor settings that make it practical for multiple services. Its main limitation is that you manage the servers and integrations yourself when you choose self-hosting.
Pros
- Self-hosted web UI shows live monitor status and historical uptime charts
- Flexible alerting with integrations like email and webhooks for incident routing
- Supports multiple monitor types such as HTTP, ping, and keyword checks
- Granular per-service settings for intervals, retries, and alerting behavior
Cons
- No built-in incident management workflow like tickets and escalation rules
- Self-hosted setup adds operational overhead for hosting and updates
- Alert logic is simpler than advanced monitoring platforms with rich analytics
- Large fleets can require careful tuning of intervals and retry thresholds
Best For
Small teams running self-hosted uptime monitoring with webhook-driven alerts
Conclusion
After evaluating 10 technology digital media, PagerDuty stands out as our overall top pick — it scored highest across our combined criteria of features, ease of use, and value, which is why it sits at #1 in the rankings above.
Use the comparison table and detailed reviews above to validate the fit against your own requirements before committing to a tool.
How to Choose the Right Alert Software
This buyer's guide helps you choose Alert Software by mapping alert sources to incident workflows, routing rules, and responder handoffs. It covers PagerDuty, Splunk On-Call, Datadog Monitor Alerts, New Relic Alerts, VictorOps, Opsgenie, Grafana Alerting, Zabbix, Prometheus Alertmanager, and Uptime Kuma. Use it to identify the right platform for your observability stack and operational model.
What Is Alert Software?
Alert software turns monitoring signals like thresholds and uptime checks into notifications that reach the right people with clear ownership. It solves problems like alert noise, slow acknowledgement, unclear escalation paths, and missing context during incident response. Tools like PagerDuty focus on incident workflows with escalation policies that route across on-call rotations. Tools like Prometheus Alertmanager focus on routing, inhibition, deduplication, and silences so notification fanout stays controlled.
Key Features to Look For
These capabilities determine whether alerts become actionable response tasks or stay as noisy notifications.
Alert-to-incident escalation workflows
PagerDuty excels at escalation policies that automatically route incidents across on-call rotations. Opsgenie adds SLA-based escalation with scheduled on-call rotations and escalation chains that turn alerts into timed responses.
SLA-driven scheduling, rotations, and responder ownership
Opsgenie supports scheduling, rotations, and escalation overrides so ownership stays consistent during changing coverage. PagerDuty routes incidents to the right teams using on-call scheduling and escalation policies.
Noise control with deduplication, grouping, silences, and inhibition
Opsgenie provides alert deduplication, grouping, and noise-reduction controls so alerts turn into fewer actionable incidents. Prometheus Alertmanager adds inhibition rules that suppress downstream alerts and includes silence management plus alert grouping and deduplication.
Multi-source observability correlation across metrics, logs, and traces
Datadog Monitor Alerts evaluates alerts across metrics, logs, and traces with composite monitors and logical functions. New Relic Alerts correlates performance signals across APM, infrastructure, and logs with entity-scoped grouping and routing.
Platform-native alert logic and state management
Grafana Alerting unifies alert rules for dashboards and data sources inside Grafana with a central alerting engine. Grafana Alerting also includes alert state management with deduplication and silences and supports routing through notification policies and contact points.
Event-driven automation for infrastructure monitoring
Zabbix generates alerts from server, host, and service triggers with calculated expressions and event correlation. It supports multi-step alert escalation with actions tied to an event lifecycle and recurring maintenance windows to reduce false positives.
How to Choose the Right Alert Software
Pick a tool by matching your alert source system, your required escalation behavior, and your tolerance for configuration complexity.
Start with your alert source and data model
If your organization already operationalizes telemetry through Splunk, Splunk On-Call drives alert-to-incident automation using Splunk alert inputs and escalation policies. If you are Grafana-first for monitoring, Grafana Alerting centralizes dashboard rule evaluation and routes notifications with contact points.
Choose an incident workflow model that fits your team coverage
For teams that need reliable escalation that keeps routing active until resolution, PagerDuty orchestrates escalation chains across on-call rotations. If you need SLA-based escalation with scheduled rotations and escalation chains, Opsgenie provides the scheduling backbone for time-bound responses.
Design for noise reduction before you scale alert volume
Use Datadog Monitor Alerts composite monitors with multiple conditions and logical functions to cut alert noise and reduce noisy notifications. Use Prometheus Alertmanager inhibition rules to suppress lower-priority alerts from higher-priority states and manage silences to control fanout.
Map grouping and routing to the ownership units you actually use
Use New Relic Alerts entity-scoped alert conditions with grouping and routing by service, environment, or other entity dimensions. Use Zabbix trigger expressions and action-based escalation so alerts route based on calculated trigger states across hosts and services.
Validate integration depth with your operational endpoints
PagerDuty supports multi-channel alerting and deep integrations with monitoring and collaboration systems to speed handoffs. New Relic Alerts includes email, webhooks, and integrations like Slack and PagerDuty so alert lifecycle actions include acknowledge and resolve workflows.
Who Needs Alert Software?
Alert software fits teams that must respond quickly to operational issues and coordinate ownership across teams and time zones.
Teams that need reliable alert-to-incident workflows with clear ownership
PagerDuty is the best fit for teams that require escalation policies that automatically route incidents across on-call rotations until resolution. PagerDuty also emphasizes incident workflows with incident timelines and reporting so responders can analyze alert noise and improve runbooks.
Operations teams using Splunk for automated alert triage and escalation
Splunk On-Call is built to use Splunk alerts as inputs for alert-to-incident automation with rotations, schedules, and escalation policies. VictorOps also focuses on Splunk alert-to-on-call escalation with incident timelines and status-aware handoffs.
Operations and engineering teams needing observability-driven alerting at scale
Datadog Monitor Alerts targets teams that evaluate monitors across metrics, logs, and traces with composite monitors and anomaly detection. New Relic Alerts supports correlated alerting across APM, infrastructure, and logs with entity-scoped routing for service and environment strategies.
Large infrastructure teams needing configurable alert logic without external tooling
Zabbix is designed for large infrastructure monitoring that relies on trigger expressions, event correlation, and actions tied to event lifecycle. It supports agent, SNMP, and log monitoring and includes maintenance windows and alert escalation steps.
Common Mistakes to Avoid
These mistakes repeatedly lead to slow onboarding, noisy alerting, and weak operational ownership.
Choosing a tool without matching your alert source system
Splunk-centric teams get better alignment with Splunk On-Call and VictorOps because both drive workflows from Splunk alerts. Grafana-first teams get a smoother governance path with Grafana Alerting because alert rules and routing are centralized inside Grafana.
Scaling alert volume without implementing noise suppression
Datadog Monitor Alerts uses composite monitors and anomaly detection to reduce noisy alerts, but you still need deliberate monitor design for large estates. Prometheus Alertmanager uses grouping, deduplication, inhibition rules, and silences, so skipping these controls leads to alert fanout.
Relying on routing alone when escalation and handoffs are missing
Opsgenie is strong when you need SLA-based escalation and scheduled rotations that turn alerts into timed responses. PagerDuty provides escalation chains and on-call handoffs, so routing without these escalation behaviors stalls incident resolution.
Underestimating configuration effort for advanced routing and complex rule evaluation
PagerDuty setup complexity increases with advanced routing and large team models, which can slow initial deployment. Grafana Alerting and Zabbix can also require sustained configuration effort when multi-dimensional routing or complex trigger expressions are used heavily.
How We Selected and Ranked These Tools
We evaluated PagerDuty, Splunk On-Call, Datadog Monitor Alerts, New Relic Alerts, VictorOps, Opsgenie, Grafana Alerting, Zabbix, Prometheus Alertmanager, and Uptime Kuma using overall capability strength, feature depth, ease of use, and value for operational teams. We prioritized products that convert alerts into accountable response workflows with escalation policies, scheduling, grouping, and state management. PagerDuty separated itself by combining escalation policies that route across on-call rotations with strong incident workflows and incident timelines for post-incident analysis. We also weighed how quickly teams can get value, since tools like Prometheus Alertmanager rely on configuration-heavy YAML routing behavior and tools like Grafana Alerting depend on Grafana-first deployment patterns.
Frequently Asked Questions About Alert Software
How do PagerDuty and Opsgenie turn raw alerts into actionable incidents?
PagerDuty routes incidents using escalation policies and on-call scheduling until resolution, and it records incident timelines for later analysis. Opsgenie combines deduplication, grouping, and SLA-based escalation so alerts become timed responses through automated routing policies and schedules.
Which alerting tool is best for teams that already run Splunk Enterprise or Splunk Observability Cloud?
Splunk On-Call is strongest when alerting starts from Splunk alert inputs, because it uses team schedules, rotations, and escalation policies to route acknowledgements and status updates. VictorOps also integrates with Splunk, but its focus centers on incident timelines and status-aware handoffs tied to fast escalation paths.
What platform reduces alert noise using composite logic and anomaly-style detection?
Datadog Monitor Alerts supports composite monitors with multiple conditions and logical functions, which helps suppress noisy signals with threshold logic and anomaly-style triggers. Prometheus Alertmanager also reduces noise by routing with alert grouping and by enforcing inhibition rules that silence lower-priority alerts when a higher-priority alert is active.
How do Grafana Alerting and Prometheus Alertmanager differ in how they manage alert state?
Grafana Alerting manages alert evaluation and state inside Grafana, including deduplication and silences tied to the Grafana alerting engine and configurable notification policies. Prometheus Alertmanager manages routing and noise control for Prometheus alerts, including silence management, templated notifications, and deterministic behavior via routing trees.
Which tools support routing alerts into existing collaboration and incident workflows?
New Relic Alerts sends alerts through channels like email and webhooks and integrates with tools such as Slack and PagerDuty for incident workflows. Opsgenie also integrates with common monitoring and ticketing systems and keeps responders aligned using incident timelines and post-incident actions.
How should teams handle alert suppression and maintenance windows across systems?
Zabbix supports recurring maintenance windows and event correlation, and it can drive automated actions that include acknowledgements during planned disruptions. Prometheus Alertmanager provides inhibition rules and silences to suppress noisy notifications, while Grafana Alerting provides silences and label-based routing via notification policies and contact points.
What is the practical difference between entity-scoped alert routing in New Relic and label-based routing in Grafana?
New Relic Alerts groups and routes by entity dimensions such as service and environment so responders can focus on the exact context of an issue. Grafana Alerting routes alerts using labels and grouping rules via notification policies and contact points, which is tightly coupled to how your monitors live in Grafana.
Which tools are strongest for infrastructure-heavy environments that need agent-based monitoring and calculated trigger expressions?
Zabbix is built for large-scale infrastructure using agent-based monitoring and calculated trigger expressions with server, host, and service metrics. Prometheus Alertmanager complements Prometheus-based infrastructure monitoring by focusing on alert routing, deduplication, and suppression rules rather than agent-based collection.
If you need self-hosted uptime dashboards with actionable alerts, what should you look at?
Uptime Kuma provides a self-hosted status dashboard built from pings and supports downtime tracking plus uptime history charts per monitor. It also sends alerts through channels like email and webhooks, so you can route availability incidents directly into your alert receivers.
What is a good first setup path for teams trying to operationalize telemetry into alerts without manual triage?
Datadog Monitor Alerts starts from metrics, logs, and traces and moves from alert to investigation within the same platform using built-in dashboards and correlation workflows. Grafana Alerting is a strong next step for Grafana-first teams because it unifies alert rules for dashboards and data sources and applies notification policies that route alerts to configured endpoints.
Tools reviewed
Referenced in the comparison table and product reviews above.
Keep exploring
Comparing two specific tools?
Software Alternatives
See head-to-head software comparisons with feature breakdowns, pricing, and our recommendation for each use case.
Explore software alternatives→In this category
Technology Digital Media alternatives
See side-by-side comparisons of technology digital media tools and pick the right one for your stack.
Compare technology digital media tools→FOR SOFTWARE VENDORS
Not on this list? Let’s fix that.
Our best-of pages are how many teams discover and compare tools in this space. If you think your product belongs in this lineup, we’d like to hear from you—we’ll walk you through fit and what an editorial entry looks like.
Apply for a ListingWHAT THIS INCLUDES
Where buyers compare
Readers come to these pages to shortlist software—your product shows up in that moment, not in a random sidebar.
Editorial write-up
We describe your product in our own words and check the facts before anything goes live.
On-page brand presence
You appear in the roundup the same way as other tools we cover: name, positioning, and a clear next step for readers who want to learn more.
Kept up to date
We refresh lists on a regular rhythm so the category page stays useful as products and pricing change.
